 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Internet Message Control Protocol ICMP: A Scout of Network Time
Internet Message Control Protocol ICMP: A Scout of Network Time
Internet Message Control Protocol ICMP: A Scout of Network Time
When we want to test the connectivity between two hosts, we often use the ping command to verify. But do you know the connection between this command and the icmp protocol?
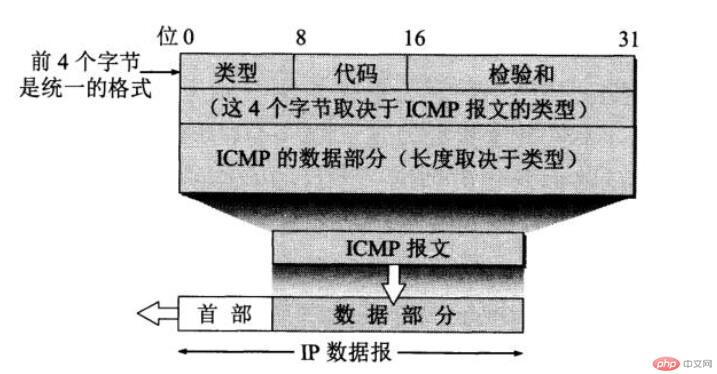
ICMP is the Internet Message Control Protocol, which is used to report error conditions and related error information. The icmp data message is encapsulated in the ip datagram as its data part. However, like the ip protocol, icmp is also a network layer protocol. The following figure is an icmp message format diagram:
ICMP message type
ICMP message total are divided into two categories, namely error report messages and inquiry messages.
Error report messages mainly include the following types:
The destination is unreachable (type value is 3): When the host or router cannot deliver data, this message is sent to the source point.
Timeout (type value is 11): When the TTL value in the IP datagram is 0, or the delivery is not successful within the specified time, a timeout message is sent to the source point.
Parameter problem (type value is 12): When there are incorrect fields in the header of the received datagram, the data packet will be discarded and a parameter problem message will be sent to the source point.
Redirect (type value is 5): When the router receives the packet, it will be more efficient to know that the destination address should be forwarded from another router. Then after it forwards the packet, it also forwards the packet to the source. Click to send the redirect message. Then the next datagram with the same destination address will go from another router.
Next, let’s look at the inquiry message, which mainly falls into one category: response request message (type value is 8) and reply message (type value is 0). The host that receives the response request message must Return a reply message.
An application of ICMP: ping command
After understanding some knowledge of ICMP, let’s take a look at an example of applying ICMP— —ping command. This command is not only available on Linux systems, but also on Windows systems
ping baidu.com
正在 Ping baidu.com [220.181.38.148] 具有 32 字节的数据:
来自 220.181.38.148 的回复: 字节=32 时间=32ms TTL=52
来自 220.181.38.148 的回复: 字节=32 时间=29ms TTL=52
来自 220.181.38.148 的回复: 字节=32 时间=27ms TTL=52
来自 220.181.38.148 的回复: 字节=32 时间=35ms TTL=52
220.181.38.148 的 Ping 统计信息:
数据包: 已发送 = 4,已接收 = 4,丢失 = 0 (0% 丢失),
往返行程的估计时间(以毫秒为单位):
最短 = 27ms,最长 = 35ms,平均 = 30msLet’s take a look at the workflow of the ping command: First, my host generates four ICMP messages, and these four ICMP messages are responses. request message and send these four ICMP messages to the Baidu server. If the Baidu server can receive these four ICMP messages, then it will also send four ICMP reply messages to my host. Therefore, my host can calculate the packet loss rate and round-trip time based on the number of ICMP datagrams returned and the return time.
Recommended: "linux video tutorial"
The above is the detailed content of Internet Message Control Protocol ICMP: A Scout of Network Time. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1655
1655
 14
14
 1414
1414
 52
52
 1307
1307
 25
25
 1255
1255
 29
29
 1228
1228
 24
24
 Where to view the logs of Tigervnc on Debian
Apr 13, 2025 am 07:24 AM
Where to view the logs of Tigervnc on Debian
Apr 13, 2025 am 07:24 AM
In Debian systems, the log files of the Tigervnc server are usually stored in the .vnc folder in the user's home directory. If you run Tigervnc as a specific user, the log file name is usually similar to xf:1.log, where xf:1 represents the username. To view these logs, you can use the following command: cat~/.vnc/xf:1.log Or, you can open the log file using a text editor: nano~/.vnc/xf:1.log Please note that accessing and viewing log files may require root permissions, depending on the security settings of the system.
 How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
The readdir function in the Debian system is a system call used to read directory contents and is often used in C programming. This article will explain how to integrate readdir with other tools to enhance its functionality. Method 1: Combining C language program and pipeline First, write a C program to call the readdir function and output the result: #include#include#include#includeintmain(intargc,char*argv[]){DIR*dir;structdirent*entry;if(argc!=2){
 Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
The five basic components of the Linux system are: 1. Kernel, 2. System library, 3. System utilities, 4. Graphical user interface, 5. Applications. The kernel manages hardware resources, the system library provides precompiled functions, system utilities are used for system management, the GUI provides visual interaction, and applications use these components to implement functions.
 How to interpret the output results of Debian Sniffer
Apr 12, 2025 pm 11:00 PM
How to interpret the output results of Debian Sniffer
Apr 12, 2025 pm 11:00 PM
DebianSniffer is a network sniffer tool used to capture and analyze network packet timestamps: displays the time for packet capture, usually in seconds. Source IP address (SourceIP): The network address of the device that sent the packet. Destination IP address (DestinationIP): The network address of the device receiving the data packet. SourcePort: The port number used by the device sending the packet. Destinatio
 How to recycle packages that are no longer used
Apr 13, 2025 am 08:51 AM
How to recycle packages that are no longer used
Apr 13, 2025 am 08:51 AM
This article describes how to clean useless software packages and free up disk space in the Debian system. Step 1: Update the package list Make sure your package list is up to date: sudoaptupdate Step 2: View installed packages Use the following command to view all installed packages: dpkg--get-selections|grep-vdeinstall Step 3: Identify redundant packages Use the aptitude tool to find packages that are no longer needed. aptitude will provide suggestions to help you safely delete packages: sudoaptitudesearch '~pimportant' This command lists the tags
 Key Linux Operations: A Beginner's Guide
Apr 09, 2025 pm 04:09 PM
Key Linux Operations: A Beginner's Guide
Apr 09, 2025 pm 04:09 PM
Linux beginners should master basic operations such as file management, user management and network configuration. 1) File management: Use mkdir, touch, ls, rm, mv, and CP commands. 2) User management: Use useradd, passwd, userdel, and usermod commands. 3) Network configuration: Use ifconfig, echo, and ufw commands. These operations are the basis of Linux system management, and mastering them can effectively manage the system.
 How to monitor Nginx SSL performance on Debian
Apr 12, 2025 pm 10:18 PM
How to monitor Nginx SSL performance on Debian
Apr 12, 2025 pm 10:18 PM
This article describes how to effectively monitor the SSL performance of Nginx servers on Debian systems. We will use NginxExporter to export Nginx status data to Prometheus and then visually display it through Grafana. Step 1: Configuring Nginx First, we need to enable the stub_status module in the Nginx configuration file to obtain the status information of Nginx. Add the following snippet in your Nginx configuration file (usually located in /etc/nginx/nginx.conf or its include file): location/nginx_status{stub_status
 How to install PHPStorm in Debian system
Apr 13, 2025 am 06:03 AM
How to install PHPStorm in Debian system
Apr 13, 2025 am 06:03 AM
Install PHPStorm on the Debian system to easily solve your PHP development environment! The following steps will guide you through the entire installation process. Installation steps: Download PHPStorm: Visit the official website of JetBrains and download the latest version of PHPStorm. Unzip the installation package: After downloading using wget or curl, unzip it to the specified directory (for example /opt). Command example: wgethttps://download.jetbrains.com/phpstorm/phpstorm-2024.3.5.tar.gztar-xzfphpstorm-2024.3.5.tar.gz



