Summary and sharing of three cluster modes of Redis
Recommended learning: Redis video tutorial
Three cluster modes
- redis has three clusters mode, of which master-slave is the most common mode.
- Sentinel Sentinel mode was evolved to make up for the complexity of master-slave switchover after the host in the master-slave replication cluster goes down. As the name suggests, Sentinel is used for monitoring. Its main function is to monitor the master-slave cluster, automatically switch between master and slave, and complete cluster failover.
- cluster mode is the cluster mode officially provided by redis. It uses Sharding technology to not only achieve high availability, read and write separation, but also achieve true distributed storage.
1. Master-slave replication
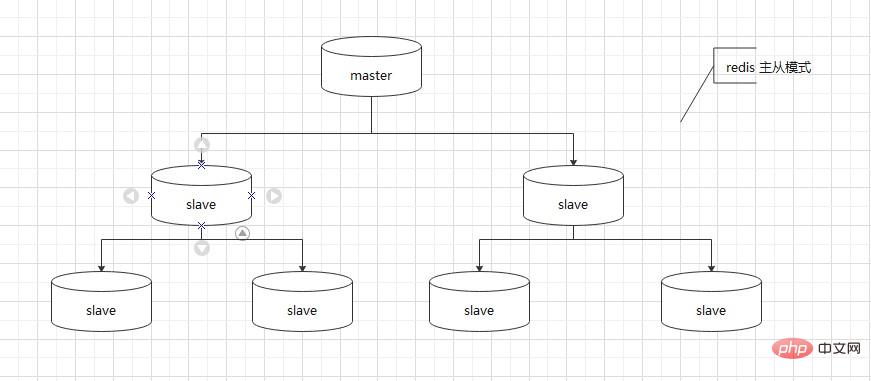
redis master-slave replication
1. reids master-slave mode
2. Redis replication principle
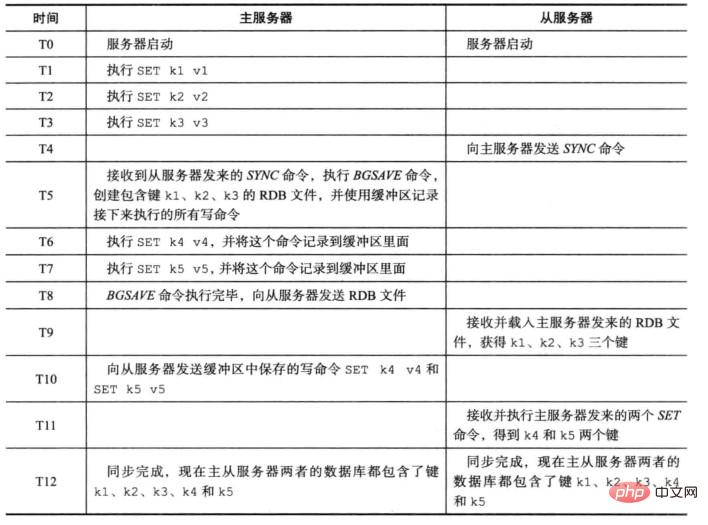
Redis replication is divided into two parts: operation synchronization (SYNC) and command propagate (command propagate)
- Synchronization (SYNC) is used to update the status of the slave server to be consistent with the master server. The vernacular explanation is to actively obtain the data of the main server from the server. Keep your data consistent. The specific implementation is that after receiving the SYNC command, the master server generates an RDB snapshot file and then sends it to the slave server.
- Command propagate (command propagate) is used for command propagation in order to keep the slave server consistent with the master server state after the master server data is modified and the master slave is inconsistent. The vernacular explanation is that after the master server receives the client's data modification command, the database data changes, and the command is cached, and then the cached command is sent to the slave server. The slave server achieves master-slave data consistency by loading the cached command. This is called command propagation.
- Why there are two replication operations of synchronization and command propagation: When there is only synchronization operation, when the slave server sends the SYNC command to the master server, the master server will still receive it when generating the RDB snapshot file. The client's command modifies the data status. If this part of the data cannot be communicated to the slave server, then the master-slave data will be inconsistent. At this time, command propagation occurs. After the master server receives the SYNC command from the slave server, it generates an RDB snapshot file and caches the commands received during this period, and then uses the command propagation operation to send them to the slave server. To achieve master-slave data consistency.
3. Principle of redis master-slave replication
The two operations of redis replication are introduced above, and redis master-slave replication is officially based on synchronization and Command propagation is achieved. The following two pictures show the redis replication process:

##4. Advantages and disadvantages of redis master-slave replication
Advantages: 1. Realizes read-write separation, improves availability, and solves single-machine failures. 2. During master-slave replication, both master and slave are non-blocking and are still available. Disadvantages: 1. During the master downtime, you need to manually switch the host. At the same time, some data cannot be synchronized with the slave server in time, resulting in data inconsistency (manual intervention is required)2. After the slave goes down and multiple slaves are restored, a large number of SYNC synchronizations will cause the master IO pressure to double (the startup time can be manually avoided) 3. Online expansion is complicated. Summary: The advantages of redis master-slave replication are mainly improved availability Disadvantages2. Sentinel Sentinel ModeSentinel Sentinel Sentinel IntroductionSentinel Sentinel is essentially a Redis instance running in a special mode, but the initialization process and work are different from ordinary Redis, and it is essentially a separate process. Sentinel is a high-availability solution for Redis: a Sentinel system (system) composed of one or more Sentinel instances (instances) can monitor any number of master servers and all slave servers under these master servers. , and can automatically switch from the slave server to the master server when the master server goes offline.1. Sentinel system
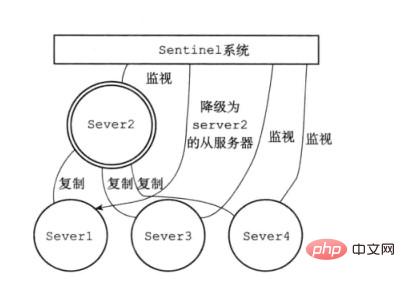
The following figure is a simple Sentinel system architecture diagram. A Sentinel system monitors a master-slave cluster, where server1 is the Redis master server and server2 /3/4 is the Redis slave server. The above master-slave replication is used between master and slave to achieve master-slave consistency. The Sentinel system monitors the entire master-slave cluster.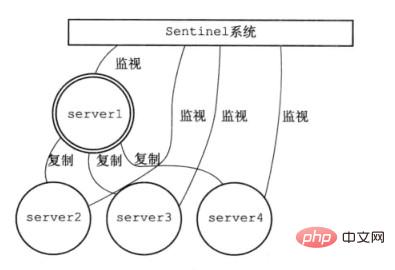
2. Sentinel failover
When the Sentinel system detects that the main server of Server1 is offline, it will terminate server2/3 /4 copy.
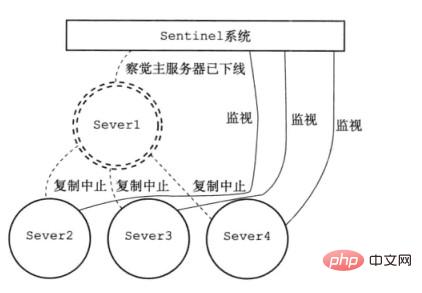
At the same time, Sentinel upgrades server2 to the main server, and server3/4 replicates from the new main server. At the same time, wait for server1 to come online again.
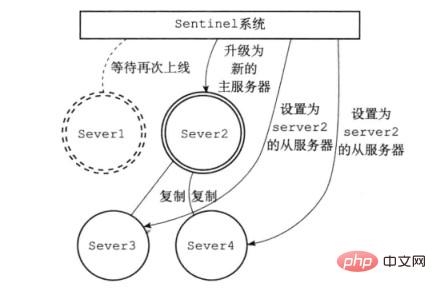
#The Sentinel system can also actively downgrade the main service to a slave server and upgrade the slave server to the master server.
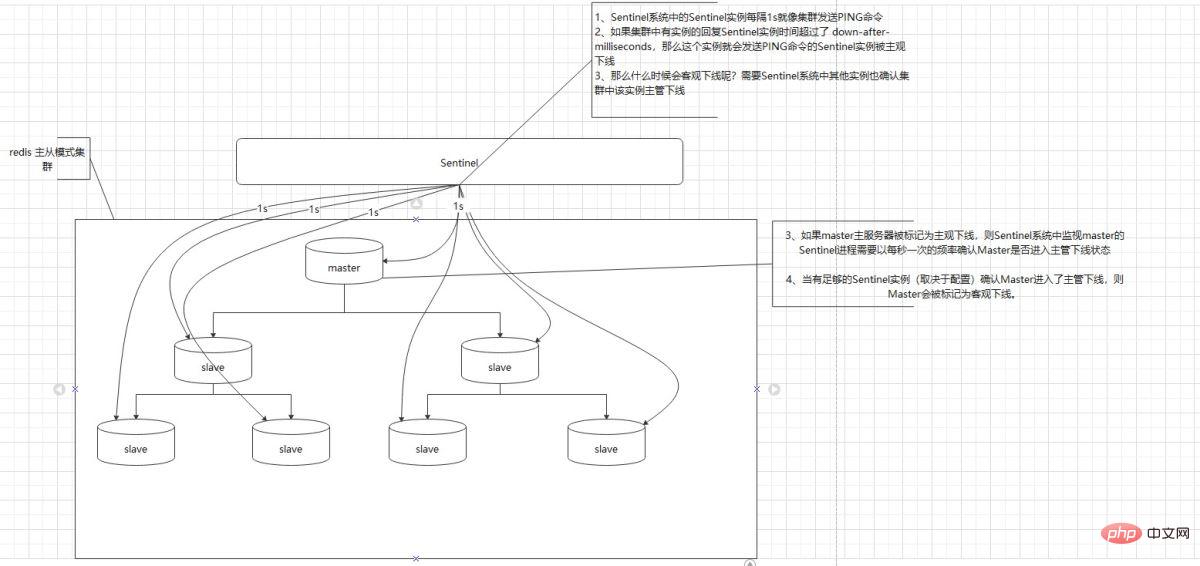
2.1. Sentinel monitoring process
Sentinel monitoring cluster process:
- Command Sentinel to return the redis server to running status by sending commands. Publish and subscribe When the status of the master server changes, Sentinel notifies other slave servers through the
- publish and subscribe mode.
2.2. Sentinel failover
Sentinel failover:
- #1. Sentinel in Sentinel system The instance sends a PING command to the cluster every 1s
- 2. If the reply time of an instance in the cluster to the Sentinel instance exceeds down-after-milliseconds, then this instance will send the PING command. The Sentinel instance is subjectively down Line
- 3. So when will it be objectively offline? Other instances in the Sentinel system need to confirm that the instance supervisor in the cluster is offline.
- If the master server is marked as subjectively offline, the Sentinel process monitoring the master in the Sentinel system needs to confirm whether the master has entered the supervisor offline state once per second.
- 4. If there are enough Sentinel instances (depending on the configuration) to confirm that the Master has entered the supervisory offline state, the Master will be marked as objectively offline.
3. Sentinel advantages and disadvantages
Advantages:
1. Sentinel mode is based on master-slave replication, so Sentinel has all the advantages of master-slave replication. 2. Sentinel has master-slave switching and failover, so the cluster has higher availability
Disadvantages:
1. Redis is difficult to support online expansion, and online expansion is more complicated.
Summary:
sentinel is mainly used to monitor the redis master-slave cluster and improve the availability of the redis master-slave cluster.
3. Cluster mode
redis cluster
1. reids cluster
Redis Cluster is a kind of server Sharding Technology, redis version 3.0 is officially available.
Sentinel has basically achieved high availability, but each machine stores the same content, which wastes memory, so Redis Cluster implements distributed storage. Different content is stored on each machine node.
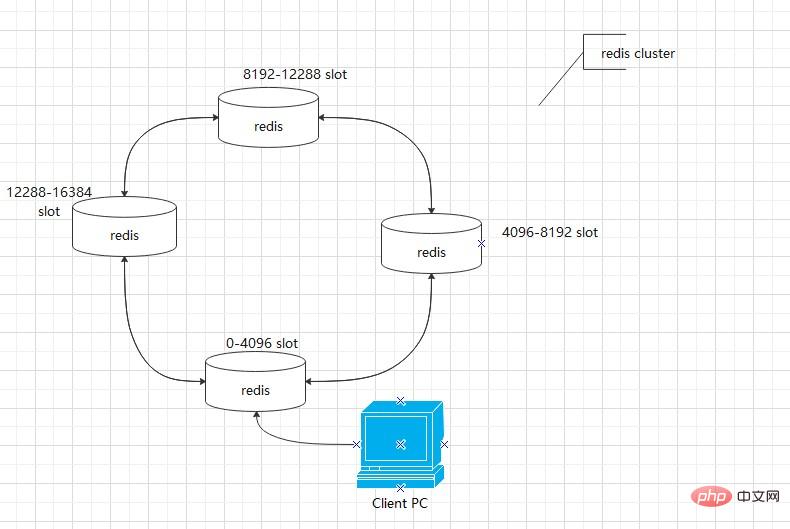
#2. Redis Cluster data sharding principle
redis data sharding uses hash slot, redis cluster There are 16384 hash slots. Each Key is checked modulo 16384 after passing the CRC16 check to determine which slot to place.
When accessing the redis key, redis will obtain a result based on the CRC16 algorithm, and then calculate the remainder of the result and 16384, and use this value to obtain the data from the corresponding node.
At this time, the application client actually only needs to connect to any one of the nodes, and then each node in the Redis Cluster saves the slot information of other nodes. In this way, after the access key calculates the slot, the node information is obtained from the configuration by saving the slot information, and then the corresponding node is retrieved to obtain the data.
3. Redis Cluster replication principle
The redis-cluster cluster introduces the master-slave replication model. One master node corresponds to one or more slave nodes. When the master node When a node goes down, the slave node will be enabled. When other master nodes ping a master node A, if more than half of the master nodes communicate with A times out, then the master node A is considered to be down. If both master node A and its slave node A1 are down, then the cluster can no longer provide services
Recommended learning:Redis video tutorial
The above is the detailed content of Summary and sharing of three cluster modes of Redis. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1666
1666
 14
14
 1425
1425
 52
52
 1327
1327
 25
25
 1273
1273
 29
29
 1253
1253
 24
24
 How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
Redis cluster mode deploys Redis instances to multiple servers through sharding, improving scalability and availability. The construction steps are as follows: Create odd Redis instances with different ports; Create 3 sentinel instances, monitor Redis instances and failover; configure sentinel configuration files, add monitoring Redis instance information and failover settings; configure Redis instance configuration files, enable cluster mode and specify the cluster information file path; create nodes.conf file, containing information of each Redis instance; start the cluster, execute the create command to create a cluster and specify the number of replicas; log in to the cluster to execute the CLUSTER INFO command to verify the cluster status; make
 How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear Redis data: Use the FLUSHALL command to clear all key values. Use the FLUSHDB command to clear the key value of the currently selected database. Use SELECT to switch databases, and then use FLUSHDB to clear multiple databases. Use the DEL command to delete a specific key. Use the redis-cli tool to clear the data.
 How to read redis queue
Apr 10, 2025 pm 10:12 PM
How to read redis queue
Apr 10, 2025 pm 10:12 PM
To read a queue from Redis, you need to get the queue name, read the elements using the LPOP command, and process the empty queue. The specific steps are as follows: Get the queue name: name it with the prefix of "queue:" such as "queue:my-queue". Use the LPOP command: Eject the element from the head of the queue and return its value, such as LPOP queue:my-queue. Processing empty queues: If the queue is empty, LPOP returns nil, and you can check whether the queue exists before reading the element.
 How to configure Lua script execution time in centos redis
Apr 14, 2025 pm 02:12 PM
How to configure Lua script execution time in centos redis
Apr 14, 2025 pm 02:12 PM
On CentOS systems, you can limit the execution time of Lua scripts by modifying Redis configuration files or using Redis commands to prevent malicious scripts from consuming too much resources. Method 1: Modify the Redis configuration file and locate the Redis configuration file: The Redis configuration file is usually located in /etc/redis/redis.conf. Edit configuration file: Open the configuration file using a text editor (such as vi or nano): sudovi/etc/redis/redis.conf Set the Lua script execution time limit: Add or modify the following lines in the configuration file to set the maximum execution time of the Lua script (unit: milliseconds)
 How to use the redis command line
Apr 10, 2025 pm 10:18 PM
How to use the redis command line
Apr 10, 2025 pm 10:18 PM
Use the Redis command line tool (redis-cli) to manage and operate Redis through the following steps: Connect to the server, specify the address and port. Send commands to the server using the command name and parameters. Use the HELP command to view help information for a specific command. Use the QUIT command to exit the command line tool.
 How to implement redis counter
Apr 10, 2025 pm 10:21 PM
How to implement redis counter
Apr 10, 2025 pm 10:21 PM
Redis counter is a mechanism that uses Redis key-value pair storage to implement counting operations, including the following steps: creating counter keys, increasing counts, decreasing counts, resetting counts, and obtaining counts. The advantages of Redis counters include fast speed, high concurrency, durability and simplicity and ease of use. It can be used in scenarios such as user access counting, real-time metric tracking, game scores and rankings, and order processing counting.
 How to set the redis expiration policy
Apr 10, 2025 pm 10:03 PM
How to set the redis expiration policy
Apr 10, 2025 pm 10:03 PM
There are two types of Redis data expiration strategies: periodic deletion: periodic scan to delete the expired key, which can be set through expired-time-cap-remove-count and expired-time-cap-remove-delay parameters. Lazy Deletion: Check for deletion expired keys only when keys are read or written. They can be set through lazyfree-lazy-eviction, lazyfree-lazy-expire, lazyfree-lazy-user-del parameters.
 How to optimize the performance of debian readdir
Apr 13, 2025 am 08:48 AM
How to optimize the performance of debian readdir
Apr 13, 2025 am 08:48 AM
In Debian systems, readdir system calls are used to read directory contents. If its performance is not good, try the following optimization strategy: Simplify the number of directory files: Split large directories into multiple small directories as much as possible, reducing the number of items processed per readdir call. Enable directory content caching: build a cache mechanism, update the cache regularly or when directory content changes, and reduce frequent calls to readdir. Memory caches (such as Memcached or Redis) or local caches (such as files or databases) can be considered. Adopt efficient data structure: If you implement directory traversal by yourself, select more efficient data structures (such as hash tables instead of linear search) to store and access directory information





