What computer components does virtual storage mainly rely on?
Virtual storage is mainly realized by relying on the computer's hard disk; a computer task only needs to be partially loaded into the main memory to start running, and the rest remains on the disk and loaded into the main memory when needed, which can improve the main memory. The utilization rate of memory space is such that the main memory capacity of the system will be much larger than the actual main memory capacity. Such memory is called virtual memory.
The operating environment of this tutorial: Windows 10 system, DELL G3 computer.
What computer device does virtual storage mainly rely on?
Virtual storage mainly relies on hard disk;
A computer task only needs to be partially loaded into the main memory It can be started and run, and the rest will be left on the disk and loaded into the main memory when needed, which can improve the utilization of the main memory space. In this way, the main memory capacity of the system will be much larger than the actual main memory capacity. Such memory is called virtual memory.
Virtual hard disk and virtual cache are mainly implemented by relying on memory and U disk. Virtual memory is necessary for the operation of the host; the virtual hard disk can be used to store temporary files such as TEMP folders and web pages, which will be automatically cleared when shutting down to avoid garbage accumulation; the virtual cache can avoid frequent writes to the hard disk. When downloading a large number of files such as videos, it can effectively protect the mechanical hard disk; for solid disks, the life span mainly depends on the amount of data written. Using virtual cache can only write the data that needs to be written to the solid disk into the cache, which can greatly reduce the need for hard drives. Disk write volume, so that there is no need to write at all.
Expand knowledge
1. Virtual storage on the server side
Server manufacturers will implement virtual storage on the server side. Likewise, software vendors will implement virtual storage on server platforms. The implementation of these virtual storage is to map the image to the peripheral storage device through the server side. In addition to allocating data, there is no control over the peripheral storage device. The server side generally implements virtual storage technology through logical volume management. Logical volume management provides a virtualization layer for mapping physical storage to logical volumes. The server only needs to deal with logical volumes and does not have to manage the physical parameters of the storage device.
Using this method to build a virtual storage system, the server side is a performance bottleneck, so it is rarely used in the field of multimedia processing.
2. Virtual storage on the storage subsystem side
Another place to implement virtualization is in the storage device itself. This kind of virtual storage is generally implemented by the storage manufacturer, but it is likely to use the manufacturer's exclusive storage product. To avoid such incompatibilities, vendors may work with server, software or network vendors. When virtual storage is implemented on the device side, the logical (virtual) environment and the physical device are under the same control. The benefit of this is that virtual disks use disk capacity highly efficiently, and virtual tapes use tape media highly efficiently.
The virtual storage device on the storage subsystem side is mainly connected to the server through a large-scale RAID subsystem and multiple I/O channels. The intelligent controller provides LUN access control, caching and other functions such as data replication, etc. management functions. The advantage of this approach is that the storage device administrator has complete control over the device, and by being separated from the server system, the management of the storage can be isolated from multiple server operating systems, and hardware parameters can be easily adjusted.
3. Implementing virtual storage on the network device side
Network manufacturers will implement virtual storage on the network device side and map the logical image to the peripheral storage device through the network. In addition to allocating data, there is no control over the peripheral storage device. It is reasonable to implement virtual storage on the network side, because its implementation is neither on the server side nor on the storage device side, but between the two environments. It may be the most "open" virtual implementation environment and the most It is possible to support any server, operating system, application and storage device. Technically speaking, there are two structural forms of virtual storage implemented on the network side: symmetric and asymmetric virtual storage.
Judging from the actual situation of current virtual storage technologies and products, host-based and storage-based methods are most attractive to early adopters because they do not require any additional hardware, but for heterogeneous storage In terms of system and operating system, the system does not run very well. The method based on interconnected devices is between the two. It avoids some security issues, has stronger storage virtualization functions, can reduce the load of a single host, and can achieve good scalability.
No matter what kind of virtual storage technology is used, its purpose is to provide a high-performance, safe, stable, reliable and scalable storage network platform to meet the demanding requirements of program production network systems. According to the comprehensive performance-price ratio, under normal circumstances, when host-based and storage device-based virtual storage technologies can ensure the data processing capability requirements of the system, priority is given, because these two virtual storage technologies are convenient to construct, simple to manage, and It is easy to maintain, the product is relatively mature, and the performance-price ratio is high. When pure virtual storage technology based on storage devices cannot guarantee the performance requirements of the storage system, we can consider using virtual storage technology based on interconnection devices.
For more related knowledge, please visit the FAQ column!
The above is the detailed content of What computer components does virtual storage mainly rely on?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1661
1661
 14
14
 1418
1418
 52
52
 1311
1311
 25
25
 1261
1261
 29
29
 1234
1234
 24
24
 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
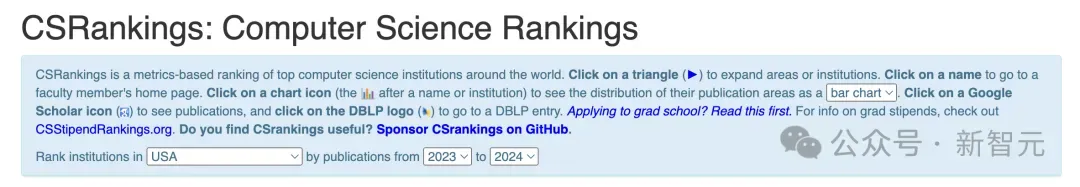 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
 What is e in computer
Aug 31, 2023 am 09:36 AM
What is e in computer
Aug 31, 2023 am 09:36 AM
The "e" of computer is the scientific notation symbol. The letter "e" is used as the exponent separator in scientific notation, which means "multiplied to the power of 10". In scientific notation, a number is usually written as M × 10^E, where M is a number between 1 and 10 and E represents the exponent.
 Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
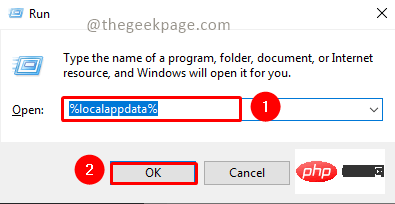
<p>MSTeams is the trusted platform to communicate, chat or call with teammates and colleagues. Error code 80090016 on MSTeams and the message <strong>Your computer's Trusted Platform Module has failed</strong> may cause difficulty logging in. The app will not allow you to log in until the error code is resolved. If you encounter such messages while opening MS Teams or any other Microsoft application, then this article can guide you to resolve the issue. </p><h2&
 What does computer cu mean?
Aug 15, 2023 am 09:58 AM
What does computer cu mean?
Aug 15, 2023 am 09:58 AM
The meaning of cu in a computer depends on the context: 1. Control Unit, in the central processor of a computer, CU is the component responsible for coordinating and controlling the entire computing process; 2. Compute Unit, in a graphics processor or other accelerated processor, CU is the basic unit for processing parallel computing tasks.
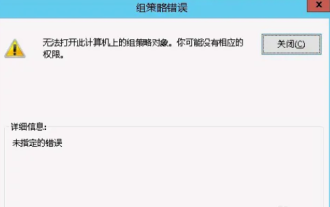 Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Occasionally, the operating system may malfunction when using a computer. The problem I encountered today was that when accessing gpedit.msc, the system prompted that the Group Policy object could not be opened because the correct permissions may be lacking. The Group Policy object on this computer could not be opened. Solution: 1. When accessing gpedit.msc, the system prompts that the Group Policy object on this computer cannot be opened because of lack of permissions. Details: The system cannot locate the path specified. 2. After the user clicks the close button, the following error window pops up. 3. Check the log records immediately and combine the recorded information to find that the problem lies in the C:\Windows\System32\GroupPolicy\Machine\registry.pol file
 What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
Solution to the problem that steam cannot connect to the remote computer: 1. In the game platform, click the "steam" option in the upper left corner; 2. Open the menu and select the "Settings" option; 3. Select the "Remote Play" option; 4. Check Activate the "Remote Play" function and click the "OK" button.
 Python script to log out of computer
Sep 05, 2023 am 08:37 AM
Python script to log out of computer
Sep 05, 2023 am 08:37 AM
In today's digital age, automation plays a vital role in streamlining and simplifying various tasks. One of these tasks is to log off the computer, which is usually done manually by selecting the logout option from the operating system's user interface. But what if we could automate this process using a Python script? In this blog post, we'll explore how to create a Python script that can log off your computer with just a few lines of code. In this article, we'll walk through the step-by-step process of creating a Python script for logging out of your computer. We'll cover the necessary prerequisites, discuss different ways to log out programmatically, and provide a step-by-step guide to writing the script. Additionally, we will address platform-specific considerations and highlight best practices



