CGI安全漏洞资料速查 v1.0(转三)
cgi|安全|安全漏洞
51
类型: 攻击型
名字: search97.vts
风险等级: 中
描述: 这个文件将能使入侵者任意的读取你系统中启动httpd用户能读取的文件
建议: 将在您Web目录中的search97.vts删除或移走
解决方法: 将在您Web目录中的search97.vts删除或移走,或前往以下地址下载Patch
https://customers.verity.com/products/server/310/patches/
_____________________________________________________________________________
52
类型: 攻击型
名字: carbo.dll
风险等级: 低
描述: 如果您安装了Systems running iCat Suite version 3.0,那么它将自动在你的系统上添加一个叫carbo.dll的文件,而入侵者将能利用这个文件访问您系统上的热和文件
建议: 将在您Web目录中的openfile.cfm删除或移走
解决方法: 将在您Web目录中的openfile.cfm删除或移走
__________________________________________________________________________
53
类型: 攻击型
名字: whois_raw.cgi
风险等级: 低
描述: 因为whois_raw.cgi作者的失误,这个CGI将使入侵者能够以您系统上启动httpd的用户的权限执行您系统上任意的程序
建议: 将在您Web目录中的whois_raw.cgi删除或移走
解决方法: 将在您Web目录中的whois_raw.cgi删除或移走
_______________________________________________________________________________
54
类型: 攻击型
名字: doc
风险等级: 低
描述: 您的Web目录可以文件列表,这将帮助入侵者分析您的系统信息
建议: 将您的所有Web目录设置为不能文件列表
解决方法: 将您的所有Web目录设置为不能文件列表
_______________________________________________________________________________
55
类型: 攻击型
名字: .html/............./config.sys
风险等级: 低
描述: 如果您使用的是较久版本的ICQ,那么入侵者能够利用它阅读您机器上的所有文件
建议: 下载新版本的ICQ
解决方法: 请前往以下地址下载新版本的ICQ
http://www.icq.com/download/
______________________________________________________________________
56
类型: 攻击型
名字: ....../
风险等级: 中
描述: 您使用的WebServer软件能使入侵者阅读您系统上的所有文件
建议: 更换或升级您的WebServer软件
解决方法: 更换或升级您的WebServer软件
_________________________________________________________________________
58
类型: 攻击型
名字: no-such-file.pl
风险等级: 低
描述: 由于您的WebServer软件的缺陷,使得入侵者能够利用不存在的CGI脚本请求来分析您的站点的目录结构
建议: 升级您的WebServer软件
解决方法: 升级您的WebServer软件
________________________________________________________________________________
59
类型: 攻击型
名字: _vti_bin/shtml.dll
风险等级: 低
描述: 入侵者利用这个文件将能使您的系统的CPU占用率达到100%
建议: 将_vti_bin/shtml.dll从您的Web目录删除或移走
解决方法: 将_vti_bin/shtml.dll从您的Web目录删除或移走
______________________________________________________________________
60
类型: 信息型
名字: nph-publish
风险等级: 中
描述: 在/cgi-bin目录下存在nph-publish文件,这使入侵者能通过www浏览服务器上的任何文件
建议: 建议审查/cgi-bin目录,删除不必要的cgi程序
解决方法: 删除nph-publish文件
______________________________________________________________________
61
类型: 信息型
名字: showcode.asp
风险等级: 中
描述: 在/msadc/Samples/SELECTOR/showcode.asp?source=/msadc/Samples/SELECTOR/目录下存在showcode.asp文件可以被入侵者利用来查看服务器上的文件内容
建议: 最好禁止/msadc这个web目录的匿名访问,建议删除这个web目录
解决方法: 删除showcode.asp文件
_________________________________________________________________________
62
类型: 信息型
名字: _vti_inf.html
风险等级: 中
描述: web根目录下存在_vti_inf.html文件,该文件是Frontpage extention server的特征,包含了一系列Frontpage Extention Server的重要信息;而且Frontpage Extention server是一个有很多漏洞的web服务,用它入侵者可能直接修改首页文件
建议: 用ftp等其它方式上载网页文件
解决方法: 卸载Frontpage Extention Server
________________________________________________________________________________
63
类型: 信息型
名字: index.asp::$DATA
风险等级: 中
描述: asp程序的源代码可以被后缀+::$DATA的方法查看到,这样入侵者可以设法查到服务器数据库密码等重要信息
建议: 建议留意微软最新关于codeview的补丁和安全公告
解决方法: 安装services pack6或者打补丁:
ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/chs/security/fesrc-fix/
相关连接: ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/chs/security/fesrc-fix/
___________________________________________________________________________________
64
类型: 攻击型
名字: main.asp%81
风险等级: 低
描述: asp程序的源代码可以被后缀+%81的方法查看到,这样入侵者可以设法查到服务器数据库密码等重要信息
建议: 建议留意微软最新关于codeview的补丁和安全公告
解决方法: 安装services pack6或者打补丁:
ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/chs/security/fesrc-fix/
相关连接: ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/chs/security/fesrc-fix/
____________________________________________________________________________________
65
类型: 信息型
名字: showcode.asp_2
风险等级: 中
描述: 在/msadc/Samples/SELECTOR/目录下存在showcode.asp文件,用下面的路径:
http://www.xxx.com/msadc/Samples/SELECTOR/showcode.asp?source=/msadc/Samples/../../../../../boot.ini
可以查到boot.ini文件的内容;实际上入侵者能够利用这个ASP查看您系统上所有启动httpd用户有权限阅读的文件
建议: 禁止对/msadc目录的匿名访问
解决方法: 将在您Web目录中的showcode.asp删除或移走
请前往以下地址查询补丁
Internet Information Server:
ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/usa/Viewcode-fix/
Site Server:
ftp://ftp.microsoft.com/bussys/sitesrv/sitesrv-public/fixes/usa/siteserver3/hotfixes-postsp2/Viewcode-fix/
http://www.microsoft.com/security/products/iis/checklist.asp
相关连接: ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/usa/Viewcode-fix/
_____________________________________________________________________________________
66
类型: 攻击型
名字: ism.dll
风险等级: 高
描述: 在/scripts/iisadmin/目录下存在ism.dll文件,这个文件有一个溢出错误,允许入侵者在服务器上执行任意一段程序;另外。攻击者还随时可以令服务器的www服务死掉
建议: 禁止对/scripts目录的匿名访问
解决方法: 删除/scripts/iisadmin/ism.dll, 或者打开iis的管理控制台,选取默认web站点,点右键,选取属性,点:"主目录",在起始点那行点"配置"按钮,将".htr"的应用程序映射项删除
___________________________________________________________________________________________
67
类型: 信息型
名字: codebrws.asp_2
风险等级: 中
描述: 在/iissamples/sdk/asp/docs/下面存在codebrws.asp文件,用下面的路径:
http://www.xxx.com/iissamples/exair/howitworks/codebrws.asp?source=/index.asp就可以查看到index.asp的源码。实际上任何ascii文件都可以浏览。
建议: 删除名叫/iissamples/的web目录
解决方法: 将在您Web目录中的codebrws.asp删除或移走
请前往以下地址查询补丁
Internet Information Server:
ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/usa/Viewcode-fix/
Site Server:
ftp://ftp.microsoft.com/bussys/sitesrv/sitesrv-public/fixes/usa/siteserver3/hotfixes-postsp2/Viewcode-fix/
http://www.microsoft.com/security/products/iis/checklist.asp
相关连接: ftp://ftp.microsoft.com/bussys/iis/iis-public/fixes/usa/Viewcode-fix/
______________________________________________________________________________________
68
类型: 攻击型
名字: uploadn.asp
风险等级: 高
描述: 在/scripts/tools目录下存在uploadn.asp程序,只要入侵者有一个可用帐号,哪怕是Guest帐号,就可以上传任何文件到你的web目录,除了替换主页外,他更可以进一步控制你的整个系统!
建议: 删除名为/scripts的web目录
解决方法: 删除uploadn.asp文件
相关连接:
____________________________________________________________________________________
69
类型: 攻击型
名字: uploadx.asp
风险等级: 高
描述: 在/scripts/tools目录下存在uploadx.asp程序,只要入侵者有一个可用帐号,哪怕是Guest帐号,就可以上传任何文件到你的web目录,除了替换主页外,他更可以进一步控制你的整个系统!
建议: 删除名为/scripts的web目录
解决方法: 删除uploadx.asp文件
相关连接:
______________________________________________________________________________________
70
类型: 攻击型
名字: query.asp
风险等级: 低
描述: 在/IISSAMPLES/ExAir/Search/的目录下存在query.asp文件,这个文件有个漏洞如果被攻击者利用,后果将导致CPU使用率达到100%,机器速度将明显变慢
建议: 禁止对/iissamples目录的存取
解决方法: 删除query.asp文件
_______________________________________________________________________________
71
类型: 攻击型
名字: advsearch.asp
风险等级: 低
描述: 在/IISSAMPLES/ExAir/Search/的目录下存在query.asp文件,这个文件有个漏洞如果被攻击者利用,后果将导致CPU使用率达到100%,机器速度将明显变慢
建议: 禁止对/iissamples目录的存取
解决方法: 删除advsearch.asp文件
_______________________________________________________________________________
72
类型: 攻击型
名字: search.asp
风险等级: 低
描述: 在/IISSAMPLES/ExAir/Search/的目录下存在search.asp文件,这个文件有个漏洞如果被攻击者利用,后果将导致CPU使用率达到100%,机器速度将明显变慢
建议: 禁止对/iissamples目录的存取
解决方法: 删除search.asp文件
_________________________________________________________________________________
74
类型: 攻击型
名字: getdrvrs.exe
风险等级: 中
描述: 这个存在于/scripts/tools目录下的getdrvrs.exe文件允许任何一个用户在web根目录下创建任何文件,和创建ODBC数据源
建议: 禁止对/scripts/tools目录的匿名访问
解决方法: 删除getdrvrs.exe文件
_______________________________________________________________________________
73
类型: 攻击型
名字: newdsn.exe
风险等级: 中
描述: 这个存在于/scripts/tools目录下的newdsn.exe文件允许任何一个用户在web根目录下创建任何文件,如:
http://xxx.xxx.xxx.xxx/scripts/tools/newdsn.exe?driver=Microsoft%2BAccess%2BDriver%2B%28*.mdb%29&dsn=Evil2+samples+from+microsoft&dbq=..%2F..%2Fwwwroot%2Fevil2.htm&newdb=CREATE_DB&attr=
建议: 禁止对/scripts/tools目录的匿名访问
解决方法: 删除newdsn.exe文件
_______________________________________________________________________________
75
类型: 信息型
名字: showcode.asp_3
风险等级: 中
描述: 在/iissamples/exair/howitworks/存在code.asp文件,入侵者利用该文件可以查看服务器硬盘上任何一个ASCII文件的内容,并显示asp程序文件的源代码
建议: 禁止对/iissamples的web目录的匿名访问
解决方法: 删除showcode.asp文件

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Easily remove borders in Microsoft Edge in three simplified steps
Sep 02, 2023 pm 02:57 PM
Easily remove borders in Microsoft Edge in three simplified steps
Sep 02, 2023 pm 02:57 PM
Many users are dissatisfied with the white border around web pages in Microsoft Edge. They think it's unnecessary and distracting, and they're asking Microsoft to remove Microsoft Edge's bezels entirely. This is similar to the saying "don't fix what's not broken", but Microsoft doesn't seem to have taken this into account. Of course, it's a popular web browser that offers a variety of features, including a built-in ad blocker, tracking prevention, and a password manager. However, some users may find that the browser has a border around web pages. This border can be distracting or unsightly, and there are several ways to remove it. In a lengthy conversation on r/Edge, some regular non-internal users discovered,
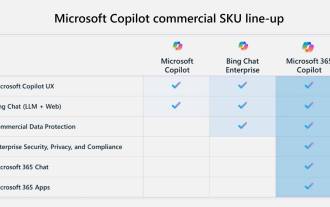 Key differences between Microsoft 365 Copilot, Bing Chat Enterprise, and Copilot in Windows
Sep 23, 2023 pm 03:57 PM
Key differences between Microsoft 365 Copilot, Bing Chat Enterprise, and Copilot in Windows
Sep 23, 2023 pm 03:57 PM
Currently, Microsoft offers three different AI assistants to enterprise customers: Microsoft365Copilot, BingChatEnterprise, and Copilot in Windows. We would like to explain the differences between these three options. CopilotinWindows: Copilot in Windows is a powerful tool that helps you complete tasks faster and easier. You can seamlessly access Copilot from the taskbar or by pressing Win+C, and it will provide help next to any application you use. Copilot in Windows features new icons, new user experience and BingChat. it will be 2
 How to log in to a Microsoft account on Windows 10
Jan 01, 2024 pm 05:58 PM
How to log in to a Microsoft account on Windows 10
Jan 01, 2024 pm 05:58 PM
You can log in with a Microsoft account in the win10 system, but there are still many friends who don’t know how to log in. Today I will bring you the method of logging in with a win10 Microsoft account. Come and take a look. How to log in to win10 microsoft account: 1. Click Start in the lower left corner and click the gear to open settings. 2. Then find "Account" and click to open. 3. After entering the account, click "Email and App Accounts" on the left. 4. Then click "Add Account" on the right. 5. After entering the account interface, many options will appear. Click the first "outlook". 6. Enter your account number in the Microsoft account window that appears. 7. After all is completed, you can
 Fix 'Your account is currently unavailable' error in OneDrive
Sep 13, 2023 am 08:33 AM
Fix 'Your account is currently unavailable' error in OneDrive
Sep 13, 2023 am 08:33 AM
Trying to log in in Windows doesn't work either. However, a check on the Microsoft account showed that there were no issues with it. I am able to log in and out of my Microsoft account on Windows and the web and am able to access all services. Only OneDrive appears to be affected. Microsoft's error message, like most of the time, isn't very helpful because it's too generic to be of much use. It starts with the following statement: "Your OneDrive or profile may be temporarily blocked because it is experiencing an unusually large amount of traffic. In this case, the block will be removed after 24 hours" This is followed by another sentence, Other possible reasons for temporary account suspension are listed: "
 What are web standards?
Oct 18, 2023 pm 05:24 PM
What are web standards?
Oct 18, 2023 pm 05:24 PM
Web standards are a set of specifications and guidelines developed by W3C and other related organizations. It includes standardization of HTML, CSS, JavaScript, DOM, Web accessibility and performance optimization. By following these standards, the compatibility of pages can be improved. , accessibility, maintainability and performance. The goal of web standards is to enable web content to be displayed and interacted consistently on different platforms, browsers and devices, providing better user experience and development efficiency.
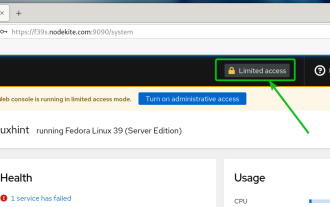 How to enable administrative access from the cockpit web UI
Mar 20, 2024 pm 06:56 PM
How to enable administrative access from the cockpit web UI
Mar 20, 2024 pm 06:56 PM
Cockpit is a web-based graphical interface for Linux servers. It is mainly intended to make managing Linux servers easier for new/expert users. In this article, we will discuss Cockpit access modes and how to switch administrative access to Cockpit from CockpitWebUI. Content Topics: Cockpit Entry Modes Finding the Current Cockpit Access Mode Enable Administrative Access for Cockpit from CockpitWebUI Disabling Administrative Access for Cockpit from CockpitWebUI Conclusion Cockpit Entry Modes The cockpit has two access modes: Restricted Access: This is the default for the cockpit access mode. In this access mode you cannot access the web user from the cockpit
 Windows 12 will be a free upgrade, no subscription required
Oct 21, 2023 am 11:17 AM
Windows 12 will be a free upgrade, no subscription required
Oct 21, 2023 am 11:17 AM
Microsoft doesn't work with subscription-based versions of Windows 12, and you won't be charged any fees. People are still talking about Windows 12 being subscription-based, a rumor based on a string of code in a Windows 11 preview build. Some people are still wondering how Microsoft plans to make their next version of Windows a subscription model. It turns out that the rumor discussed by some media outlets was an "IoT Enterprise Subscription" based on Windows 11, not Windows vNext. For those who don’t know, Windows24H2 or WindowsvNext is the public name for Windows 12. Some media will win
 what does web mean
Jan 09, 2024 pm 04:50 PM
what does web mean
Jan 09, 2024 pm 04:50 PM
The web is a global wide area network, also known as the World Wide Web, which is an application form of the Internet. The Web is an information system based on hypertext and hypermedia, which allows users to browse and obtain information by jumping between different web pages through hyperlinks. The basis of the Web is the Internet, which uses unified and standardized protocols and languages to enable data exchange and information sharing between different computers.






