 Hardware Tutorial
Hardware Tutorial
 Hardware News
Hardware News
 Detailed introduction to RX 6800M evaluation and running parameters
Detailed introduction to RX 6800M evaluation and running parameters
Detailed introduction to RX 6800M evaluation and running parameters
RX 6800M has also been greatly improved compared to previous products. Not only the performance but also the heat dissipation are very good improvements, which can make you feel full of experience during the game.

RX 6800M Review
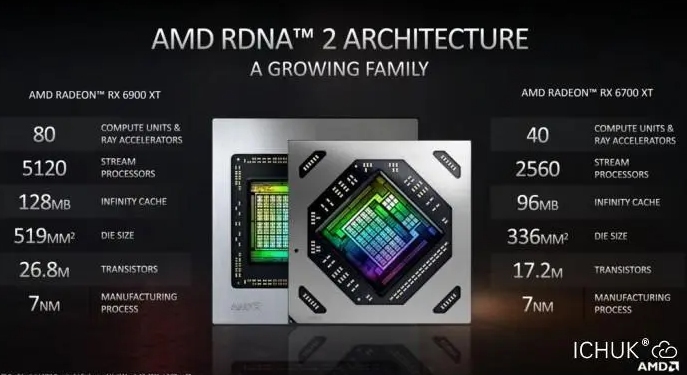
1. AMD hereby states that compared to the mobile version of RTX 2070 in 2019, the performance has improved in various games. A significant advantage of 40% to 70% has been achieved.
2. As a related product tailored by AMD for 1440p gaming notebooks, the performance of RX 6800M can undoubtedly meet the diverse needs of this consumer group.
3. In the Time Spy test scenario based on DX12, the performance gap between the two major graphics card brands has narrowed significantly, but compared to RTX 3080 (130W), Radeon RX 6800M still maintains 5.11% The advantages.
RX 6800M Benchmark
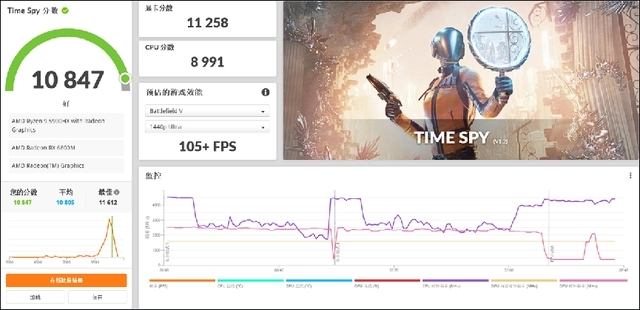
In the Time Spy benchmark test, we noticed that the system using the RX 6800M graphics card achieved a performance of 11258 points, compared to The RTX 3080, which consumes 105 watts of power (this model's performance is close to that of the RTX 3070, which consumes approximately 130 watts) shows a lead of about 11%. However, it is worth noting that there is still a slight gap between the RX 6800M and the RTX 3080, which has a power management of 150 watts.
RX 6800M parameters
| Core frequency | 2321 MHz |
|---|---|
| Turbo frequency | 2581 MHz |
| Stream processing unit | 2560 units |
| Core architecture | RDNA 2.0 |
| GPU code | Navi 22 |
| Production process | 7 nm |
| TDP power consumption | 230W |
| Memory parameters | |
| Memory frequency | 16 Gbps |
|---|---|
| Memory type | GDDR6 |
| Memory bit width | 192 bit |
| Maximum video memory | 12 GB |
RX 6800M Picture

The above is the detailed content of Detailed introduction to RX 6800M evaluation and running parameters. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.
 Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Java 8 introduces the Stream API, providing a powerful and expressive way to process data collections. However, a common question when using Stream is: How to break or return from a forEach operation? Traditional loops allow for early interruption or return, but Stream's forEach method does not directly support this method. This article will explain the reasons and explore alternative methods for implementing premature termination in Stream processing systems. Further reading: Java Stream API improvements Understand Stream forEach The forEach method is a terminal operation that performs one operation on each element in the Stream. Its design intention is
 What are PHP magic methods (__construct, __destruct, __call, __get, __set, etc.) and provide use cases?
Apr 03, 2025 am 12:03 AM
What are PHP magic methods (__construct, __destruct, __call, __get, __set, etc.) and provide use cases?
Apr 03, 2025 am 12:03 AM
What are the magic methods of PHP? PHP's magic methods include: 1.\_\_construct, used to initialize objects; 2.\_\_destruct, used to clean up resources; 3.\_\_call, handle non-existent method calls; 4.\_\_get, implement dynamic attribute access; 5.\_\_set, implement dynamic attribute settings. These methods are automatically called in certain situations, improving code flexibility and efficiency.
 PHP and Python: Comparing Two Popular Programming Languages
Apr 14, 2025 am 12:13 AM
PHP and Python: Comparing Two Popular Programming Languages
Apr 14, 2025 am 12:13 AM
PHP and Python each have their own advantages, and choose according to project requirements. 1.PHP is suitable for web development, especially for rapid development and maintenance of websites. 2. Python is suitable for data science, machine learning and artificial intelligence, with concise syntax and suitable for beginners.
 What is Cross-Site Request Forgery (CSRF) and how do you implement CSRF protection in PHP?
Apr 07, 2025 am 12:02 AM
What is Cross-Site Request Forgery (CSRF) and how do you implement CSRF protection in PHP?
Apr 07, 2025 am 12:02 AM
In PHP, you can effectively prevent CSRF attacks by using unpredictable tokens. Specific methods include: 1. Generate and embed CSRF tokens in the form; 2. Verify the validity of the token when processing the request.
 Explain the match expression (PHP 8 ) and how it differs from switch.
Apr 06, 2025 am 12:03 AM
Explain the match expression (PHP 8 ) and how it differs from switch.
Apr 06, 2025 am 12:03 AM
In PHP8, match expressions are a new control structure that returns different results based on the value of the expression. 1) It is similar to a switch statement, but returns a value instead of an execution statement block. 2) The match expression is strictly compared (===), which improves security. 3) It avoids possible break omissions in switch statements and enhances the simplicity and readability of the code.





