Summary of usage examples of PHP encryption methods
PHP encryption extension library—Mhash extension library What is the Mhash extension library: Mhash is an irreversible PHP encryption extension library based on the principle of discrete mathematics. It is not enabled by default. mhash can be used to create verification values, message digests, message authentication codes, and save key information (such as passwords) without the original text. 1. Mhash extension library installation The installation of the Mhash library is similar to the installation of the Mcrypt extension library. I won’t go into more details here. You can refer to the previous article "PHP Encryption Extension Library—Mcrypt Extension Library"! 2. Mhash extension library constants The Mhash library supports multiple hashing algorithms such as MD5, SHA, CRC32, etc. You can use the mhash_count() and mhash_get_hash_name() functions to output the supported algorithm names. Let’s take a look at the sample code:
1. Summary of the article on how to use the encryption extension library
##Introduction: PHP encryption extension library-Mhash extension library What is Mhash extension library: Mhash is an irreversible PHP encryption extension library based on the principle of discrete mathematics. It is not enabled by default. mhash can be used to create verification values, message digests, message authentication codes, and save key information (such as passwords) without the original text. 1. Mhash extension library installation The installation of Mhash library is similar to the installation of Mcrypt extension library. I won’t introduce it here. You can refer to the previous article "PHP Encryption Extension Library-Mcrypt Extension Library...
2. PHP encryption extension library-Mhash extension library instance usage details
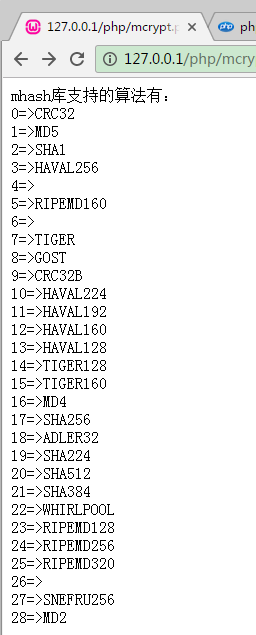
Introduction: What is the Mhash extension library: Mhash is an irreversible PHP encryption extension library based on the principle of discrete mathematics. It is not enabled by default. mhash can be used to create verification values, message digests, message authentication codes, and save key information (such as passwords) without the original text.
3. Sample code for PHP to interface with Java's AES/ECB/PKCS5Padding encryption method (picture)

Introduction: Due to project needs, we need to interface with an insurance company to call the API. Our company is a PHP backend, and the insurance company is a Java backend. The data transmission in the middle must be encrypted. , decrypted, the currently popular encryption AES is recommended.
4. WeChat public platform development: message encryption

5.
Share a PHP encryption and decryption function you just wrote
 ##Introduction: base64 encryption and XOR string encryption method to encrypt {code...} decrypt {code...} Complete code example: {code...} The whole program is very simple ~ follow logical thinking It is said that it should be difficult to crack, if others do not know your secret key; if you still feel unsafe. Then I...
##Introduction: base64 encryption and XOR string encryption method to encrypt {code...} decrypt {code...} Complete code example: {code...} The whole program is very simple ~ follow logical thinking It is said that it should be difficult to crack, if others do not know your secret key; if you still feel unsafe. Then I...
6.
php encryption discuz content classic encryption method examples detailed explanation ##Introduction: This article mainly introduces the classic encryption method of discuz content in PHP encryption. It analyzes the usage techniques of discuz encryption in detail with specific examples. It has certain reference value and is needed. Friends can refer to
##Introduction: This article mainly introduces the classic encryption method of discuz content in PHP encryption. It analyzes the usage techniques of discuz encryption in detail with specific examples. It has certain reference value and is needed. Friends can refer to
7. Java implementation of MD5 encryption and decryption code example sharing

Introduction: If the demand for security is not too high, MD5 is still a very convenient and popular encryption method, such as the one that comes with Java. The MessageDigest class provides support. Here is a code example sharing for implementing MD5 encryption and decryption in Java:
8. Detailed explanation of several ways in which PHP handles passwords _php example
#Introduction: This article mainly introduces several ways in which PHP handles passwords, and introduces the encryption processing of passwords in detail. If you need it, you can learn more one time.
9. Let’s see what encryption method this is and can it be decrypted?
##Introduction: The ciphertext looks like this: V53::eJwzcDJAASYWRhaGLsYGLqamTpZGji4GJuYGlpbGbm4mhhbmxi6OAPBkCik=The plaintext corresponds to the 11-digit mobile phone number, which is certain; so I want to ask everyone this What encryption method was used?
10. What is the communication encryption method of NetEase Cloud Music?
Introduction: As shown in the figure of RT, the post parameters in all http requests captured by the packet capture only have params, and the parameter values are all garbled. Is there anyone who can do some research? Pass his encryption method?
[Related Q&A recommendations]:
bash - How to test the delay of an ss account using the terminal or python?
The User.php class that comes with yii2 (in common/model/User.php) cannot find the login() method
java - User login, password md5 Encryption question
python - Please see what encryption method is used for this password?
javascript - How to crack js encryption
The above is the detailed content of Summary of usage examples of PHP encryption methods. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1676
1676
 14
14
 1429
1429
 52
52
 1333
1333
 25
25
 1278
1278
 29
29
 1257
1257
 24
24
 Explain secure password hashing in PHP (e.g., password_hash, password_verify). Why not use MD5 or SHA1?
Apr 17, 2025 am 12:06 AM
Explain secure password hashing in PHP (e.g., password_hash, password_verify). Why not use MD5 or SHA1?
Apr 17, 2025 am 12:06 AM
In PHP, password_hash and password_verify functions should be used to implement secure password hashing, and MD5 or SHA1 should not be used. 1) password_hash generates a hash containing salt values to enhance security. 2) Password_verify verify password and ensure security by comparing hash values. 3) MD5 and SHA1 are vulnerable and lack salt values, and are not suitable for modern password security.
 How does PHP type hinting work, including scalar types, return types, union types, and nullable types?
Apr 17, 2025 am 12:25 AM
How does PHP type hinting work, including scalar types, return types, union types, and nullable types?
Apr 17, 2025 am 12:25 AM
PHP type prompts to improve code quality and readability. 1) Scalar type tips: Since PHP7.0, basic data types are allowed to be specified in function parameters, such as int, float, etc. 2) Return type prompt: Ensure the consistency of the function return value type. 3) Union type prompt: Since PHP8.0, multiple types are allowed to be specified in function parameters or return values. 4) Nullable type prompt: Allows to include null values and handle functions that may return null values.
 PHP and Python: Different Paradigms Explained
Apr 18, 2025 am 12:26 AM
PHP and Python: Different Paradigms Explained
Apr 18, 2025 am 12:26 AM
PHP is mainly procedural programming, but also supports object-oriented programming (OOP); Python supports a variety of paradigms, including OOP, functional and procedural programming. PHP is suitable for web development, and Python is suitable for a variety of applications such as data analysis and machine learning.
 Choosing Between PHP and Python: A Guide
Apr 18, 2025 am 12:24 AM
Choosing Between PHP and Python: A Guide
Apr 18, 2025 am 12:24 AM
PHP is suitable for web development and rapid prototyping, and Python is suitable for data science and machine learning. 1.PHP is used for dynamic web development, with simple syntax and suitable for rapid development. 2. Python has concise syntax, is suitable for multiple fields, and has a strong library ecosystem.
 PHP and Python: A Deep Dive into Their History
Apr 18, 2025 am 12:25 AM
PHP and Python: A Deep Dive into Their History
Apr 18, 2025 am 12:25 AM
PHP originated in 1994 and was developed by RasmusLerdorf. It was originally used to track website visitors and gradually evolved into a server-side scripting language and was widely used in web development. Python was developed by Guidovan Rossum in the late 1980s and was first released in 1991. It emphasizes code readability and simplicity, and is suitable for scientific computing, data analysis and other fields.
 Why Use PHP? Advantages and Benefits Explained
Apr 16, 2025 am 12:16 AM
Why Use PHP? Advantages and Benefits Explained
Apr 16, 2025 am 12:16 AM
The core benefits of PHP include ease of learning, strong web development support, rich libraries and frameworks, high performance and scalability, cross-platform compatibility, and cost-effectiveness. 1) Easy to learn and use, suitable for beginners; 2) Good integration with web servers and supports multiple databases; 3) Have powerful frameworks such as Laravel; 4) High performance can be achieved through optimization; 5) Support multiple operating systems; 6) Open source to reduce development costs.
 PHP and Frameworks: Modernizing the Language
Apr 18, 2025 am 12:14 AM
PHP and Frameworks: Modernizing the Language
Apr 18, 2025 am 12:14 AM
PHP remains important in the modernization process because it supports a large number of websites and applications and adapts to development needs through frameworks. 1.PHP7 improves performance and introduces new features. 2. Modern frameworks such as Laravel, Symfony and CodeIgniter simplify development and improve code quality. 3. Performance optimization and best practices further improve application efficiency.
 PHP's Impact: Web Development and Beyond
Apr 18, 2025 am 12:10 AM
PHP's Impact: Web Development and Beyond
Apr 18, 2025 am 12:10 AM
PHPhassignificantlyimpactedwebdevelopmentandextendsbeyondit.1)ItpowersmajorplatformslikeWordPressandexcelsindatabaseinteractions.2)PHP'sadaptabilityallowsittoscaleforlargeapplicationsusingframeworkslikeLaravel.3)Beyondweb,PHPisusedincommand-linescrip




