 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Sorting algorithm: insertion sort and shell sort
Sorting algorithm: insertion sort and shell sort
Sorting algorithm: insertion sort and shell sort
Today we will talk about two classic sorting methods, insertion sorting and shell sorting. You can think of shell sort as an upgraded version of insertion sort.
Insertion Sort
The algorithm description of Insertion-Sort is a very simple and intuitive sorting algorithm. Its complexity is similar to bubble sort. The working principle is to construct an ordered sequence. For unsorted data, scan from back to front in the sorted sequence to find the corresponding position and insert it.
I found an animated picture from the Internet as follows:
The process is as follows:
From the first element Initially, the element can be considered to have been sorted;
Take out the next element and scan from back to front in the sorted element sequence;
If the element (sorted) is greater than the new element, move the element to the next position;
Repeat step 3 until you find the sorted element that is less than or equal to the new element Position;
After inserting the new element at this position;
Repeat steps 2~5.
Code implementation (C language is used here):
void insort (int arr[], int len)
{
int i,current,preindex;
for (i = 1; i < len; i++) {
preindex = i - 1;
current = arr[i];
while (preindex >= 0 && current < arr[preindex]) {
arr[preindex + 1] = arr[preindex];
preindex --;
}
arr[preindex + 1] = current;
}
}shell sorting
After understanding insertion sort, it is easy to understand shell sort.
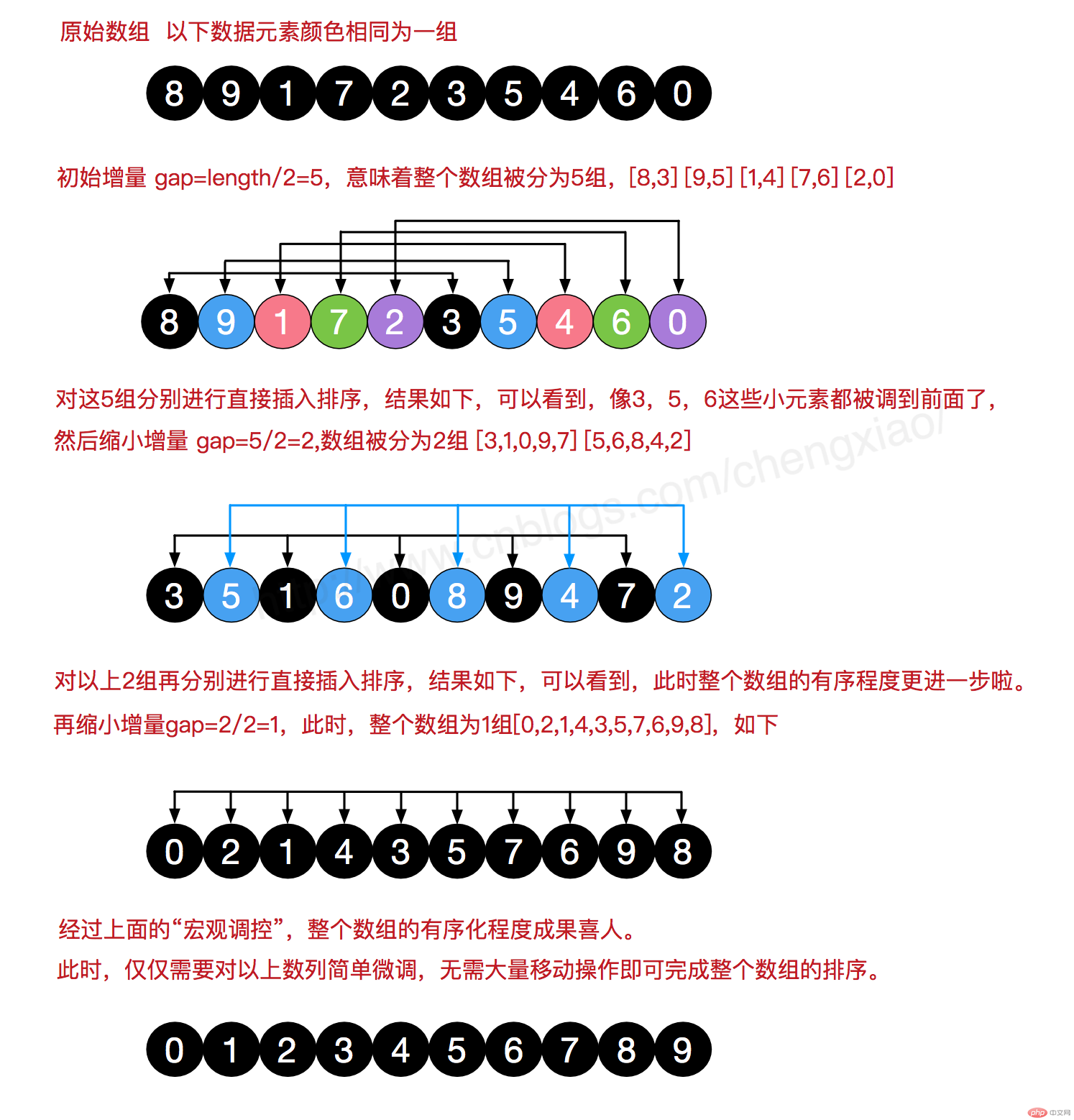
Shell sorting algorithm was invented by D.L.Shell in 1959. Its basic idea is to compare distant elements first, which can quickly reduce a large number of disordered situations, thus easing subsequent work. The distance between the compared elements gradually decreases until it is reduced to 1, at which time the sorting becomes the exchange of adjacent elements.
Hill sorting is to group records according to a certain increment in the table, and use the direct insertion sorting algorithm to sort each group; as the increment gradually decreases, each group contains more and more keywords. When When the increment is reduced to 1, the entire file is divided into one group, and the algorithm terminates.
Process demonstration (this picture was also found online):
Code implementation (C language is used here):
void shell_sort (int arr[], int len)
{
int gap,i,current,preindex;
for (gap = len / 2; gap > 0; gap /= 2) {
for (i = gap; i < len; i++) {
preindex = i - gap;
current = arr[i];
while (preindex >= 0 && current < arr[preindex]) {
arr[preindex + gap] = arr[preindex];
preindex -= gap;
}
arr[preindex + gap] = current;
}
}
}The above is the detailed content of Sorting algorithm: insertion sort and shell sort. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Where to view the logs of Tigervnc on Debian
Apr 13, 2025 am 07:24 AM
Where to view the logs of Tigervnc on Debian
Apr 13, 2025 am 07:24 AM
In Debian systems, the log files of the Tigervnc server are usually stored in the .vnc folder in the user's home directory. If you run Tigervnc as a specific user, the log file name is usually similar to xf:1.log, where xf:1 represents the username. To view these logs, you can use the following command: cat~/.vnc/xf:1.log Or, you can open the log file using a text editor: nano~/.vnc/xf:1.log Please note that accessing and viewing log files may require root permissions, depending on the security settings of the system.
 How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
The readdir function in the Debian system is a system call used to read directory contents and is often used in C programming. This article will explain how to integrate readdir with other tools to enhance its functionality. Method 1: Combining C language program and pipeline First, write a C program to call the readdir function and output the result: #include#include#include#includeintmain(intargc,char*argv[]){DIR*dir;structdirent*entry;if(argc!=2){
 How to interpret the output results of Debian Sniffer
Apr 12, 2025 pm 11:00 PM
How to interpret the output results of Debian Sniffer
Apr 12, 2025 pm 11:00 PM
DebianSniffer is a network sniffer tool used to capture and analyze network packet timestamps: displays the time for packet capture, usually in seconds. Source IP address (SourceIP): The network address of the device that sent the packet. Destination IP address (DestinationIP): The network address of the device receiving the data packet. SourcePort: The port number used by the device sending the packet. Destinatio
 Key Linux Operations: A Beginner's Guide
Apr 09, 2025 pm 04:09 PM
Key Linux Operations: A Beginner's Guide
Apr 09, 2025 pm 04:09 PM
Linux beginners should master basic operations such as file management, user management and network configuration. 1) File management: Use mkdir, touch, ls, rm, mv, and CP commands. 2) User management: Use useradd, passwd, userdel, and usermod commands. 3) Network configuration: Use ifconfig, echo, and ufw commands. These operations are the basis of Linux system management, and mastering them can effectively manage the system.
 How to recycle packages that are no longer used
Apr 13, 2025 am 08:51 AM
How to recycle packages that are no longer used
Apr 13, 2025 am 08:51 AM
This article describes how to clean useless software packages and free up disk space in the Debian system. Step 1: Update the package list Make sure your package list is up to date: sudoaptupdate Step 2: View installed packages Use the following command to view all installed packages: dpkg--get-selections|grep-vdeinstall Step 3: Identify redundant packages Use the aptitude tool to find packages that are no longer needed. aptitude will provide suggestions to help you safely delete packages: sudoaptitudesearch '~pimportant' This command lists the tags
 Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
The five basic components of the Linux system are: 1. Kernel, 2. System library, 3. System utilities, 4. Graphical user interface, 5. Applications. The kernel manages hardware resources, the system library provides precompiled functions, system utilities are used for system management, the GUI provides visual interaction, and applications use these components to implement functions.
 How Debian improves Hadoop data processing speed
Apr 13, 2025 am 11:54 AM
How Debian improves Hadoop data processing speed
Apr 13, 2025 am 11:54 AM
This article discusses how to improve Hadoop data processing efficiency on Debian systems. Optimization strategies cover hardware upgrades, operating system parameter adjustments, Hadoop configuration modifications, and the use of efficient algorithms and tools. 1. Hardware resource strengthening ensures that all nodes have consistent hardware configurations, especially paying attention to CPU, memory and network equipment performance. Choosing high-performance hardware components is essential to improve overall processing speed. 2. Operating system tunes file descriptors and network connections: Modify the /etc/security/limits.conf file to increase the upper limit of file descriptors and network connections allowed to be opened at the same time by the system. JVM parameter adjustment: Adjust in hadoop-env.sh file
 Debian Mail Server DNS Setup Guide
Apr 13, 2025 am 11:33 AM
Debian Mail Server DNS Setup Guide
Apr 13, 2025 am 11:33 AM
To configure the DNS settings for the Debian mail server, you can follow these steps: Open the network configuration file: Use a text editor (such as vi or nano) to open the network configuration file /etc/network/interfaces. sudonano/etc/network/interfaces Find network interface configuration: Find the network interface to be modified in the configuration file. Normally, the configuration of the Ethernet interface is located in the ifeth0 block.





