 Operation and Maintenance
Operation and Maintenance
 Safety
Safety
 How to fix remote command execution vulnerability in Apache axis component
How to fix remote command execution vulnerability in Apache axis component
How to fix remote command execution vulnerability in Apache axis component

Recently, Sangfor discovered how to exploit the remote command execution vulnerability of the Apache axis component. The essence of this vulnerability is due to the administrator's misconfiguration of AdminService. When the enableRemoteAdmin attribute is set to true, the attacker can remotely use the AdminService interface to self-publish the constructed WebService. When accessing the generated WebService interface again, it can be triggered. Internally referenced classes are used to exploit remote command execution vulnerabilities.
axis component introduction
axis full nameApache EXtensible Interaction System is the Apache extensible interaction system. axis provides the basic framework for creating server-side, client-side, and gateway SOAP operations. The current version of axis is mainly for Java, and the C-oriented version is under development. axis is not exactly a SOAP engine, but can also be used as a standalone SOAP server and a server embedded in a Servlet engine (such as Tomcat).
Vulnerability Analysis
The essence of the vulnerability is the administrator’s configuration error of AdminService. When the enableRemoteAdmin attribute is set to true, the attacker can construct the WebService to call the template.utility.Execute class in the freemarker component, and remotely use the AdminService interface to publish WebService , access the generated WebService interface again, pass in the command to be executed, and you can exploit the remote command execution vulnerability.
Vulnerability Recurrence
Build an environment of axis 1.4 tomcat6, and set the enableRemoteAdmin attribute in the AdminService configuration to true .
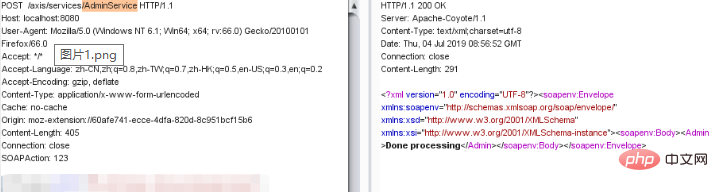
Pass in the constructed data for WebService publishing, as shown below:
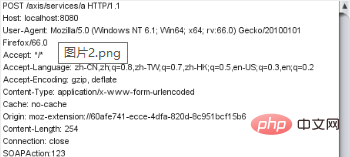
Then call the WebService interface to pass in the command and execute it, as shown below:
Repair suggestions
1. Configure URL access control policy: deployed on the axis server on the public network, you can pass The ACL prohibits access to the /services/AdminService and /services/FreeMarkerService paths.
2. Disable the axis remote management function: axis server-config.wsdd file in the WEB-INF folder in the axis directory and set the value of "enableRemoteAdmin" is false.
If you want to know more about web security, please visit: Web Server Security
The above is the detailed content of How to fix remote command execution vulnerability in Apache axis component. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to set the cgi directory in apache
Apr 13, 2025 pm 01:18 PM
How to set the cgi directory in apache
Apr 13, 2025 pm 01:18 PM
To set up a CGI directory in Apache, you need to perform the following steps: Create a CGI directory such as "cgi-bin", and grant Apache write permissions. Add the "ScriptAlias" directive block in the Apache configuration file to map the CGI directory to the "/cgi-bin" URL. Restart Apache.
 What to do if the apache80 port is occupied
Apr 13, 2025 pm 01:24 PM
What to do if the apache80 port is occupied
Apr 13, 2025 pm 01:24 PM
When the Apache 80 port is occupied, the solution is as follows: find out the process that occupies the port and close it. Check the firewall settings to make sure Apache is not blocked. If the above method does not work, please reconfigure Apache to use a different port. Restart the Apache service.
 How to connect to the database of apache
Apr 13, 2025 pm 01:03 PM
How to connect to the database of apache
Apr 13, 2025 pm 01:03 PM
Apache connects to a database requires the following steps: Install the database driver. Configure the web.xml file to create a connection pool. Create a JDBC data source and specify the connection settings. Use the JDBC API to access the database from Java code, including getting connections, creating statements, binding parameters, executing queries or updates, and processing results.
 How to view your apache version
Apr 13, 2025 pm 01:15 PM
How to view your apache version
Apr 13, 2025 pm 01:15 PM
There are 3 ways to view the version on the Apache server: via the command line (apachectl -v or apache2ctl -v), check the server status page (http://<server IP or domain name>/server-status), or view the Apache configuration file (ServerVersion: Apache/<version number>).
 How to view the apache version
Apr 13, 2025 pm 01:00 PM
How to view the apache version
Apr 13, 2025 pm 01:00 PM
How to view the Apache version? Start the Apache server: Use sudo service apache2 start to start the server. View version number: Use one of the following methods to view version: Command line: Run the apache2 -v command. Server Status Page: Access the default port of the Apache server (usually 80) in a web browser, and the version information is displayed at the bottom of the page.
 How to configure zend for apache
Apr 13, 2025 pm 12:57 PM
How to configure zend for apache
Apr 13, 2025 pm 12:57 PM
How to configure Zend in Apache? The steps to configure Zend Framework in an Apache Web Server are as follows: Install Zend Framework and extract it into the Web Server directory. Create a .htaccess file. Create the Zend application directory and add the index.php file. Configure the Zend application (application.ini). Restart the Apache Web server.
 How to delete more than server names of apache
Apr 13, 2025 pm 01:09 PM
How to delete more than server names of apache
Apr 13, 2025 pm 01:09 PM
To delete an extra ServerName directive from Apache, you can take the following steps: Identify and delete the extra ServerName directive. Restart Apache to make the changes take effect. Check the configuration file to verify changes. Test the server to make sure the problem is resolved.
 How to solve the problem that apache cannot be started
Apr 13, 2025 pm 01:21 PM
How to solve the problem that apache cannot be started
Apr 13, 2025 pm 01:21 PM
Apache cannot start because the following reasons may be: Configuration file syntax error. Conflict with other application ports. Permissions issue. Out of memory. Process deadlock. Daemon failure. SELinux permissions issues. Firewall problem. Software conflict.





