Has the use of the Internet become the main way for computer viruses to spread?
Correct, using the Internet to spread has become the main way for computer viruses to spread. Computer network resource sharing has become easier. People often download and share software online for free, and virus files are inevitably included in them, which makes viruses spread. Speed is accelerating, and the Internet is the main way modern viruses spread.
#The operating environment of this article: Windows 7 system, Dell G3 computer.
There are roughly two ways of virus transmission:
One is through the Internet, including the Internet and LAN, and the other is through mobile media, such as U disks, mobile hard drives, etc.
Mobile media spread
(1) Through floppy disks: By using floppy disks infected by the outside world.
For example, system disks from different sources, software from unknown sources, game disks, etc. are the most common infection routes. Due to the use of virus-containing floppy disks, the machine becomes infected with the virus and is transmitted to uninfected "clean" floppy disks. A large number of floppy disk exchanges, legal or illegal program copies, and the uncontrolled use of various software on the machine have created a hotbed for virus infection and spread.
(2) Through the hard disk: Infection through the hard disk is also an important channel. Because the machine with the virus is moved to other places for use, maintenance, etc., clean floppy disks will be infected and then spread.
(3) Through the CD: Because the CD has a large capacity and stores a large number of executable files, a large number of viruses may hide in the CD. Write operations cannot be performed on read-only CDs, so the Viruses cannot be removed. In the process of producing illegally pirated software for profit, it is impossible to take special responsibility for virus protection, and there will never be truly reliable and feasible technical guarantees to avoid the introduction, infection, epidemic and spread of viruses. Currently, the proliferation of pirated CDs has brought great convenience to the spread of viruses.
Internet spread
With the popularity of the Internet, new ways have been added to the spread of viruses. Its development makes viruses likely to become disasters, and the spread of viruses is even more Quickly, the anti-virus task becomes more difficult. The Internet brings two different security threats. One threat comes from file downloads. These files that are browsed or downloaded may contain viruses. Another threat comes from email. Most Internet mail systems provide the function of transmitting emails with formatted documents between networks. Therefore, documents or files affected by viruses may flow into the corporate network through gateways and mail servers. The ease and openness of using the Internet make this threat increasingly serious.
Download virus files on the Internet. Today, as computers become increasingly popular, people transfer files and letters to each other through computer networks, which accelerates the spread of viruses. Because of the sharing of resources, people often download and share software and viruses online for free. Files are inevitably included, and the Internet is the main way modern viruses spread.
The above is the detailed content of Has the use of the Internet become the main way for computer viruses to spread?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
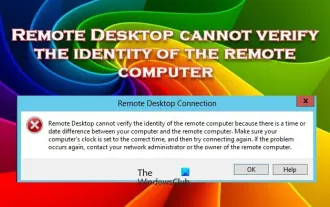 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
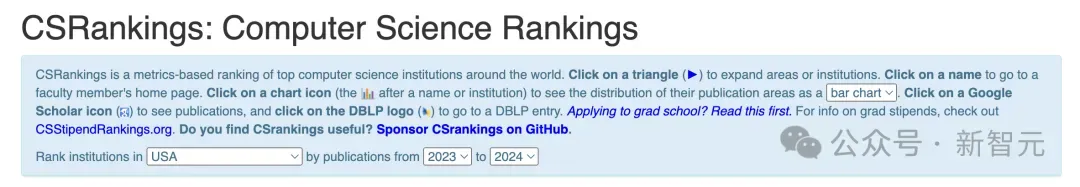 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
 What is e in computer
Aug 31, 2023 am 09:36 AM
What is e in computer
Aug 31, 2023 am 09:36 AM
The "e" of computer is the scientific notation symbol. The letter "e" is used as the exponent separator in scientific notation, which means "multiplied to the power of 10". In scientific notation, a number is usually written as M × 10^E, where M is a number between 1 and 10 and E represents the exponent.
![How to Show Internet Speed on Taskbar [Easy Steps]](https://img.php.cn/upload/article/000/465/014/169088173253603.png?x-oss-process=image/resize,m_fill,h_207,w_330) How to Show Internet Speed on Taskbar [Easy Steps]
Aug 01, 2023 pm 05:22 PM
How to Show Internet Speed on Taskbar [Easy Steps]
Aug 01, 2023 pm 05:22 PM
Internet speed is an important parameter in determining the outcome of your online experience. Whether downloading or uploading files or just browsing the web, we all need a decent internet connection. This is why users look for ways to display internet speed on the taskbar. Displaying network speed in the taskbar allows users to monitor things quickly, no matter the task at hand. The taskbar is always visible unless you are in full screen mode. But Windows doesn't offer a native option to display internet speed in the taskbar. That's why you need third-party tools. Read on to learn all about the best options! How to run a speed test from the Windows command line? Press + to open Run, type power shell, and press ++. Window
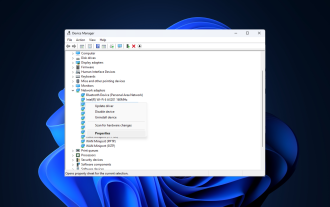 Fix: Network connection issue that prevents access to the Internet in Windows 11 Safe Mode
Sep 23, 2023 pm 01:13 PM
Fix: Network connection issue that prevents access to the Internet in Windows 11 Safe Mode
Sep 23, 2023 pm 01:13 PM
Having no internet connection on your Windows 11 computer in Safe Mode with Networking can be frustrating, especially when diagnosing and troubleshooting system issues. In this guide, we will discuss the potential causes of the problem and list effective solutions to ensure you can access the internet in Safe Mode. Why is there no internet in safe mode with networking? The network adapter is incompatible or not loading correctly. Third-party firewalls, security software, or antivirus software may interfere with network connections in safe mode. Network service is not running. Malware Infection What should I do if the Internet cannot be used in Safe Mode on Windows 11? Before performing advanced troubleshooting steps, you should consider performing the following checks: Make sure to use
 What does computer cu mean?
Aug 15, 2023 am 09:58 AM
What does computer cu mean?
Aug 15, 2023 am 09:58 AM
The meaning of cu in a computer depends on the context: 1. Control Unit, in the central processor of a computer, CU is the component responsible for coordinating and controlling the entire computing process; 2. Compute Unit, in a graphics processor or other accelerated processor, CU is the basic unit for processing parallel computing tasks.
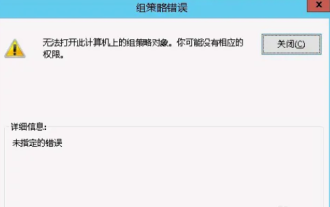 Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Occasionally, the operating system may malfunction when using a computer. The problem I encountered today was that when accessing gpedit.msc, the system prompted that the Group Policy object could not be opened because the correct permissions may be lacking. The Group Policy object on this computer could not be opened. Solution: 1. When accessing gpedit.msc, the system prompts that the Group Policy object on this computer cannot be opened because of lack of permissions. Details: The system cannot locate the path specified. 2. After the user clicks the close button, the following error window pops up. 3. Check the log records immediately and combine the recorded information to find that the problem lies in the C:\Windows\System32\GroupPolicy\Machine\registry.pol file
 How to completely remove viruses from mobile phones Recommended methods to deal with viruses in mobile phones
Feb 29, 2024 am 10:52 AM
How to completely remove viruses from mobile phones Recommended methods to deal with viruses in mobile phones
Feb 29, 2024 am 10:52 AM
After a mobile phone is infected with a certain Trojan virus, it cannot be detected and killed by anti-virus software. This principle is just like a computer infected with a stubborn virus. The virus can only be completely removed by formatting the C drive and reinstalling the system. , then I will explain how to completely clean the virus after the mobile phone is infected with a stubborn virus. Method 1: Open the phone and click "Settings" - "Other Settings" - "Restore Phone" to restore the phone to factory settings. Note: Before restoring factory settings, you must back up important data in the phone. The factory settings are equivalent to those of the computer. "It's the same as formatting and reinstalling the system". After the recovery, the data in the phone will be cleared. Method 2 (1) First turn off the phone, then press and hold the "power button" + "volume + button or volume - button" on the phone at the same time.





