Recommended courses on Validate verification
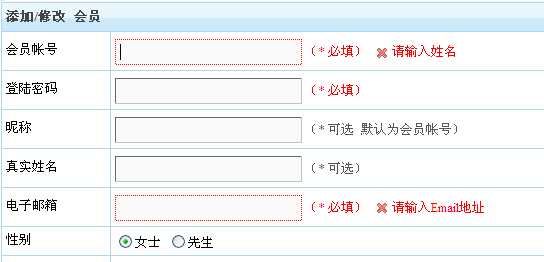
One of the powerful features of yii2 is its Form component, which is both convenient and safe. Some friends feel that after using Yii for a while, it seems to be nothing but "difficult to understand" than TP. The leader arranged for a registration function, but this guy used Baidu's various good form styles, and Baidu's validate verification. I really felt sorry for this guy. Of course, without further ado, our focus is to use ActiveForm and how to implement custom validation rules. Let’s talk about the scenario first: Conditions: ①. There are two fields, A and B. ②. A has two values, 1 and 2. The requirement is: when the value of A selected by the user is equal to 1, the value of B must Fill in, when the value of A is equal to 2, it doesn't matter if the value of B is not written. Among them, A is required. Let’s take a look at how to implement it using the rules that come with Yii2. First, add the following rule /*** @inheritdoc*/ to its associated model. public function rules() { return [ [['B'], 'requiredByASpecial'], ];
1. Rules in yii2 Detailed explanation of custom verification rules rules card yii rules techrules
Introduction: rules:yii2 Detailed explanation of custom validation rules in rules: One of the powerful features of yii2 is its Form component, which is both convenient and safe. Some friends feel that after using Yii for a while, it seems to be nothing but "difficult to understand" than TP. The leader arranged for a registration function, but this guy used Baidu's various good form styles, and Baidu's validate verification. I really felt sorry for this guy. Of course, without further ado, our focus is to use ActiveForm and how to implement custom validation rules. Let’s talk about the scenario first: Conditions: ①. There are two fields, A and B
2. Detailed explanation of the use of jQuery validate verification plug-in_jquery
Introduction: This article mainly introduces the usage of jQuery validate verification plug-in in detail. Validate is a lightweight verification plug-in based on jQuery. It supports the verification of input, select and textarea. If you are interested Friends, you can refer to
3. Detailed explanation of knowledge points based on jQuery.Validate verification library_jquery
Introduction: This article introduces a detailed explanation of the knowledge points of the jQuery.Validate verification library. Friends in need can refer to
4. Introduction to the use of jQuery.Validate verification library_jquery
Introduction: This article introduces the use of jQuery.Validate verification library. Friends in need can refer to
5. Small example of jquery plug-in validate_jquery
Introduction: jquery plug-in A small example of validate verification
6. jQuery Validate validation framework classic collection_jquery
Introduction: This article is a small I have compiled a complete jquery validate verification framework to share with you. This article is very detailed. Friends who are interested should take a look.
7. jquery determines whether to enter a password twice Equality_jquery
#Introduction: This article introduces the Jquery framework easyui to determine whether the password entered twice is equal, and uses jQuery.validate to verify whether the two passwords in the form are consistent. Friends who need it can refer to
##8. CKEditor cannot verify the solution (js verification + jQuery Validate verification)_jquery
Introduction: This article mainly introduces the CKEditor unverifiable solution and the jQuery Validate verification framework in detail. Interested friends can refer to it
[Related Q&A recommendations]:
javascript - vee-validate cannot be entered after verification is not empty
javascript - How to perform jQuery Validate on ckeditor Validation
javascript - A series of questions about form validation validate
The above is the detailed content of Recommended courses on Validate verification. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 How does session hijacking work and how can you mitigate it in PHP?
Apr 06, 2025 am 12:02 AM
How does session hijacking work and how can you mitigate it in PHP?
Apr 06, 2025 am 12:02 AM
Session hijacking can be achieved through the following steps: 1. Obtain the session ID, 2. Use the session ID, 3. Keep the session active. The methods to prevent session hijacking in PHP include: 1. Use the session_regenerate_id() function to regenerate the session ID, 2. Store session data through the database, 3. Ensure that all session data is transmitted through HTTPS.
 What are Enumerations (Enums) in PHP 8.1?
Apr 03, 2025 am 12:05 AM
What are Enumerations (Enums) in PHP 8.1?
Apr 03, 2025 am 12:05 AM
The enumeration function in PHP8.1 enhances the clarity and type safety of the code by defining named constants. 1) Enumerations can be integers, strings or objects, improving code readability and type safety. 2) Enumeration is based on class and supports object-oriented features such as traversal and reflection. 3) Enumeration can be used for comparison and assignment to ensure type safety. 4) Enumeration supports adding methods to implement complex logic. 5) Strict type checking and error handling can avoid common errors. 6) Enumeration reduces magic value and improves maintainability, but pay attention to performance optimization.
 Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
The application of SOLID principle in PHP development includes: 1. Single responsibility principle (SRP): Each class is responsible for only one function. 2. Open and close principle (OCP): Changes are achieved through extension rather than modification. 3. Lisch's Substitution Principle (LSP): Subclasses can replace base classes without affecting program accuracy. 4. Interface isolation principle (ISP): Use fine-grained interfaces to avoid dependencies and unused methods. 5. Dependency inversion principle (DIP): High and low-level modules rely on abstraction and are implemented through dependency injection.
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.
 What is REST API design principles?
Apr 04, 2025 am 12:01 AM
What is REST API design principles?
Apr 04, 2025 am 12:01 AM
RESTAPI design principles include resource definition, URI design, HTTP method usage, status code usage, version control, and HATEOAS. 1. Resources should be represented by nouns and maintained at a hierarchy. 2. HTTP methods should conform to their semantics, such as GET is used to obtain resources. 3. The status code should be used correctly, such as 404 means that the resource does not exist. 4. Version control can be implemented through URI or header. 5. HATEOAS boots client operations through links in response.
 How do you handle exceptions effectively in PHP (try, catch, finally, throw)?
Apr 05, 2025 am 12:03 AM
How do you handle exceptions effectively in PHP (try, catch, finally, throw)?
Apr 05, 2025 am 12:03 AM
In PHP, exception handling is achieved through the try, catch, finally, and throw keywords. 1) The try block surrounds the code that may throw exceptions; 2) The catch block handles exceptions; 3) Finally block ensures that the code is always executed; 4) throw is used to manually throw exceptions. These mechanisms help improve the robustness and maintainability of your code.
 What are anonymous classes in PHP and when might you use them?
Apr 04, 2025 am 12:02 AM
What are anonymous classes in PHP and when might you use them?
Apr 04, 2025 am 12:02 AM
The main function of anonymous classes in PHP is to create one-time objects. 1. Anonymous classes allow classes without names to be directly defined in the code, which is suitable for temporary requirements. 2. They can inherit classes or implement interfaces to increase flexibility. 3. Pay attention to performance and code readability when using it, and avoid repeatedly defining the same anonymous classes.






