 Database
Database
 Mysql Tutorial
Mysql Tutorial
 How Can I Secure MySQL Login Credentials in Java Applications Against Decompilation?
How Can I Secure MySQL Login Credentials in Java Applications Against Decompilation?
How Can I Secure MySQL Login Credentials in Java Applications Against Decompilation?

Safeguarding MySQL Login Credentials from Decompilation
In the realm of programming, Java .class files are susceptible to decompilation. This raises concerns about protecting sensitive information, such as database login credentials. How can we ensure the integrity of our database while incorporating login data into our code?
Hard-coding Passwords: A Fatal Misstep
The practice of hard-coding passwords into code is a significant security vulnerability. As emphasized in the Top 25 Most Dangerous Programming Mistakes:
"If the password is the same across all your software, then every customer becomes vulnerable when that password inevitably becomes known. And because it's hard-coded, it's a **huge pain to fix."
The Preferred Solution: External Configuration Files
To safeguard login credentials, store them in a separate file that the application reads at startup. This method prevents unauthorized access to the credentials via code decompilation.
Utilizing the Preferences Class in Java
For Java applications, the Preferences class serves as an effective solution. It facilitates the storage of configuration settings, including usernames and passwords:
import java.util.prefs.Preferences;
public class DemoApplication {
Preferences preferences =
Preferences.userNodeForPackage(DemoApplication.class);
// Setter method to store credentials
public void setCredentials(String username, String password) {
preferences.put("db_username", username);
preferences.put("db_password", password);
}
// Getter methods to retrieve credentials
public String getUsername() {
return preferences.get("db_username", null);
}
public String getPassword() {
return preferences.get("db_password", null);
}
}In this example, the setCredentials method stores the provided username and password in the preference file. During database connection, the getUsername and getPassword methods retrieve these stored values. By keeping credentials external, decompilation does not compromise their security.
Security Considerations
While the preference files provide a suitable solution, they remain plain text XML files. Therefore, it is essential to implement appropriate file permissions (UNIX and Windows) to restrict unauthorized access.
Alternate Architectures for Specialized Scenarios
Authorized User Knowing Credentials: In situations where the application user is authorized to know the database credentials, the preference file approach remains effective. The user can directly access the XML file to view the credentials, but this is not a security concern since they already possess the necessary knowledge.
Concealing Credentials from User: When the database credentials must remain confidential from application users, a different strategy is needed. This requires a middle-layer system between the database server and client application that authenticates users and permits limited database access operations.
Multi-Tier Architecture as a Secure Alternative: The ideal architecture for secure database access employs a multi-tier approach:
- Client Authentication: Users authenticate with the middle layer (business logic tier) using their own usernames and passwords, which are distinct from database credentials.
- Database Access Request: If authentication succeeds, the client sends a database access request to the business logic tier.
- Secure SQL Query Execution: The business logic tier connects to the database and generates a secure SQL query based on the user's request.
- Data Retrieval and Return: The business logic tier retrieves the requested data and returns it to the client application.
- Client Data Display: The application presents the received data to the user.
In this architecture, the client never establishes a direct connection to the database, ensuring that sensitive credentials remain hidden from unauthorized parties.
The above is the detailed content of How Can I Secure MySQL Login Credentials in Java Applications Against Decompilation?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1657
1657
 14
14
 1415
1415
 52
52
 1309
1309
 25
25
 1257
1257
 29
29
 1230
1230
 24
24
 When might a full table scan be faster than using an index in MySQL?
Apr 09, 2025 am 12:05 AM
When might a full table scan be faster than using an index in MySQL?
Apr 09, 2025 am 12:05 AM
Full table scanning may be faster in MySQL than using indexes. Specific cases include: 1) the data volume is small; 2) when the query returns a large amount of data; 3) when the index column is not highly selective; 4) when the complex query. By analyzing query plans, optimizing indexes, avoiding over-index and regularly maintaining tables, you can make the best choices in practical applications.
 Can I install mysql on Windows 7
Apr 08, 2025 pm 03:21 PM
Can I install mysql on Windows 7
Apr 08, 2025 pm 03:21 PM
Yes, MySQL can be installed on Windows 7, and although Microsoft has stopped supporting Windows 7, MySQL is still compatible with it. However, the following points should be noted during the installation process: Download the MySQL installer for Windows. Select the appropriate version of MySQL (community or enterprise). Select the appropriate installation directory and character set during the installation process. Set the root user password and keep it properly. Connect to the database for testing. Note the compatibility and security issues on Windows 7, and it is recommended to upgrade to a supported operating system.
 MySQL: Simple Concepts for Easy Learning
Apr 10, 2025 am 09:29 AM
MySQL: Simple Concepts for Easy Learning
Apr 10, 2025 am 09:29 AM
MySQL is an open source relational database management system. 1) Create database and tables: Use the CREATEDATABASE and CREATETABLE commands. 2) Basic operations: INSERT, UPDATE, DELETE and SELECT. 3) Advanced operations: JOIN, subquery and transaction processing. 4) Debugging skills: Check syntax, data type and permissions. 5) Optimization suggestions: Use indexes, avoid SELECT* and use transactions.
 Can mysql and mariadb coexist
Apr 08, 2025 pm 02:27 PM
Can mysql and mariadb coexist
Apr 08, 2025 pm 02:27 PM
MySQL and MariaDB can coexist, but need to be configured with caution. The key is to allocate different port numbers and data directories to each database, and adjust parameters such as memory allocation and cache size. Connection pooling, application configuration, and version differences also need to be considered and need to be carefully tested and planned to avoid pitfalls. Running two databases simultaneously can cause performance problems in situations where resources are limited.
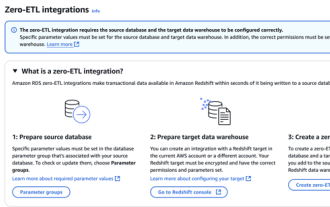 RDS MySQL integration with Redshift zero ETL
Apr 08, 2025 pm 07:06 PM
RDS MySQL integration with Redshift zero ETL
Apr 08, 2025 pm 07:06 PM
Data Integration Simplification: AmazonRDSMySQL and Redshift's zero ETL integration Efficient data integration is at the heart of a data-driven organization. Traditional ETL (extract, convert, load) processes are complex and time-consuming, especially when integrating databases (such as AmazonRDSMySQL) with data warehouses (such as Redshift). However, AWS provides zero ETL integration solutions that have completely changed this situation, providing a simplified, near-real-time solution for data migration from RDSMySQL to Redshift. This article will dive into RDSMySQL zero ETL integration with Redshift, explaining how it works and the advantages it brings to data engineers and developers.
 The relationship between mysql user and database
Apr 08, 2025 pm 07:15 PM
The relationship between mysql user and database
Apr 08, 2025 pm 07:15 PM
In MySQL database, the relationship between the user and the database is defined by permissions and tables. The user has a username and password to access the database. Permissions are granted through the GRANT command, while the table is created by the CREATE TABLE command. To establish a relationship between a user and a database, you need to create a database, create a user, and then grant permissions.
 Laravel Eloquent ORM in Bangla partial model search)
Apr 08, 2025 pm 02:06 PM
Laravel Eloquent ORM in Bangla partial model search)
Apr 08, 2025 pm 02:06 PM
LaravelEloquent Model Retrieval: Easily obtaining database data EloquentORM provides a concise and easy-to-understand way to operate the database. This article will introduce various Eloquent model search techniques in detail to help you obtain data from the database efficiently. 1. Get all records. Use the all() method to get all records in the database table: useApp\Models\Post;$posts=Post::all(); This will return a collection. You can access data using foreach loop or other collection methods: foreach($postsas$post){echo$post->
 MySQL: The Ease of Data Management for Beginners
Apr 09, 2025 am 12:07 AM
MySQL: The Ease of Data Management for Beginners
Apr 09, 2025 am 12:07 AM
MySQL is suitable for beginners because it is simple to install, powerful and easy to manage data. 1. Simple installation and configuration, suitable for a variety of operating systems. 2. Support basic operations such as creating databases and tables, inserting, querying, updating and deleting data. 3. Provide advanced functions such as JOIN operations and subqueries. 4. Performance can be improved through indexing, query optimization and table partitioning. 5. Support backup, recovery and security measures to ensure data security and consistency.



