 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Analysis of SQL injection vulnerability drag library principle for sql security_PHP tutorial
Analysis of SQL injection vulnerability drag library principle for sql security_PHP tutorial
Analysis of SQL injection vulnerability drag library principle for sql security_PHP tutorial
This article uses some of my own experience to tell you how hacker friends will use the SQL vulnerability of your database to download your database. Please refer to this article if necessary.
Create a table in the database:
| The code is as follows | Copy code | ||||||||
`articleid` int(11) NOT NULL AUTO_INCREMENT, `title` varchar(100) CHARACTER SET utf8 NOT NULL DEFAULT '', `content` text CHARACTER SET utf8 NOT NULL, PRIMARY KEY (`articleid`)
) ENGINE=MyISAM AUTO_INCREMENT=7 DEFAULT CHARSET=latin1; |
|||||||||
| 代码如下 | 复制代码 |
|
http://127.0.0.1/marcofly/phpstudy/sqlinsert/showart.php?id=1 |
|
Next, write a page that handles user requests. Here, we deliberately do not filter the data submitted by the user, leaving a SQL injection vulnerability for testing.
The code is as follows:
| The code is as follows | Copy code | ||||
 $servername = "localhost"; $servername = "localhost";
$dbusername = "root"; $dbpassword = "";
Drag library using SQL injection vulnerability ";
if (!$row){
echo "The record does not exist";
exit;
}
echo "title ";
echo "Content "; ?> |
|||||
| The code is as follows | Copy code |
| http://127.0.0.1/marcofly/phpstudy/sqlinsert/showart.php?id=1 | |
Analysis: %23 is the ASCII code of #. Since entering # directly in the address bar will become empty in the database system, you need to enter %23 in the address bar, then it will become # and then be commented out. The following sql statement.
After running, open the E drive and find an additional sql.txt file. After opening, there is a record in the table article.
Why is there only one record? Does this data table only have one record? This is not the case, because we only retrieve one record with id 1, so can we download all the records in the article table at once?
The answer is yes, as long as your constructed SQL statement is flexible enough (again, the flexibility of constructed SQL statements is brought up).
Analysis, when you enter 'into outfile 'e:/sql.txt'%23 in the URL address bar, it is merged into the sql query statement and becomes:
The code is as follows
|
Copy code
|
||||||||
|
After careful analysis, we can construct the SQL statement like this:
In this case, the WHERE clause is always true no matter what. In other words, the sql statement is equivalent to the following:
Understood, the sql statement first executes the select statement to retrieve all the contents in the table article, and then executes into outfile 'e:/whf.txt'#' to export the contents.
|
|||||||||
http: //www.bkjia.com/PHPjc/632941.html

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1662
1662
 14
14
 1419
1419
 52
52
 1313
1313
 25
25
 1262
1262
 29
29
 1235
1235
 24
24
 Canada plans to ban hacking tool Flipper Zero as car theft problem surges
Jul 17, 2024 am 03:06 AM
Canada plans to ban hacking tool Flipper Zero as car theft problem surges
Jul 17, 2024 am 03:06 AM
This website reported on February 12 that the Canadian government plans to ban the sale of hacking tool FlipperZero and similar devices because they are labeled as tools that thieves can use to steal cars. FlipperZero is a portable programmable test tool that helps test and debug various hardware and digital devices through multiple protocols, including RFID, radio, NFC, infrared and Bluetooth, and has won the favor of many geeks and hackers. Since the release of the product, users have demonstrated FlipperZero's capabilities on social media, including using replay attacks to unlock cars, open garage doors, activate doorbells and clone various digital keys. ▲FlipperZero copies the McLaren keychain and unlocks the car Canadian Industry Minister Franço
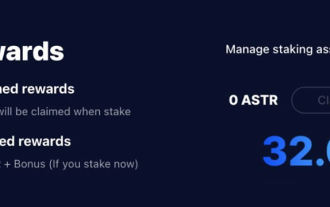 Astar staking principle, income dismantling, airdrop projects and strategies & operation nanny-level strategy
Jun 25, 2024 pm 07:09 PM
Astar staking principle, income dismantling, airdrop projects and strategies & operation nanny-level strategy
Jun 25, 2024 pm 07:09 PM
Table of Contents Astar Dapp Staking Principle Staking Revenue Dismantling of Potential Airdrop Projects: AlgemNeurolancheHealthreeAstar Degens DAOVeryLongSwap Staking Strategy & Operation "AstarDapp Staking" has been upgraded to the V3 version at the beginning of this year, and many adjustments have been made to the staking revenue rules. At present, the first staking cycle has ended, and the "voting" sub-cycle of the second staking cycle has just begun. To obtain the "extra reward" benefits, you need to grasp this critical stage (expected to last until June 26, with less than 5 days remaining). I will break down the Astar staking income in detail,
 PHP Microframework: Security Discussion of Slim and Phalcon
Jun 04, 2024 am 09:28 AM
PHP Microframework: Security Discussion of Slim and Phalcon
Jun 04, 2024 am 09:28 AM
In the security comparison between Slim and Phalcon in PHP micro-frameworks, Phalcon has built-in security features such as CSRF and XSS protection, form validation, etc., while Slim lacks out-of-the-box security features and requires manual implementation of security measures. For security-critical applications, Phalcon offers more comprehensive protection and is the better choice.
 How should the Java framework security architecture design be balanced with business needs?
Jun 04, 2024 pm 02:53 PM
How should the Java framework security architecture design be balanced with business needs?
Jun 04, 2024 pm 02:53 PM
Java framework design enables security by balancing security needs with business needs: identifying key business needs and prioritizing relevant security requirements. Develop flexible security strategies, respond to threats in layers, and make regular adjustments. Consider architectural flexibility, support business evolution, and abstract security functions. Prioritize efficiency and availability, optimize security measures, and improve visibility.
 Which wallet is safer for SHIB coins? (Must read for newbies)
Jun 05, 2024 pm 01:30 PM
Which wallet is safer for SHIB coins? (Must read for newbies)
Jun 05, 2024 pm 01:30 PM
SHIB coin is no longer unfamiliar to investors. It is a conceptual token of the same type as Dogecoin. With the development of the market, SHIB’s current market value has ranked 12th. It can be seen that the SHIB market is hot and attracts countless investments. investors participate in investment. In the past, there have been frequent transactions and wallet security incidents in the market. Many investors have been worried about the storage problem of SHIB. They wonder which wallet is safer for SHIB coins at the moment? According to market data analysis, the relatively safe wallets are mainly OKXWeb3Wallet, imToken, and MetaMask wallets, which will be relatively safe. Next, the editor will talk about them in detail. Which wallet is safer for SHIB coins? At present, SHIB coins are placed on OKXWe
 Lenovo has issued a patch in May, Phoenix UEFI firmware vulnerability disclosed: affecting hundreds of Intel PC CPU models
Jun 22, 2024 am 10:27 AM
Lenovo has issued a patch in May, Phoenix UEFI firmware vulnerability disclosed: affecting hundreds of Intel PC CPU models
Jun 22, 2024 am 10:27 AM
According to news from this site on June 21, the Phoenix Secure Core UEFI firmware was exposed to a security vulnerability, affecting hundreds of Intel CPU devices. Lenovo has released a new firmware update to fix the vulnerability. This site learned from reports that the vulnerability tracking number is CVE-2024-0762, known as "UEFICANHAZBUFFEROVERFLOW", which exists in the Trusted Platform Module (TPM) configuration of Phoenix UEFI firmware. It is a buffer overflow vulnerability that can be Exploit to execute arbitrary code on a vulnerable device. The vulnerability was discovered by Eclypsium in Lenovo ThinkPad X1 Carbon 7th generation and X1Yoga 4th generation
 Hack an assassin's phone in 40 minutes
Jul 20, 2024 pm 06:11 PM
Hack an assassin's phone in 40 minutes
Jul 20, 2024 pm 06:11 PM
According to people familiar with the matter, Cellebrite, an Israeli mobile device forensics company, provided the FBI with an evaluation version of a mobile phone cracking program that has not yet been released and is still undergoing internal testing. The FBI used it to unlock the special device in less than 40 minutes. The cellphone of Trump assassin Thomas Matthew Crooks. Agents from the FBI's Pittsburgh office initially used a commercially available Cellebrite tool to unlock Crooks' phone, but were unsuccessful. So the phone was sent to the FBI's Quantico headquarters that day. After headquarters personnel contacted key account support, Cellebrite provided an unreleased unlocking tool, allowing investigators to unlock the phone at 40
 How to interact with JSON data using SQL in Golang?
Jun 03, 2024 am 11:47 AM
How to interact with JSON data using SQL in Golang?
Jun 03, 2024 am 11:47 AM
There are the following steps for interacting with JSON data through SQL in Golang: Use the json.Unmarshal function to parse JSON data into a Go structure and convert JSON to a structure. Use the database/sql package to access and operate SQL databases and perform operations such as inserts and queries. Combining the above steps, you can build an application based on SQL and JSON in Go to implement functions such as user registration and login.



