What is session control and http protocol? How to use it?
The previous article introduced you to "What is PhpSpreadsheet?" how to use? 》, this article continues to introduce to you what is session control and http protocol? How to use it? (Code attached) has certain reference value. Friends in need can refer to it. I hope it will be helpful to everyone.
Session control
1. What is a session
In reality, two A conversation between individuals is a conversation.
In a computer, the communication between the client and the server is a session.
#2. What is session control
Control of the session is session control
3, HTTP protocol?
HTTP is called a stateless tracking protocol and cannot have any state tracking
Working principle:
HTTP is based on the client-server model and is connection-oriented. A typical HTTP transaction process has the following process
The client establishes a connection with the server;
The client makes a request to the server;
The server accepts the request and returns the corresponding file as a response according to the request;
The client is connected to the server.
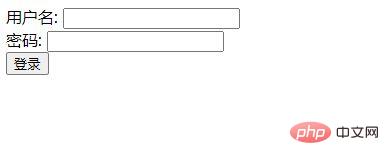
Let’s take the code as an example (login page)
<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8">
<title>Document</title>
</head>
<body>
<form action= "login . php" method="post">
用户名: <input type="text" name= "name" id=""><br/>
密码:
<input type=" password" name="pwd" id=""><br/>
<input type="submit" value="登录">
</form>
</body>
</html>The running results are as follows:
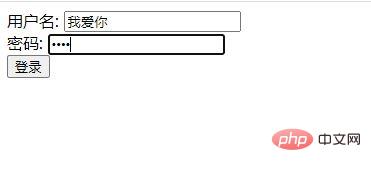
Then we create a new file (login.php)
First we need to get the user name and password entered by the user, and secondly, we query whether the user is stored in the data.
How should we query:
//$sq1 = "SELECT id FROM user WHERE name=用户输入的用户名&& pwd=等于用户输入的密码加密后的字符串”; //有数据密码正确登录成功 //没有数据提示用户名或密码错 误 请注册
Let’s take the code as an example:
<?php var_dump($_POST); ?>
The running results are as follows:
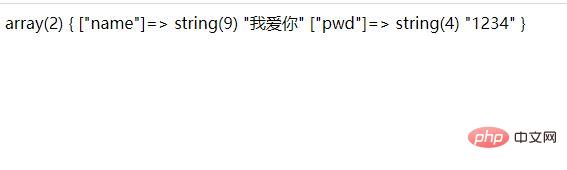
If the code is as follows, let’s take a look at the running results:
<?php
var_dump($_POST);
if($_POST['name'] == '我爱你' && $_POST['pwd'] == 'admin'){
//登录成功
echo '<script>
alert("登录成功"); location="./index.php"</script>';
}else{
//登录失 败跳转注册页面
}
?>The running results are as follows:

Then we After creating a file (index.php), we start to make the home page of the project: then when we log in successfully, we start to make the card, that is, in login.php, we take the inserted code as an example,
//制作卡片 setCookie('islogin',true ,time()+3600,'/'); setCookie('name' ,$_POST['name'],time()+3600,'/');
The information in all our cards can be queried in the cookie
<?php
//这是项目的首页
var_dump($_COOKIE);
?>After we finish running, we can add the if conditional sentence to the index page,
<?php
//这是项目的首页
//var_dump($_COOKIE);
if($_COOKIE[' islogin'] != true){
//用户没有登录
echo ' 对不起,您无权访问3S后自动跳转到登录页面' ;
echo '<meta http-equiv="refresh"
content= "3;url=./login. html">';
}else{
//代表用户已经登录
echo '亲爱的'. $_COOKIE['name'].'会员,欢迎您回来<br/>' ;
echo '<a href="a . php">去a页面</a><brF>';
echo '<a href="b . php">去b页面</a><br/>';
echo '<a href="c . php">去c页面</a><br/>';
}
?>The running result As follows:
Recommended learning: "PHP Video Tutorial"
The above is the detailed content of What is session control and http protocol? How to use it?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 OWASP Top 10 PHP: Describe and mitigate common vulnerabilities.
Mar 26, 2025 pm 04:13 PM
OWASP Top 10 PHP: Describe and mitigate common vulnerabilities.
Mar 26, 2025 pm 04:13 PM
The article discusses OWASP Top 10 vulnerabilities in PHP and mitigation strategies. Key issues include injection, broken authentication, and XSS, with recommended tools for monitoring and securing PHP applications.
 PHP Secure File Uploads: Preventing file-related vulnerabilities.
Mar 26, 2025 pm 04:18 PM
PHP Secure File Uploads: Preventing file-related vulnerabilities.
Mar 26, 2025 pm 04:18 PM
The article discusses securing PHP file uploads to prevent vulnerabilities like code injection. It focuses on file type validation, secure storage, and error handling to enhance application security.
 PHP API Rate Limiting: Implementation strategies.
Mar 26, 2025 pm 04:16 PM
PHP API Rate Limiting: Implementation strategies.
Mar 26, 2025 pm 04:16 PM
The article discusses strategies for implementing API rate limiting in PHP, including algorithms like Token Bucket and Leaky Bucket, and using libraries like symfony/rate-limiter. It also covers monitoring, dynamically adjusting rate limits, and hand
 PHP Input Validation: Best practices.
Mar 26, 2025 pm 04:17 PM
PHP Input Validation: Best practices.
Mar 26, 2025 pm 04:17 PM
Article discusses best practices for PHP input validation to enhance security, focusing on techniques like using built-in functions, whitelist approach, and server-side validation.
 PHP XSS Prevention: How to protect against XSS.
Mar 26, 2025 pm 04:12 PM
PHP XSS Prevention: How to protect against XSS.
Mar 26, 2025 pm 04:12 PM
The article discusses strategies to prevent XSS attacks in PHP, focusing on input sanitization, output encoding, and using security-enhancing libraries and frameworks.
 ACID vs BASE Database: Differences and when to use each.
Mar 26, 2025 pm 04:19 PM
ACID vs BASE Database: Differences and when to use each.
Mar 26, 2025 pm 04:19 PM
The article compares ACID and BASE database models, detailing their characteristics and appropriate use cases. ACID prioritizes data integrity and consistency, suitable for financial and e-commerce applications, while BASE focuses on availability and
 PHP Password Hashing: password_hash and password_verify.
Mar 26, 2025 pm 04:15 PM
PHP Password Hashing: password_hash and password_verify.
Mar 26, 2025 pm 04:15 PM
The article discusses the benefits of using password_hash and password_verify in PHP for securing passwords. The main argument is that these functions enhance password protection through automatic salt generation, strong hashing algorithms, and secur
 PHP Interface vs Abstract Class: When to use each.
Mar 26, 2025 pm 04:11 PM
PHP Interface vs Abstract Class: When to use each.
Mar 26, 2025 pm 04:11 PM
The article discusses the use of interfaces and abstract classes in PHP, focusing on when to use each. Interfaces define a contract without implementation, suitable for unrelated classes and multiple inheritance. Abstract classes provide common funct






