 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
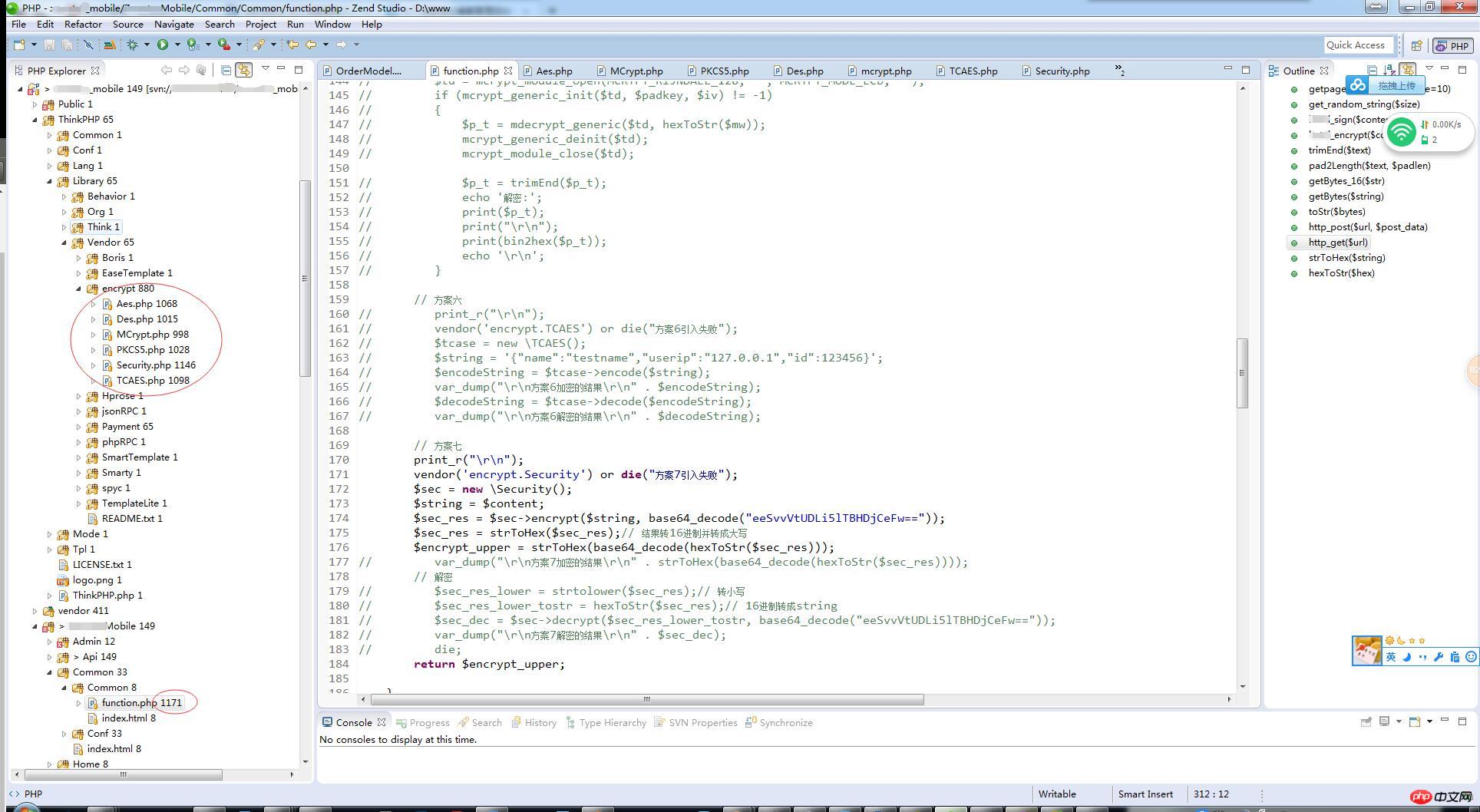
 Sample code for PHP to interface with Java's AES/ECB/PKCS5Padding encryption method (picture)
Sample code for PHP to interface with Java's AES/ECB/PKCS5Padding encryption method (picture)
Sample code for PHP to interface with Java's AES/ECB/PKCS5Padding encryption method (picture)
Due to project needs, we need to interface with an insurance company to call API. Our company is a PHP backend, and the insurance company is a java backend. The data transmission in the middle must be encrypted and encrypted. Decrypted, the currently popular encryption AES is recommended.
In the process of docking, it is inevitable to go through mountains and rivers.
The following is the encryption description of my docking company:

You must be clear about your own encryption method, otherwise the difference between an encryption mode ECB and CBC will lead to hugely different results.
Attached is the final code that can be used:
<?php
class Security {
public static function encrypt($input, $key) {
$size = mcrypt_get_block_size(MCRYPT_RIJNDAEL_128, MCRYPT_MODE_ECB);
$input = Security::pkcs5_pad($input, $size);
$td = mcrypt_module_open(MCRYPT_RIJNDAEL_128, '', MCRYPT_MODE_ECB, '');
$iv = mcrypt_create_iv (mcrypt_enc_get_iv_size($td), MCRYPT_RAND);
mcrypt_generic_init($td, $key, $iv);
$data = mcrypt_generic($td, $input);
mcrypt_generic_deinit($td);
mcrypt_module_close($td);
$data = base64_encode($data);
return $data;
}
private static function pkcs5_pad ($text, $blocksize) {
$pad = $blocksize - (strlen($text) % $blocksize);
return $text . str_repeat(chr($pad), $pad);
}
public static function decrypt($sStr, $sKey) {
$decrypted= mcrypt_decrypt(
MCRYPT_RIJNDAEL_128,
$sKey,
base64_decode($sStr),
MCRYPT_MODE_ECB
);
$dec_s = strlen($decrypted);
$padding = ord($decrypted[$dec_s-1]);
$decrypted = substr($decrypted, 0, -$padding);
return $decrypted;
}
}
// $key = "1234567891234567";
// $data = "example";
// $value = Security::encrypt($data , $key );
// echo "加密::".$value.'<br/>';
// echo Security::decrypt($value, $key );Public Called in function :
/**
* request body加密
* @param array $content 投保人的信息
* @return string
*/
function hetai_encrypt($content) {
// 方案七
print_r("\r\n");
vendor('encrypt.Security') or die("方案7引入失败");
$sec = new \Security();
$string = $content;
$sec_res = $sec->encrypt($string, base64_decode("eeSvvVtUDLi5lTBHDjCeFw=="));
$sec_res = strToHex($sec_res);// 结果转16进制并转成大写
// 这里做了好几次的转换
// 只是为了迎合出来我需要的结果而已
// 根据自己的加密要求来定
$encrypt_upper = strToHex(base64_decode(hexToStr($sec_res)));
var_dump("\r\n方案7加密的结果\r\n" . $encrypt_upper);
// 解密
$sec_res_lower = strtolower($sec_res);// 转小写
$sec_res_lower_tostr = hexToStr($sec_res);// 16进制转成string
$sec_dec = $sec->decrypt($sec_res_lower_tostr, base64_decode("eeSvvVtUDLi5lTBHDjCeFw=="));
var_dump("\r\n方案7解密的结果\r\n" . $sec_dec);
return $encrypt_upper;
}Binary String Convert to 16 Convert hexadecimal string to binary:
/**
* 字符串转十六进制
* @param string $string
* @return string
*/
function strToHex($string)
{
$hex="";
for($i=0;$i<strlen($string);$i++)
$hex.=dechex(ord($string[$i]));
$hex=strtoupper($hex);
return $hex;
}
/**
* 十六进制转字符串
* 16进制的转为2进制字符串
* @param 十六进制 $hex
* @return string
*/
function hexToStr($hex)
{
$string="";
for($i=0;$i<strlen($hex)-1;$i+=2)
$string.=chr(hexdec($hex[$i].$hex[$i+1]));
return $string;
}Attached is the encryption function block that tortured me for three days. It is only for my own reminder. If you don’t like it, please don’t comment~
The above is the detailed content of Sample code for PHP to interface with Java's AES/ECB/PKCS5Padding encryption method (picture). For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.
 Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Java 8 introduces the Stream API, providing a powerful and expressive way to process data collections. However, a common question when using Stream is: How to break or return from a forEach operation? Traditional loops allow for early interruption or return, but Stream's forEach method does not directly support this method. This article will explain the reasons and explore alternative methods for implementing premature termination in Stream processing systems. Further reading: Java Stream API improvements Understand Stream forEach The forEach method is a terminal operation that performs one operation on each element in the Stream. Its design intention is
 What are PHP magic methods (__construct, __destruct, __call, __get, __set, etc.) and provide use cases?
Apr 03, 2025 am 12:03 AM
What are PHP magic methods (__construct, __destruct, __call, __get, __set, etc.) and provide use cases?
Apr 03, 2025 am 12:03 AM
What are the magic methods of PHP? PHP's magic methods include: 1.\_\_construct, used to initialize objects; 2.\_\_destruct, used to clean up resources; 3.\_\_call, handle non-existent method calls; 4.\_\_get, implement dynamic attribute access; 5.\_\_set, implement dynamic attribute settings. These methods are automatically called in certain situations, improving code flexibility and efficiency.
 What is Cross-Site Request Forgery (CSRF) and how do you implement CSRF protection in PHP?
Apr 07, 2025 am 12:02 AM
What is Cross-Site Request Forgery (CSRF) and how do you implement CSRF protection in PHP?
Apr 07, 2025 am 12:02 AM
In PHP, you can effectively prevent CSRF attacks by using unpredictable tokens. Specific methods include: 1. Generate and embed CSRF tokens in the form; 2. Verify the validity of the token when processing the request.
 Explain the match expression (PHP 8 ) and how it differs from switch.
Apr 06, 2025 am 12:03 AM
Explain the match expression (PHP 8 ) and how it differs from switch.
Apr 06, 2025 am 12:03 AM
In PHP8, match expressions are a new control structure that returns different results based on the value of the expression. 1) It is similar to a switch statement, but returns a value instead of an execution statement block. 2) The match expression is strictly compared (===), which improves security. 3) It avoids possible break omissions in switch statements and enhances the simplicity and readability of the code.





