MySQL database audit function configuration and log analysis
MySQL database auditing mainly relies on the audit_log plug-in to implement. 1. Install the plug-in INSTALL PLUGIN audit_log SONAME 'audit_log.so';; 2. Enable the plug-in SET GLOBAL plugin_audit_log = ON;; 3. Use the CREATE AUDIT DEFINITION statement to create an audit policy, such as recording DML operations for a specific database; 4. View the log storage location through SHOW VARIABLES LIKE 'audit_log%'; and use tools to analyze the logs; 5. Advanced usage includes real-time monitoring and alarms in combination with monitoring tools. Only by rationally configuring policies and cleaning logs regularly can the database be effectively guaranteed.

MySQL Database Audit: Insight into database activities and protect data security
Have you ever thought about what happened in your MySQL database? Who is accessing the data? What operations have modified the data? The answers to these questions are hidden in the database audit function. In this article, we will discuss the configuration and log analysis of MySQL database audit function in depth to help you master this powerful tool for database security protection. After reading, you will be able to independently configure the audit function and effectively analyze the audit logs to find out potential security risks.
Let me talk about the basics first. MySQL's auditing capabilities mainly rely on its own slow query logs and general query logs, as well as some third-party tools. Slow query logging SQL statements whose execution time exceeds the specified threshold, although this is not a strict audit log, but can help us discover performance bottlenecks, which often hide security risks. General query logs record all SQL statements, but it produces a large number of logs, has a great impact on performance, and is not suitable as the main source of audit logs.
The truly powerful audit function requires the MySQL audit_log plug-in, which can accurately control the types of events that need to be recorded, such as DML operations (addition, deletion, modification), DDL operations (table creation, table modification), login and cancellation, etc. Moreover, it supports outputting audit logs to files, tables, and even remote servers, with high flexibility.
Next, let's take a look at how to configure audit_log plugin. This requires some system-level operations to ensure you have sufficient permissions. First, install the plug-in: INSTALL PLUGIN audit_log SONAME 'audit_log.so'; (Note: The path of audit_log.so may vary from system to system). Then, enable the plugin: SET GLOBAL plugin_audit_log = ON; . This is only the first step, and the more important thing is to configure the audit strategy, which requires the use of the CREATE AUDIT DEFINITION statement. For example, the following statement creates an audit policy that records all DML operations on the mydatabase database:
<code class="sql">CREATE AUDIT DEFINITION 'my_audit'<br> FOR ANY ON mydatabase<br> WITH</code><pre class='brush:php;toolbar:false;'> PRINCIPAL, STATEMENT, CLIENT, CONNECTION;</code>
This code defines an audit policy called my_audit. FOR ANY ON mydatabase specifies the audit target, and the WITH clause specifies the information to be recorded, including operation user, SQL statement, client information, and connection information. You can adjust these options as needed.
After you configure the audit strategy, the audit log will start recording. The location of the log can be viewed through SHOW VARIABLES LIKE 'audit_log%';. Logs are usually text files, with relatively simple formats, but they may be laborious to analyze. Here, we can use some tools, such as awk, grep and other Linux commands, or write simple scripts for analysis.
Advanced usage? We can combine database monitoring tools to monitor and analyze audit logs in real time, for example, set alarm rules, and issue an alarm immediately when abnormal operations are found. This requires more in-depth programming knowledge, but the advantage is that automated security monitoring can be achieved, greatly improving efficiency.
Lastly, let’s talk about some easy pitfalls. A common pitfall is that the log files are too large, resulting in insufficient disk space and even affecting database performance. To avoid this problem, you can consider cleaning the log files regularly, or using the log rotation mechanism. Another pitfall is that the audit strategy is improperly configured, resulting in incomplete information recorded, or unnecessary information recorded, affecting the efficiency of analysis. Therefore, when configuring an audit policy, you must carefully consider what information you need to record and regularly check whether the policy is effective.
In short, the MySQL database audit function is an important means to ensure database security. Proficient in its configuration and log analysis skills can effectively improve the security of the database and avoid data breaches and malicious attacks. Remember, safety is nothing small, continuous learning and practice is the king!
The above is the detailed content of MySQL database audit function configuration and log analysis. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1664
1664
 14
14
 1423
1423
 52
52
 1318
1318
 25
25
 1269
1269
 29
29
 1248
1248
 24
24
 How reliable is Binance Plaza?
May 07, 2025 pm 07:18 PM
How reliable is Binance Plaza?
May 07, 2025 pm 07:18 PM
Binance Square is a social media platform provided by Binance Exchange, aiming to provide users with a space to communicate and share information related to cryptocurrencies. This article will explore the functions, reliability and user experience of Binance Plaza in detail to help you better understand this platform.
 phpMyAdmin's Function: Interacting with MySQL (SQL)
May 07, 2025 am 12:16 AM
phpMyAdmin's Function: Interacting with MySQL (SQL)
May 07, 2025 am 12:16 AM
phpMyAdmin simplifies MySQL database management through the web interface. 1) Create databases and tables: Use graphical interface to operate easily. 2) Execute complex queries: such as JOIN query, implemented through SQL editor. 3) Optimization and best practices: including SQL query optimization, index management and data backup.
 The 5 Essential Elements of Linux: Explained
May 07, 2025 am 12:14 AM
The 5 Essential Elements of Linux: Explained
May 07, 2025 am 12:14 AM
The five core elements of Linux are: 1. Kernel, 2. Command line interface, 3. File system, 4. Package management, 5. Community and open source. Together, these elements define the nature and functionality of Linux.
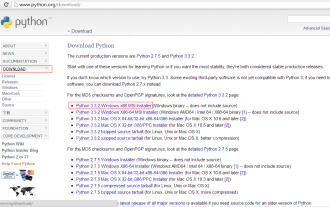 Python development_python installation
May 07, 2025 pm 04:33 PM
Python development_python installation
May 07, 2025 pm 04:33 PM
Python can run on a variety of platforms, including our common ones: Windows, Unix, Linux, and Macintosh. This article will introduce in detail the process of installing Python in Windows operating system. My operating system is Windows 7, 32-bit version. When installing Python, we can choose to install it from the source code or select the already compiled binary version for installation. I chose the latter here. Step 1 Download the installation package. We download the installation package of Python from the official Python website: http://www.python.org. The version I selected is: python-3.3.2.msi click to download, I
 MySQL: A Practical Application of SQL
May 08, 2025 am 12:12 AM
MySQL: A Practical Application of SQL
May 08, 2025 am 12:12 AM
MySQL is popular because of its excellent performance and ease of use and maintenance. 1. Create database and tables: Use the CREATEDATABASE and CREATETABLE commands. 2. Insert and query data: operate data through INSERTINTO and SELECT statements. 3. Optimize query: Use indexes and EXPLAIN statements to improve performance.
 The latest download tutorial for Ouyi OKX6.118.0 version
May 07, 2025 pm 06:51 PM
The latest download tutorial for Ouyi OKX6.118.0 version
May 07, 2025 pm 06:51 PM
The latest download tutorial for Ouyi OKX6.118.0 version: 1. Click on the quick link in the article; 2. Click on the download (if you are a web user, please register the information first). The latest Android version v6.118.0 optimizes some functions and experiences to make trading easier. Update the app now to experience a more extreme trading experience.
 How does logging and auditing differ between Linux and Windows?
May 08, 2025 am 12:03 AM
How does logging and auditing differ between Linux and Windows?
May 08, 2025 am 12:03 AM
Linuxoffersmoregranularcontroloverloggingandauditing,whileWindowsprovidesamorecentralizedsystem.1)Linuxusestoolslikesyslog,rsyslog,andjournaldforcustomizablelogging.2)WindowsusestheEventViewerforcentralizedlogmanagement.3)Linuxisidealforenvironmentsn
 2025 Binance Binance Exchange Latest Login Portal
May 07, 2025 pm 07:03 PM
2025 Binance Binance Exchange Latest Login Portal
May 07, 2025 pm 07:03 PM
As the world's leading cryptocurrency exchange, Binance is always committed to providing users with a safe and convenient trading experience. Over time, Binance has continuously optimized its platform features and user interface to meet the changing needs of users. In 2025, Binance launched a new login portal aimed at further improving the user experience.




