 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to implement an effective web interface security policy on a Linux server?
How to implement an effective web interface security policy on a Linux server?
How to implement an effective web interface security policy on a Linux server?
How to implement an effective web interface security policy on a Linux server?
With the rapid development of the Internet, Web interfaces have become an important part of modern applications. Web interfaces provide convenience and efficiency for data interaction between various software systems, but they also bring security risks. To protect these web interfaces from unauthorized access, data leakage, and malicious attacks, it is crucial to implement an effective web interface security strategy.
This article will introduce how to implement an effective web interface security policy on a Linux server to protect the sensitive data of the system and users.
- Use secure communication protocols
In order to ensure the security of data during transmission, it is crucial to use secure communication protocols. The HTTPS protocol uses the SSL/TLS protocol to encrypt data for transmission, thereby preventing data from being eavesdropped and tampered with. Configure and enable HTTPS on the Linux server, and you can obtain a valid SSL certificate through the certificate authority to achieve secure transmission of the web interface. - Use strong passwords and multi-factor authentication
Strong passwords are a basic requirement to protect user accounts from malicious attacks. In the web interface, users are required to set a password that is complex and difficult to guess, such as containing uppercase and lowercase letters, numbers, and special characters. In addition, in order to further improve security, multi-factor authentication can be implemented, such as mobile phone verification code, fingerprint recognition, etc., to increase the level of user identity verification. - Implement access control and permission management
On a Linux server, access to the web interface can be restricted by implementing access control and permission management policies. Using firewall rules and network security groups, you can control access from specific IP addresses or ranges of IP addresses. Meanwhile, role-based access control (RBAC) can manage access to specific functions and data based on user roles and permissions. In addition, regular audits and monitoring are conducted to detect abnormal behavior of the system and take timely measures to deal with it. - Implement input validation and filtering
Web interfaces are often threatened by various input attacks, such as cross-site scripting (XSS) attacks, SQL injection attacks, etc. To prevent these attacks, user input should be validated and filtered. Input validation verifies that user-supplied data conforms to specified formats and rules, while input filtering filters out potentially malicious code and sensitive characters. - Update and maintain security patches
Timely updating and maintaining the software and operating system on the server are important measures to maintain the security of the web interface. Updates include security patches and updates to the operating system and web server software. These security patches fix known vulnerabilities and security vulnerabilities, preventing hackers from exploiting them to invade the system. - Secure Data Storage and Encryption
For sensitive data stored on the server, it is very important to use secure storage and encryption mechanisms. Using an encrypted file system protects data from unauthorized access. At the same time, at the database level, encryption algorithms can be used to encrypt sensitive data to ensure the security of data during storage and transmission. - Regular backup and disaster recovery
Regular backup of data on the server is an important measure to prevent data loss and quickly restore the system. Protect your data from hardware failure, natural disasters, and human error by backing it up to a secure external storage device or cloud storage. At the same time, establish a complete disaster recovery plan to quickly restore the system in the event of a major system failure.
To summarize, implementing an effective web interface security policy on a Linux server requires the use of secure communication protocols, strong passwords and multi-factor authentication, implementation of access control and permission management, input validation and filtering , update and maintain security patches, secure data storage and encryption, regular backups and disaster recovery and other measures. By comprehensively applying these strategies, the security of the web interface can be improved and user data and systems can be protected from attacks.
The above is the detailed content of How to implement an effective web interface security policy on a Linux server?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to use PHP scripts to implement cross-server file transfer on Linux servers
Oct 05, 2023 am 09:06 AM
How to use PHP scripts to implement cross-server file transfer on Linux servers
Oct 05, 2023 am 09:06 AM
Title: PHP script implementation of cross-server file transfer 1. Introduction In cross-server file transfer, we usually need to transfer files from one server to another. This article will introduce how to use PHP scripts to implement cross-server file transfer on Linux servers, and give specific code examples. 2. Preparation Before starting to write PHP scripts, we need to ensure that the following environment has been configured on the server: Install PHP: Install PHP on the Linux server and ensure that the PHP version meets the code requirements.
 How to deploy a trustworthy web interface on a Linux server?
Sep 09, 2023 pm 03:27 PM
How to deploy a trustworthy web interface on a Linux server?
Sep 09, 2023 pm 03:27 PM
How to deploy a trustworthy web interface on a Linux server? Introduction: In today's era of information explosion, Web applications have become one of the main ways for people to obtain information and communicate. In order to ensure user privacy and information reliability, we need to deploy a trustworthy Web interface on the Linux server. This article will introduce how to deploy a web interface in a Linux environment and provide relevant code examples. 1. Install and configure the Linux server. First, we need to prepare a Li
 Key points of price strategy and promotion design in PHP flash sale system
Sep 19, 2023 pm 02:18 PM
Key points of price strategy and promotion design in PHP flash sale system
Sep 19, 2023 pm 02:18 PM
Key points of price strategy and promotion design in PHP flash sale system In a flash sale system, price strategy and promotion design are very important parts. Reasonable price strategies and well-designed promotions can attract users to participate in flash sale activities and improve the user experience and profitability of the system. The following will introduce the key points of price strategy and promotional activity design in the PHP flash sale system in detail, and provide specific code examples. 1. Key points in price strategy design: Determine the benchmark price: In the flash sale system, the benchmark price refers to the price of the product when it is normally sold. exist
 exe to php: an effective strategy to achieve function expansion
Mar 04, 2024 pm 09:36 PM
exe to php: an effective strategy to achieve function expansion
Mar 04, 2024 pm 09:36 PM
EXE to PHP: An effective strategy to achieve function expansion. With the development of the Internet, more and more applications have begun to migrate to the web to achieve wider user access and more convenient operations. In this process, the demand for converting functions originally run as EXE (executable files) into PHP scripts is also gradually increasing. This article will discuss how to convert EXE to PHP to achieve functional expansion, and give specific code examples. Why Convert EXE to PHP Cross-Platformness: PHP is a cross-platform language
 Linux server failure and security: How to manage your system healthily
Sep 10, 2023 pm 04:02 PM
Linux server failure and security: How to manage your system healthily
Sep 10, 2023 pm 04:02 PM
With the development of Internet technology, more and more enterprises and individuals choose to use Linux servers to host and manage their applications and websites. However, as the number of servers increases, server failures and security issues become an urgent task. This article will explore the causes of Linux server failures and how to manage and protect the system healthily. First, let's take a look at some common reasons that can cause Linux servers to malfunction. Firstly, hardware failure is one of the most common reasons. For example, the server is overheating,
 How to optimize the performance and resource utilization of Linux servers
Nov 07, 2023 pm 02:27 PM
How to optimize the performance and resource utilization of Linux servers
Nov 07, 2023 pm 02:27 PM
How to optimize the performance and resource utilization of Linux servers requires specific code examples. Summary: Optimizing Linux server performance and resource utilization is the key to ensuring stable and efficient server operation. This article will introduce some methods to optimize Linux server performance and resource utilization, and provide specific code examples. Introduction: With the rapid development of the Internet, a large number of applications and services are deployed on Linux servers. In order to ensure the efficient and stable operation of the server, we need to optimize the performance and resource utilization of the server to achieve
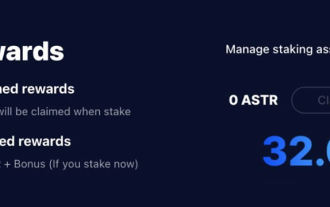 Astar staking principle, income dismantling, airdrop projects and strategies & operation nanny-level strategy
Jun 25, 2024 pm 07:09 PM
Astar staking principle, income dismantling, airdrop projects and strategies & operation nanny-level strategy
Jun 25, 2024 pm 07:09 PM
Table of Contents Astar Dapp Staking Principle Staking Revenue Dismantling of Potential Airdrop Projects: AlgemNeurolancheHealthreeAstar Degens DAOVeryLongSwap Staking Strategy & Operation "AstarDapp Staking" has been upgraded to the V3 version at the beginning of this year, and many adjustments have been made to the staking revenue rules. At present, the first staking cycle has ended, and the "voting" sub-cycle of the second staking cycle has just begun. To obtain the "extra reward" benefits, you need to grasp this critical stage (expected to last until June 26, with less than 5 days remaining). I will break down the Astar staking income in detail,
 Full analysis of CentOS7 software installation steps and strategies
Jan 04, 2024 am 09:40 AM
Full analysis of CentOS7 software installation steps and strategies
Jan 04, 2024 am 09:40 AM
I started to officially come into contact with Linux in 2010. The entry-level distribution was Ubuntu10.10, and later transitioned to Ubunu11.04. During this period, I also tried many other mainstream distributions. After entering the laboratory, I started using CentOS5, then CentOS6, and now it has evolved to CentOS7. I have been using Linux for four years. The first three years were spent messing around, wasting a lot of time, and gaining a lot of experience and lessons. Maybe I am really old now and am no longer willing to bother with it. I just hope that after configuring a system, I can continue to use it. Why write/read this article? When using Linux, especially CentOS, you will encounter some pitfalls, or some things that people with mysophobia can't tolerate: software from official sources





