How to Implement Robust Global Mutex Patterns in C#?

The Mutex class in C#provides a mechanism to control access to multiple threads or processes sharing resources. The global mutual mutual body has a systematic scope, and has proposed unique challenges in ensuring safe and reliable use. This article discusses a comprehensive model of creating and effective use of global mutual expeckets, and solves the key aspects of regional setting independence, correct mutual dismissal release, and processing abnormal conditions.
Mode implementation
The following code example shows the reliable mode of using the global mutual body:
Key features
using System.Runtime.InteropServices; //GuidAttribute
using System.Reflection; //Assembly
using System.Threading; //Mutex
using System.Security.AccessControl; //MutexAccessRule
using System.Security.Principal; //SecurityIdentifier
// ...
// 主应用程序逻辑
static void Main(string[] args)
{
// 获取应用程序的唯一GUID
string appGuid =
((GuidAttribute)Assembly.GetExecutingAssembly()
.GetCustomAttributes(typeof(GuidAttribute), false)
.GetValue(0)).Value.ToString();
// 创建全局唯一的互斥体ID
string mutexId = string.Format( "Global\{{{0}}}", appGuid );
// 为多用户使用建立安全设置
var allowEveryoneRule =
new MutexAccessRule( new SecurityIdentifier( WellKnownSidType.WorldSid
, null)
, MutexRights.FullControl
, AccessControlType.Allow
);
var securitySettings = new MutexSecurity();
securitySettings.AddAccessRule(allowEveryoneRule);
// 使用指定的ID和安全设置初始化互斥体
using (var mutex = new Mutex(false, mutexId, out bool createdNew, securitySettings))
{
// 尝试获取互斥体句柄,设置超时
var hasMutexHandle = false;
try
{
hasMutexHandle = mutex.WaitOne(5000, false);
}
catch (AbandonedMutexException)
{
// 记录日志并获取被放弃的互斥体
hasMutexHandle = true;
}
// 在互斥体范围内执行关键操作
if (hasMutexHandle)
{
// ...
mutex.ReleaseMutex();
}
}
}Independence of regional settings: The mutualized ID uses the GUID generation of the application to ensure that it is unique in different areas.
- 保证互斥体释放: using块在超出范围时自动释放互斥体,消除了悬空互斥体的风险。 Out time processing:
- Specify the optional overtime when obtaining the mutually exclusive body to prevent unlimited waiting. The abandoned mutually exclusive treatment: Elegant to obtain the abandoned mutual body to ensure that the program execution will not be blocked indefinitely.
- Multi -user security: Mutual exclusion to grant explicit access permissions to all users, allowing collaboration and resource sharing.
- Conclusion
- 此模式为在C#中使用全局互斥体提供了坚实的基础,确保安全可靠的执行。 By following these criteria, developers can effectively manage sharing resources and prevent potential issues related to the use of mutual alternatives.
The above is the detailed content of How to Implement Robust Global Mutex Patterns in C#?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 C language data structure: data representation and operation of trees and graphs
Apr 04, 2025 am 11:18 AM
C language data structure: data representation and operation of trees and graphs
Apr 04, 2025 am 11:18 AM
C language data structure: The data representation of the tree and graph is a hierarchical data structure consisting of nodes. Each node contains a data element and a pointer to its child nodes. The binary tree is a special type of tree. Each node has at most two child nodes. The data represents structTreeNode{intdata;structTreeNode*left;structTreeNode*right;}; Operation creates a tree traversal tree (predecision, in-order, and later order) search tree insertion node deletes node graph is a collection of data structures, where elements are vertices, and they can be connected together through edges with right or unrighted data representing neighbors.
 The truth behind the C language file operation problem
Apr 04, 2025 am 11:24 AM
The truth behind the C language file operation problem
Apr 04, 2025 am 11:24 AM
The truth about file operation problems: file opening failed: insufficient permissions, wrong paths, and file occupied. Data writing failed: the buffer is full, the file is not writable, and the disk space is insufficient. Other FAQs: slow file traversal, incorrect text file encoding, and binary file reading errors.
 What are the basic requirements for c language functions
Apr 03, 2025 pm 10:06 PM
What are the basic requirements for c language functions
Apr 03, 2025 pm 10:06 PM
C language functions are the basis for code modularization and program building. They consist of declarations (function headers) and definitions (function bodies). C language uses values to pass parameters by default, but external variables can also be modified using address pass. Functions can have or have no return value, and the return value type must be consistent with the declaration. Function naming should be clear and easy to understand, using camel or underscore nomenclature. Follow the single responsibility principle and keep the function simplicity to improve maintainability and readability.
 Function name definition in c language
Apr 03, 2025 pm 10:03 PM
Function name definition in c language
Apr 03, 2025 pm 10:03 PM
The C language function name definition includes: return value type, function name, parameter list and function body. Function names should be clear, concise and unified in style to avoid conflicts with keywords. Function names have scopes and can be used after declaration. Function pointers allow functions to be passed or assigned as arguments. Common errors include naming conflicts, mismatch of parameter types, and undeclared functions. Performance optimization focuses on function design and implementation, while clear and easy-to-read code is crucial.
 How to calculate c-subscript 3 subscript 5 c-subscript 3 subscript 5 algorithm tutorial
Apr 03, 2025 pm 10:33 PM
How to calculate c-subscript 3 subscript 5 c-subscript 3 subscript 5 algorithm tutorial
Apr 03, 2025 pm 10:33 PM
The calculation of C35 is essentially combinatorial mathematics, representing the number of combinations selected from 3 of 5 elements. The calculation formula is C53 = 5! / (3! * 2!), which can be directly calculated by loops to improve efficiency and avoid overflow. In addition, understanding the nature of combinations and mastering efficient calculation methods is crucial to solving many problems in the fields of probability statistics, cryptography, algorithm design, etc.
 Concept of c language function
Apr 03, 2025 pm 10:09 PM
Concept of c language function
Apr 03, 2025 pm 10:09 PM
C language functions are reusable code blocks. They receive input, perform operations, and return results, which modularly improves reusability and reduces complexity. The internal mechanism of the function includes parameter passing, function execution, and return values. The entire process involves optimization such as function inline. A good function is written following the principle of single responsibility, small number of parameters, naming specifications, and error handling. Pointers combined with functions can achieve more powerful functions, such as modifying external variable values. Function pointers pass functions as parameters or store addresses, and are used to implement dynamic calls to functions. Understanding function features and techniques is the key to writing efficient, maintainable, and easy to understand C programs.
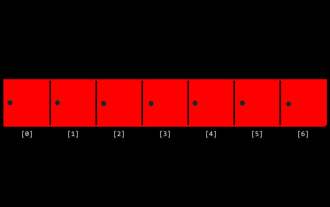 CS-Week 3
Apr 04, 2025 am 06:06 AM
CS-Week 3
Apr 04, 2025 am 06:06 AM
Algorithms are the set of instructions to solve problems, and their execution speed and memory usage vary. In programming, many algorithms are based on data search and sorting. This article will introduce several data retrieval and sorting algorithms. Linear search assumes that there is an array [20,500,10,5,100,1,50] and needs to find the number 50. The linear search algorithm checks each element in the array one by one until the target value is found or the complete array is traversed. The algorithm flowchart is as follows: The pseudo-code for linear search is as follows: Check each element: If the target value is found: Return true Return false C language implementation: #include#includeintmain(void){i
 C language multithreaded programming: a beginner's guide and troubleshooting
Apr 04, 2025 am 10:15 AM
C language multithreaded programming: a beginner's guide and troubleshooting
Apr 04, 2025 am 10:15 AM
C language multithreading programming guide: Creating threads: Use the pthread_create() function to specify thread ID, properties, and thread functions. Thread synchronization: Prevent data competition through mutexes, semaphores, and conditional variables. Practical case: Use multi-threading to calculate the Fibonacci number, assign tasks to multiple threads and synchronize the results. Troubleshooting: Solve problems such as program crashes, thread stop responses, and performance bottlenecks.






