Computer Level 3 Network Technology Knowledge Points

1. LAN is divided into wired medium LAN and wireless medium according to the type of transmission medium.
LAN The early computer network was mainly wide area network, divided into Main computers and terminals (responsible for data processing) and communication processing equipment and communication circuits (responsible for data communication processing).
2. The computer network is logically divided into resource subnets and communication subnets
Resource subnets (computer systems, terminals, external network equipment and software information Resources; Responsible for the data processing business of the entire network, providing network resources and services.
Communication subnet (communication processing control machine - i.e. network nodes, communication lines and other communication equipment): responsible for network data transmission, forwarding and other communications Handle task network access (LAN, wireless LAN, wireless metropolitan area network, telephone switching network, cable TV network).
3. The core device of the switching LAN is the LAN switch
Metropolitan area network concept: Network operators provide various information services within the city, using the broadband optical transmission network as an open platform and the promotion of dense wavelength division multiplexing technology based on the TCPIP protocol, resulting in the expansion of the bandwidth of the WAN backbone line.
The metropolitan area network is divided into core switching layer (high-speed data exchange), edge aggregation layer (routing and traffic aggregation), and user access layer (user access and local traffic control).
4. Advantages of hierarchical structureClear layer positioning, open interfaces, standard specifications, easy to set up and manage.
5. Basic functions of the core layer
(Design focus: reliability, scalability, openness) Connect to the aggregation layer, provide high-speed packet forwarding, and provide a high-speed secure QoS guaranteed transmission environment; realize backbone network interconnection and provide urban broadband IP data Exit; provides routing services required for users to access the INTERNET.
6. Basic functions of the aggregation layer
Aggregation of access layer user traffic, aggregation of data packet transmission, forwarding and Switching; local route filtering, traffic balancing, QoS priority management, security control, IP address translation, traffic shaping; forwarding traffic to the core layer or local routing for processing.
7. Establish and operate a broadband metropolitan area network Principles: operability, manageability, profitability, scalability.
Key technologies for management and operation of broadband metropolitan area networks: bandwidth management, quality of service QoS, network management, user management, Multi-service access, statistics and billing, IP address allocation and address translation, network security.
The broadband metropolitan area network must comply with carrier-level operation requirements (consider equipment redundancy, line redundancy) in the construction plan and rapid diagnosis and self-recovery of system faults).
Quality of service QoS technology: resource reservation [SD2], differentiated services [SD3], multi-protocol label conversion [SD4].
Management There are three basic solutions for bandwidth metropolitan area networks: in-band network management, out-of-band network management [SD5], and both in-band and out-of-band network management are used.
The above is the detailed content of Computer Level 3 Network Technology Knowledge Points. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1662
1662
 14
14
 1419
1419
 52
52
 1311
1311
 25
25
 1262
1262
 29
29
 1235
1235
 24
24
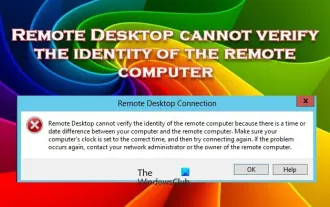 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
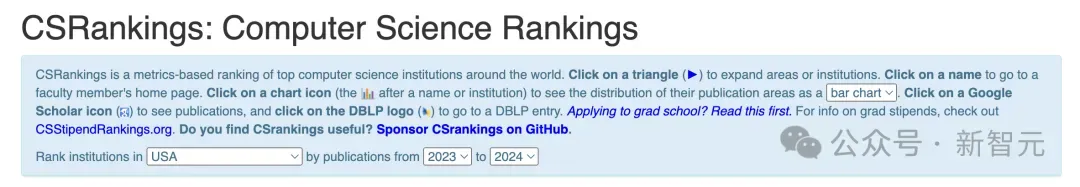 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
 Python cheat sheet collection, what knowledge points have you mastered?
Apr 26, 2023 pm 10:49 PM
Python cheat sheet collection, what knowledge points have you mastered?
Apr 26, 2023 pm 10:49 PM
Python is currently the most popular programming language. I believe that a large number of novice friends will join the ranks of learning every day. However, no matter how easy a language is to learn, there are still many basic concepts and basic knowledge. For a novice, it is still difficult to master so many in one time. Today, we have collected many Python-related knowledge cheat sheets, which can be said to be all-inclusive. In the future, mom will no longer have to worry about everyone not being able to remember any knowledge points! Python basics Pythonbasics This cheat sheet contains all the basic knowledge of Python, from variable data types to list strings, from environment installation to the use of commonly used libraries, it can be said to be comprehensive. Beginner'sPytho
 What is e in computer
Aug 31, 2023 am 09:36 AM
What is e in computer
Aug 31, 2023 am 09:36 AM
The "e" of computer is the scientific notation symbol. The letter "e" is used as the exponent separator in scientific notation, which means "multiplied to the power of 10". In scientific notation, a number is usually written as M × 10^E, where M is a number between 1 and 10 and E represents the exponent.
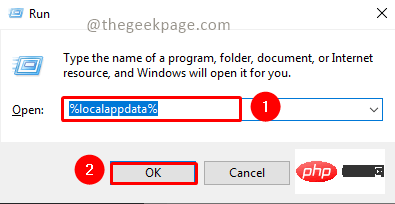 Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
<p>MSTeams is the trusted platform to communicate, chat or call with teammates and colleagues. Error code 80090016 on MSTeams and the message <strong>Your computer's Trusted Platform Module has failed</strong> may cause difficulty logging in. The app will not allow you to log in until the error code is resolved. If you encounter such messages while opening MS Teams or any other Microsoft application, then this article can guide you to resolve the issue. </p><h2&
 What does computer cu mean?
Aug 15, 2023 am 09:58 AM
What does computer cu mean?
Aug 15, 2023 am 09:58 AM
The meaning of cu in a computer depends on the context: 1. Control Unit, in the central processor of a computer, CU is the component responsible for coordinating and controlling the entire computing process; 2. Compute Unit, in a graphics processor or other accelerated processor, CU is the basic unit for processing parallel computing tasks.
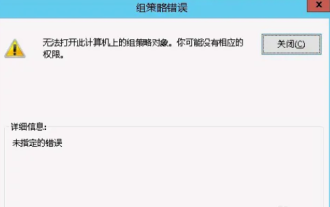 Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Occasionally, the operating system may malfunction when using a computer. The problem I encountered today was that when accessing gpedit.msc, the system prompted that the Group Policy object could not be opened because the correct permissions may be lacking. The Group Policy object on this computer could not be opened. Solution: 1. When accessing gpedit.msc, the system prompts that the Group Policy object on this computer cannot be opened because of lack of permissions. Details: The system cannot locate the path specified. 2. After the user clicks the close button, the following error window pops up. 3. Check the log records immediately and combine the recorded information to find that the problem lies in the C:\Windows\System32\GroupPolicy\Machine\registry.pol file
 What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
Solution to the problem that steam cannot connect to the remote computer: 1. In the game platform, click the "steam" option in the upper left corner; 2. Open the menu and select the "Settings" option; 3. Select the "Remote Play" option; 4. Check Activate the "Remote Play" function and click the "OK" button.



