关于拦截器的功用
关于拦截器的作用
class Computer {
private $_name;
private $_model;
private $_cpu;
private function __set($_key,$_value) {
$this->$_key = $_value;
}
private function __get($_key) {
return $this->$_key;
}
}
$computer = new Computer();
$computer->_name = '联想';
$computer->_cpu = '四核';
$computer->_model = 'i7';
echo $computer->_name;
echo $computer->_cpu;
echo $computer->_model;
我想问的事如果使用了_set和_get方法,那么类的私有属性就可以在外面任意使用赋值修改,那么和把属性设置为Public有何区别了,感觉上这两个方法没有什么用了。
------解决方案--------------------
是的,对于你的用法,的确是画蛇添足
------解决方案--------------------
set不是你那样用的,你去看哈其他开源框架就清楚了,特别是些开源框架的数据库Active Record类
------解决方案--------------------
面向对象就是要隐藏数据,开放接口。
你遵不遵循是你的事,程序只会听你的话,语法就这么回事。

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 What are the differences between Huawei GT3 Pro and GT4?
Dec 29, 2023 pm 02:27 PM
What are the differences between Huawei GT3 Pro and GT4?
Dec 29, 2023 pm 02:27 PM
Many users will choose the Huawei brand when choosing smart watches. Among them, Huawei GT3pro and GT4 are very popular choices. Many users are curious about the difference between Huawei GT3pro and GT4. Let’s introduce the two to you. . What are the differences between Huawei GT3pro and GT4? 1. Appearance GT4: 46mm and 41mm, the material is glass mirror + stainless steel body + high-resolution fiber back shell. GT3pro: 46.6mm and 42.9mm, the material is sapphire glass + titanium body/ceramic body + ceramic back shell 2. Healthy GT4: Using the latest Huawei Truseen5.5+ algorithm, the results will be more accurate. GT3pro: Added ECG electrocardiogram and blood vessel and safety
 What does the identity attribute in SQL mean?
Feb 19, 2024 am 11:24 AM
What does the identity attribute in SQL mean?
Feb 19, 2024 am 11:24 AM
What is Identity in SQL? Specific code examples are needed. In SQL, Identity is a special data type used to generate auto-incrementing numbers. It is often used to uniquely identify each row of data in a table. The Identity column is often used in conjunction with the primary key column to ensure that each record has a unique identifier. This article will detail how to use Identity and some practical code examples. The basic way to use Identity is to use Identit when creating a table.
 How SpringBoot monitors redis Key change events
May 26, 2023 pm 01:55 PM
How SpringBoot monitors redis Key change events
May 26, 2023 pm 01:55 PM
1. Function Overview Keyspace notification allows clients to receive events that modify Rediskey changes in some way by subscribing to channels or patterns. All commands that modify key keys. All keys that received the LPUSHkeyvalue[value…] command. All expired keys in the db database. Events are distributed through Redis's subscription and publishing functions (pub/sub), so all clients that support subscription and publishing functions can directly use the keyspace notification function without any modifications. Because the current subscription and publishing functions of Redis adopt a fireandforget strategy, if your program
 Fix: Snipping tool not working in Windows 11
Aug 24, 2023 am 09:48 AM
Fix: Snipping tool not working in Windows 11
Aug 24, 2023 am 09:48 AM
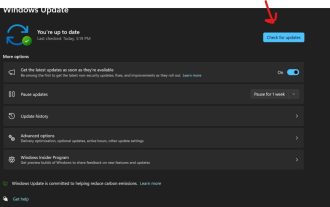
Why Snipping Tool Not Working on Windows 11 Understanding the root cause of the problem can help find the right solution. Here are the top reasons why the Snipping Tool might not be working properly: Focus Assistant is On: This prevents the Snipping Tool from opening. Corrupted application: If the snipping tool crashes on launch, it might be corrupted. Outdated graphics drivers: Incompatible drivers may interfere with the snipping tool. Interference from other applications: Other running applications may conflict with the Snipping Tool. Certificate has expired: An error during the upgrade process may cause this issu simple solution. These are suitable for most users and do not require any special technical knowledge. 1. Update Windows and Microsoft Store apps
 How to solve the problem of batch deletion of key values in redis
May 31, 2023 am 08:59 AM
How to solve the problem of batch deletion of key values in redis
May 31, 2023 am 08:59 AM
Problems encountered: During the development process, you will encounter keys that need to be deleted in batches according to certain rules, such as login_logID (ID is a variable). Now you need to delete data such as "login_log*", but redis itself only has batch query. Command keys for class key values, but there is no command for batch deletion of a certain class. Solution: Query first, then delete, use xargs to pass parameters (xargs can convert pipe or standard input (stdin) data into command line parameters), execute the query statement first, and then remove the queried key value and the original del parameters. delete. redis-cliKEYSkey* (search condition)|xargsr
 Unpatchable Yubico two-factor authentication key vulnerability breaks the security of most Yubikey 5, Security Key, and YubiHSM 2FA devices
Sep 04, 2024 pm 06:32 PM
Unpatchable Yubico two-factor authentication key vulnerability breaks the security of most Yubikey 5, Security Key, and YubiHSM 2FA devices
Sep 04, 2024 pm 06:32 PM
An unpatchable Yubico two-factor authentication key vulnerability has broken the security of most Yubikey 5, Security Key, and YubiHSM 2FA devices. The Feitian A22 JavaCard and other devices using Infineon SLB96xx series TPMs are also vulnerable.All
 What does private mean in java
Nov 24, 2022 pm 06:27 PM
What does private mean in java
Nov 24, 2022 pm 06:27 PM
In Java, private means "private" and is an access control modifier used to modify classes, properties and methods. Class members modified with private can only be accessed and modified by the methods of the class itself, and cannot be accessed and referenced by any other class (including subclasses of the class); therefore, the private modifier has the highest level of protection.
 Trezor Cold Wallet: Model One and Model T Features and Usage Guide
Jan 19, 2024 pm 04:12 PM
Trezor Cold Wallet: Model One and Model T Features and Usage Guide
Jan 19, 2024 pm 04:12 PM
After problems occurred in many centralized exchanges, more and more cryptocurrency investors began to transfer assets to cold wallets to reduce the risks posed by centralized exchanges. This article will introduce Trezor, the world's earliest cold wallet provider. Since the first cold wallet was launched in 2014, it has been sold in many countries around the world. Trezor's products include Model One launched in 2014 and the advanced version Model T launched in 2018. The following will continue to introduce the differences between these two products and other cold wallets. What is Trezor cold wallet? In 2014, Trezor launched the first cold wallet ModelOne. In addition to common BTC, ETH, USDT and other currencies, the wallet also supports more than 1,000 other currencies.






