 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Specify the inbound access permissions of the security group to allow or deny other devices to send inbound traffic to instances in the security group.
Specify the inbound access permissions of the security group to allow or deny other devices to send inbound traffic to instances in the security group.
Specify the inbound access permissions of the security group to allow or deny other devices to send inbound traffic to instances in the security group.
This article introduces the specific access rights of the security group in the inbound direction, allowing or denying other devices to send inbound traffic to the security group. It focuses on the specific steps. The content of this article is compact. I hope you can learn something. reward.
AuthorizeSecurityGroup
Add a security group inbound rule. Specify the inbound access permissions of the security group to allow or deny other devices to send inbound traffic to instances in the security group.
Description
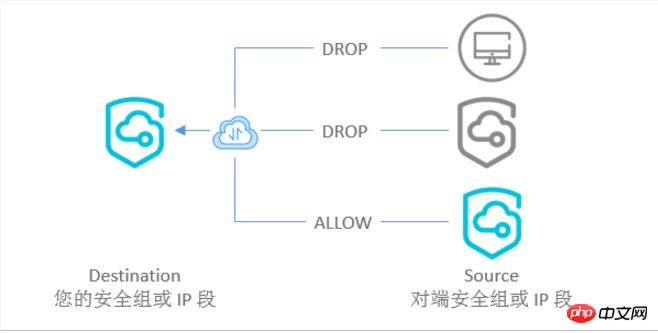
We define the initiating end of the inbound traffic as the source end (Source), and the receiving end of the data transmission as the destination end (Destination) ),As shown below.
When calling this interface, you need to understand:
A security group can have up to 100 security group rules.
Security group rules are divided into two categories: accept access (accept) and deny access (drop).
The security group rule priority (Priority) optional range is [1, 100]. The smaller the number, the higher the priority.
Among security group rules with the same priority, rules that deny access (drop) take precedence.
The source device can be a specified IP address range (SourceCidrIp) or an instance in another security group (SourceGroupId).
Any set of parameters below can determine a security group rule. Specifying only one parameter cannot determine a security group rule. If a matching security group rule already exists, this call to AuthorizeSecurityGroup fails.
Set the access permissions for the specified IP address segment, such as request example 1: IpProtocol, PortRange, (optional) SourcePortRange, NicType, Policy, (optional) DestCiderIp and SourceCidrIp
Set other security The access rights of the group, such as request example 2: IpProtocol, PortRange, (optional) SourcePortRange, NicType, Policy, (optional) DestCiderIp, SourceGroupOwnerAccount and SourceGroupId
Request parameters 
Return parameters
are all public return parameters. See Public Parameters.
Example
For more examples of setting security group rules, please refer to Application Cases, Typical Applications of Security Group Rules and Security Group Five An introduction to tuple rules.
Request Example 1
Set the access permissions for the specified IP address range. At this time, the network card type (NicType) of the classic network type security group can be set to public network (internet) and intranet (intranet). The network card type (NicType) of the VPC type security group can only be set to the intranet.
https://ecs.aliyuncs.com/?Action=AuthorizeSecurityGroup &SecurityGroupId=sg-F876FF7BA &SourceCidrIp=0.0.0.0/0 &IpProtocol=tcp &PortRange=1/65535 &NicType=intranet &Policy=Allow &<公共请求参数>
Request example two
Set the access permissions of other security groups. At this time, the network card type (NicType) can only be intranet. When security groups of the classic network type communicate with each other, you can set the access permissions of other security groups in the same region to your security group. This security group can be yours or another Alibaba Cloud account (SourceGroupOwnerAccount). When VPC security groups communicate with each other, you can set the access permissions of other security groups in the same VPC to this security group.
https://ecs.aliyuncs.com/?Action=AuthorizeSecurityGroup &SecurityGroupId=sg-F876FF7BA &SourceGroupId=sg-1651FBB64 &SourceGroupOwnerAccount=test@aliyun.com &IpProtocol=tcp &PortRange=1/65535 &NicType=intranet &Policy=Drop &<公共请求参数>
Return example
XML format
<AuthorizeSecurityGroupResponse>
<RequestId>CEF72CEB-54B6-4AE8-B225-F876FF7BA984</RequestId>
</AuthorizeSecurityGroupResponse>JSON format
{
"RequestId":"CEF72CEB-54B6-4AE8-B225-F876FF7BA984"
}Error codes
The following are the error codes unique to this interface. For more error codes, please visit the API Error Center. 
The above is the detailed content of Specify the inbound access permissions of the security group to allow or deny other devices to send inbound traffic to instances in the security group.. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1659
1659
 14
14
 1416
1416
 52
52
 1310
1310
 25
25
 1259
1259
 29
29
 1233
1233
 24
24
 Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
The five basic components of the Linux system are: 1. Kernel, 2. System library, 3. System utilities, 4. Graphical user interface, 5. Applications. The kernel manages hardware resources, the system library provides precompiled functions, system utilities are used for system management, the GUI provides visual interaction, and applications use these components to implement functions.
 vscode terminal usage tutorial
Apr 15, 2025 pm 10:09 PM
vscode terminal usage tutorial
Apr 15, 2025 pm 10:09 PM
vscode built-in terminal is a development tool that allows running commands and scripts within the editor to simplify the development process. How to use vscode terminal: Open the terminal with the shortcut key (Ctrl/Cmd). Enter a command or run the script. Use hotkeys (such as Ctrl L to clear the terminal). Change the working directory (such as the cd command). Advanced features include debug mode, automatic code snippet completion, and interactive command history.
 How to check the warehouse address of git
Apr 17, 2025 pm 01:54 PM
How to check the warehouse address of git
Apr 17, 2025 pm 01:54 PM
To view the Git repository address, perform the following steps: 1. Open the command line and navigate to the repository directory; 2. Run the "git remote -v" command; 3. View the repository name in the output and its corresponding address.
 Where to write code in vscode
Apr 15, 2025 pm 09:54 PM
Where to write code in vscode
Apr 15, 2025 pm 09:54 PM
Writing code in Visual Studio Code (VSCode) is simple and easy to use. Just install VSCode, create a project, select a language, create a file, write code, save and run it. The advantages of VSCode include cross-platform, free and open source, powerful features, rich extensions, and lightweight and fast.
 vscode terminal command cannot be used
Apr 15, 2025 pm 10:03 PM
vscode terminal command cannot be used
Apr 15, 2025 pm 10:03 PM
Causes and solutions for the VS Code terminal commands not available: The necessary tools are not installed (Windows: WSL; macOS: Xcode command line tools) Path configuration is wrong (add executable files to PATH environment variables) Permission issues (run VS Code as administrator) Firewall or proxy restrictions (check settings, unrestrictions) Terminal settings are incorrect (enable use of external terminals) VS Code installation is corrupt (reinstall or update) Terminal configuration is incompatible (try different terminal types or commands) Specific environment variables are missing (set necessary environment variables)
 vscode Previous Next Shortcut Key
Apr 15, 2025 pm 10:51 PM
vscode Previous Next Shortcut Key
Apr 15, 2025 pm 10:51 PM
VS Code One-step/Next step shortcut key usage: One-step (backward): Windows/Linux: Ctrl ←; macOS: Cmd ←Next step (forward): Windows/Linux: Ctrl →; macOS: Cmd →
 What is the main purpose of Linux?
Apr 16, 2025 am 12:19 AM
What is the main purpose of Linux?
Apr 16, 2025 am 12:19 AM
The main uses of Linux include: 1. Server operating system, 2. Embedded system, 3. Desktop operating system, 4. Development and testing environment. Linux excels in these areas, providing stability, security and efficient development tools.
 How to run sublime after writing the code
Apr 16, 2025 am 08:51 AM
How to run sublime after writing the code
Apr 16, 2025 am 08:51 AM
There are six ways to run code in Sublime: through hotkeys, menus, build systems, command lines, set default build systems, and custom build commands, and run individual files/projects by right-clicking on projects/files. The build system availability depends on the installation of Sublime Text.



