 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Linux - 11 steps to teach you how to perfectly check whether your server has been compromised
Linux - 11 steps to teach you how to perfectly check whether your server has been compromised
Linux - 11 steps to teach you how to perfectly check whether your server has been compromised

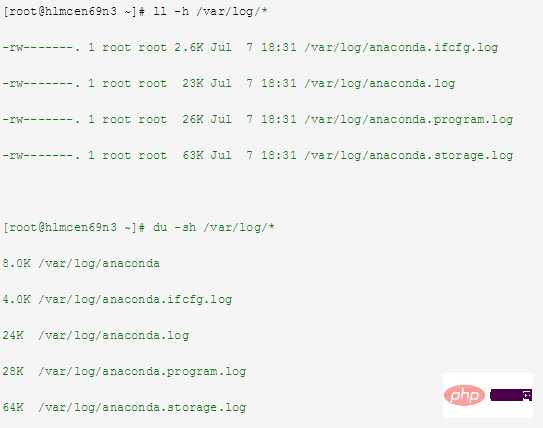
1Intrudermay delete the log information of the machine
You can check whether the log information still exists or whether it has been cleared, related commands Example:
##2Intrudermay create a new file to store username and password
##You can view /etc/passwd and /etc/ shadow file, related command examples:
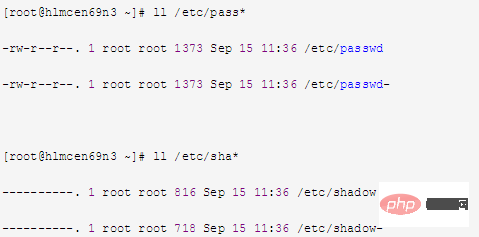
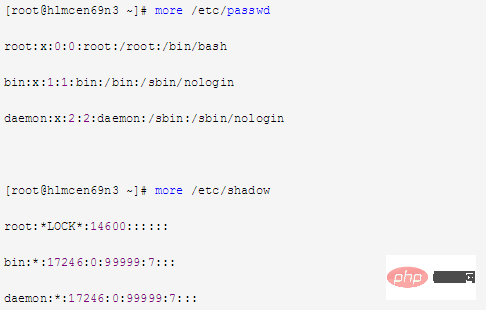
Intrudermay modify username and password files##Can view /etc/passwd and /etc/shadow To identify the file content, related command examples:
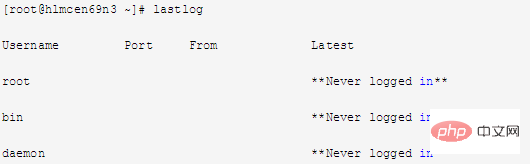
##4
View The latest successful login event of the machine and the last unsuccessful login eventcorresponds to the log "/var/log/lastlog", related command examples:
5
corresponds to the log file "/var/run/utmp", related command examples:
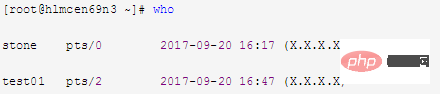
ViewMachineThe corresponding logs of users
who have logged in since the server was created File "/var/log/wtmp", related command examples:
In addition, search the public account Linux to learn how to reply "git books" in the background, and get a surprise gift package.
7
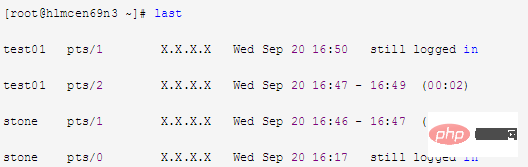
ViewThe connection time (hours) of all users of the machinecorresponds to the log file "/var/log/wtmp", related Command example:
##8
If finds that the machine generates abnormal trafficYou can use the command "tcpdump" to capture network packets to view the traffic situation or use tools" iperf" Check the traffic situation
9
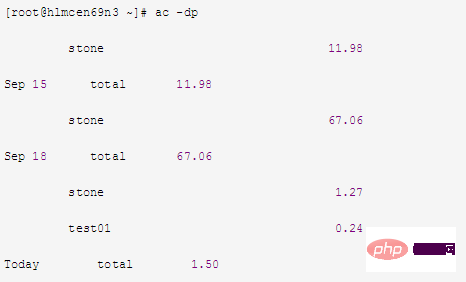
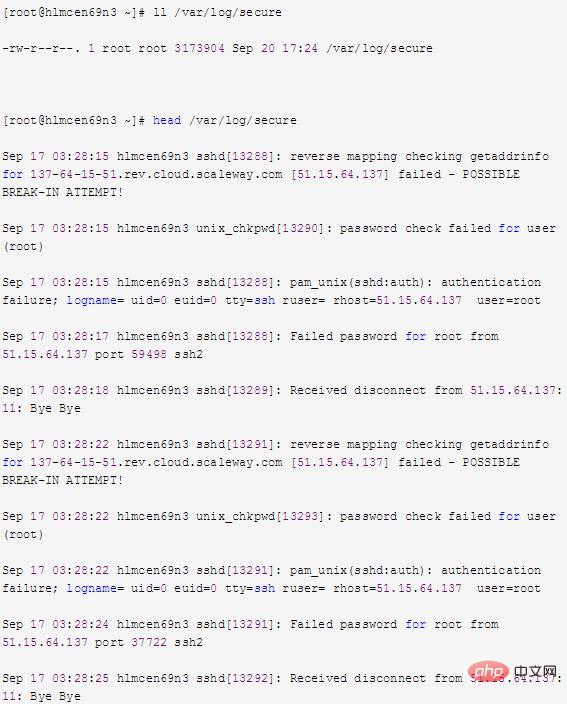
##You can view /var/log/secureLog fileTry to find information about the intruder, related command examples:
10
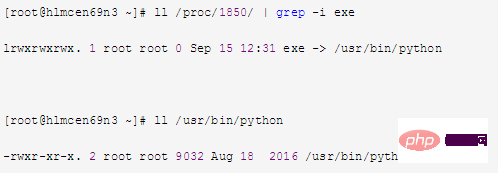
a.top command Check the PID corresponding to the abnormal process
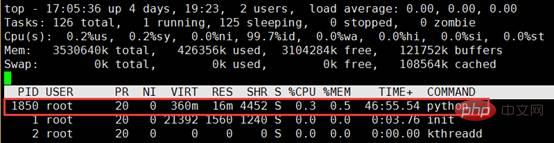
b. Find the executable file of the process in the virtual file system directory Follow Linux Chinese Community
11
If it is confirmed that the machine has been invaded and important files have been deleted, you can try to retrieve the deleted files Note:a. Check the /var/log/secure file and find that the file no longer exists
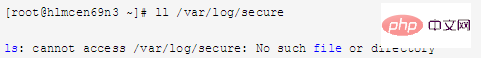
b. Use the lsof command to check whether A process opens /var/log/secure,
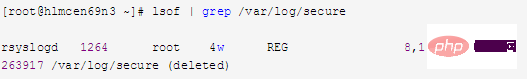
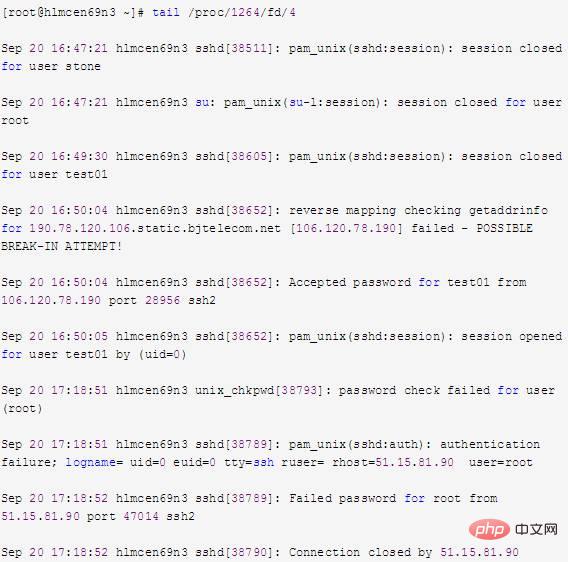
d. As can be seen from the above information, the data to be recovered can be obtained by viewing /proc/1264/fd/4. If the corresponding data can be viewed through the file descriptor, then I/O redirection can be used to redirect it to the file, such as:

# #e. Check /var/log/secure again and find that the file already exists. This method of recovering deleted files is very useful for many applications, especially log files and databases.
The above is the detailed content of Linux - 11 steps to teach you how to perfectly check whether your server has been compromised. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1662
1662
 14
14
 1418
1418
 52
52
 1311
1311
 25
25
 1261
1261
 29
29
 1234
1234
 24
24
 Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
The five basic components of the Linux system are: 1. Kernel, 2. System library, 3. System utilities, 4. Graphical user interface, 5. Applications. The kernel manages hardware resources, the system library provides precompiled functions, system utilities are used for system management, the GUI provides visual interaction, and applications use these components to implement functions.
 vscode terminal usage tutorial
Apr 15, 2025 pm 10:09 PM
vscode terminal usage tutorial
Apr 15, 2025 pm 10:09 PM
vscode built-in terminal is a development tool that allows running commands and scripts within the editor to simplify the development process. How to use vscode terminal: Open the terminal with the shortcut key (Ctrl/Cmd). Enter a command or run the script. Use hotkeys (such as Ctrl L to clear the terminal). Change the working directory (such as the cd command). Advanced features include debug mode, automatic code snippet completion, and interactive command history.
 How to check the warehouse address of git
Apr 17, 2025 pm 01:54 PM
How to check the warehouse address of git
Apr 17, 2025 pm 01:54 PM
To view the Git repository address, perform the following steps: 1. Open the command line and navigate to the repository directory; 2. Run the "git remote -v" command; 3. View the repository name in the output and its corresponding address.
 vscode Previous Next Shortcut Key
Apr 15, 2025 pm 10:51 PM
vscode Previous Next Shortcut Key
Apr 15, 2025 pm 10:51 PM
VS Code One-step/Next step shortcut key usage: One-step (backward): Windows/Linux: Ctrl ←; macOS: Cmd ←Next step (forward): Windows/Linux: Ctrl →; macOS: Cmd →
 What is the main purpose of Linux?
Apr 16, 2025 am 12:19 AM
What is the main purpose of Linux?
Apr 16, 2025 am 12:19 AM
The main uses of Linux include: 1. Server operating system, 2. Embedded system, 3. Desktop operating system, 4. Development and testing environment. Linux excels in these areas, providing stability, security and efficient development tools.
 How to run java code in notepad
Apr 16, 2025 pm 07:39 PM
How to run java code in notepad
Apr 16, 2025 pm 07:39 PM
Although Notepad cannot run Java code directly, it can be achieved by using other tools: using the command line compiler (javac) to generate a bytecode file (filename.class). Use the Java interpreter (java) to interpret bytecode, execute the code, and output the result.
 How to run sublime after writing the code
Apr 16, 2025 am 08:51 AM
How to run sublime after writing the code
Apr 16, 2025 am 08:51 AM
There are six ways to run code in Sublime: through hotkeys, menus, build systems, command lines, set default build systems, and custom build commands, and run individual files/projects by right-clicking on projects/files. The build system availability depends on the installation of Sublime Text.
 laravel installation code
Apr 18, 2025 pm 12:30 PM
laravel installation code
Apr 18, 2025 pm 12:30 PM
To install Laravel, follow these steps in sequence: Install Composer (for macOS/Linux and Windows) Install Laravel Installer Create a new project Start Service Access Application (URL: http://127.0.0.1:8000) Set up the database connection (if required)



