 Backend Development
Backend Development
 Python Tutorial
Python Tutorial
 Reveal the behind-the-scenes mechanism of Python Django and unleash your programming potential
Reveal the behind-the-scenes mechanism of Python Django and unleash your programming potential
Reveal the behind-the-scenes mechanism of Python Django and unleash your programming potential

Model-View-Template (MTV) Architecture
Django adopts MTV architecture to separate application logic from the presentation layer.
- Model: represents the data and business logic in the application.
- View: Handles user requests and provides appropriate responses.
- Template: used to generate the html response that is ultimately presented to the user.
Object Relational Mapper (ORM)
DjanGo provides a powerful ORM called Django Models. It allows developers to use python objects to operate database, abstracting the underlying sql queries. ORMs simplify data access and reduce errors.
URL routing
Django uses regular expressions to route incoming URLs. Routing matches URLs to specific views, thereby determining the business logic to be performed. Routing is flexible and customizable, allowing developers to easily define complex URL patterns.
Template Engine
Django's template engine allows developers to create dynamic HTML responses using a template language. The template language provides a series of tags and filters for conditional logic, looping, and data formatting. The template engine provides a powerful and flexible way to generate HTML responses in views.
middleware
Django's Middleware are pluggable components that perform specific tasks during request and response processing. Middleware can be used for authentication, caching, compression, and exception handling. Middleware provides the flexibility to execute custom logic at different stages of the application lifecycle.
Management tools
Django provides a set of management tools called Django Admin. This tool allows developers to manage models, create and edit objects, and perform administrative tasks through a WEB interface. Management tools are useful for managing data and maintaining applications.
Testing Framework
Django integrates a comprehensive testingframework called Django Test Case. This framework provides an api for writing and executing unit and integration tests. Automated testing is essential to ensure the quality and stability of your application.
security function
Django includes a set of built-in security features, such as Cross-site Request Forgery (CSRF) protection, SQL injection protection, and user authentication. These features help protect web applications from common attacks.
Scalability and performance
Django has a scalable and optimizable high-performance architecture. It supports horizontal and vertical scaling to accommodate growing user base and application load. Django optimizes database access, caching mechanism and network performance.
Community Support
Django has a large and active community providing documentation, forums, tutorials and sample code. Community support is essential for solving problems, getting help, and staying up to date on the latest developments in Django.
Application scenarios
Django is suitable for a variety of web applications, including:
- Content Management System (CMS)
- E-commerce website
- Blogs and Online Publications
- Social Media Platform
- Data AnalysisDashboard
- Internal Enterprise Applications
The above is the detailed content of Reveal the behind-the-scenes mechanism of Python Django and unleash your programming potential. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to remove the write protection of a USB flash drive? Several simple and effective methods can help you do it
May 02, 2024 am 09:04 AM
How to remove the write protection of a USB flash drive? Several simple and effective methods can help you do it
May 02, 2024 am 09:04 AM
U disk is one of the commonly used storage devices in our daily work and life, but sometimes we encounter situations where the U disk is write-protected and cannot write data. This article will introduce several simple and effective methods to help you quickly remove the write protection of the USB flash drive and restore the normal use of the USB flash drive. Tool materials: System version: Windows1020H2, macOS BigSur11.2.3 Brand model: SanDisk UltraFlair USB3.0 flash drive, Kingston DataTraveler100G3USB3.0 flash drive Software version: DiskGenius5.4.2.1239, ChipGenius4.19.1225 1. Check the physical write protection switch of the USB flash drive on some USB flash drives Designed with
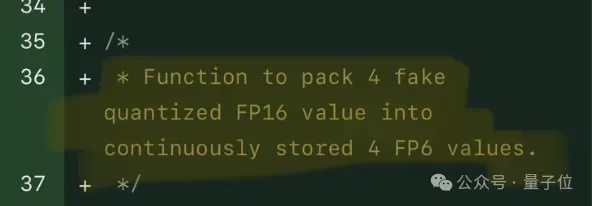 Single card running Llama 70B is faster than dual card, Microsoft forced FP6 into A100 | Open source
Apr 29, 2024 pm 04:55 PM
Single card running Llama 70B is faster than dual card, Microsoft forced FP6 into A100 | Open source
Apr 29, 2024 pm 04:55 PM
FP8 and lower floating point quantification precision are no longer the "patent" of H100! Lao Huang wanted everyone to use INT8/INT4, and the Microsoft DeepSpeed team started running FP6 on A100 without official support from NVIDIA. Test results show that the new method TC-FPx's FP6 quantization on A100 is close to or occasionally faster than INT4, and has higher accuracy than the latter. On top of this, there is also end-to-end large model support, which has been open sourced and integrated into deep learning inference frameworks such as DeepSpeed. This result also has an immediate effect on accelerating large models - under this framework, using a single card to run Llama, the throughput is 2.65 times higher than that of dual cards. one
 What is the API interface for?
Apr 23, 2024 pm 01:51 PM
What is the API interface for?
Apr 23, 2024 pm 01:51 PM
An API interface is a specification for interaction between software components and is used to implement communication and data exchange between different applications or systems. The API interface acts as a "translator", converting the developer's instructions into computer language so that the applications can work together. Its advantages include convenient data sharing, simplified development, improved performance, enhanced security, improved productivity and interoperability.
 Usage of service layer in java
May 07, 2024 am 04:24 AM
Usage of service layer in java
May 07, 2024 am 04:24 AM
The Service layer in Java is responsible for business logic and business rules for executing applications, including processing business rules, data encapsulation, centralizing business logic and improving testability. In Java, the Service layer is usually designed as an independent module, interacts with the Controller and Repository layers, and is implemented through dependency injection, following steps such as creating an interface, injecting dependencies, and calling Service methods. Best practices include keeping it simple, using interfaces, avoiding direct manipulation of data, handling exceptions, and using dependency injection.
 What does mysql database do?
Apr 22, 2024 pm 06:12 PM
What does mysql database do?
Apr 22, 2024 pm 06:12 PM
MySQL is a relational database management system that provides the following main functions: Data storage and management: Create and organize data, supporting various data types, primary keys, foreign keys, and indexes. Data query and retrieval: Use SQL language to query, filter and retrieve data, and optimize execution plans to improve efficiency. Data updates and modifications: Add, modify or delete data through INSERT, UPDATE, DELETE commands, supporting transactions to ensure consistency and rollback mechanisms to undo changes. Database management: Create and modify databases and tables, back up and restore data, and provide user management and permission control.
 What does schema mean in mysql
May 01, 2024 pm 08:33 PM
What does schema mean in mysql
May 01, 2024 pm 08:33 PM
Schema in MySQL is a logical structure used to organize and manage database objects (such as tables, views) to ensure data consistency, data access control and simplify database design. The functions of Schema include: 1. Data organization; 2. Data consistency; 3. Data access control; 4. Database design.
 Data Security in Artificial Intelligence: How to Unleash the Power of Artificial Intelligence
Apr 24, 2024 pm 06:20 PM
Data Security in Artificial Intelligence: How to Unleash the Power of Artificial Intelligence
Apr 24, 2024 pm 06:20 PM
In the digital age, data is often viewed as the battery that powers the innovation machine and drives business decisions. With the rise of modern solutions like artificial intelligence (AI) and machine learning (ML), organizations have access to vast amounts of data, enough to gain valuable insights and make informed decisions. However, this comes at the cost of subsequent data loss and confidentiality challenges. As organizations continue to grasp the potential of artificial intelligence, they must strike a balance between achieving business advancements while avoiding potential risks. This article focuses on the importance of data security in artificial intelligence and what security measures organizations can take to avoid risks while taking advantage of the viable solutions provided by artificial intelligence. In artificial intelligence, data security is crucial. Organizations need to ensure data used is legal
 How to upload running data to keep
May 04, 2024 pm 10:51 PM
How to upload running data to keep
May 04, 2024 pm 10:51 PM
Steps to upload running data to Keep: 1. Connect the device and authorize data access; 2. Turn on automatic synchronization; 3. Manually upload data (if the device does not support automatic synchronization).





