 Backend Development
Backend Development
 C++
C++
 Can We Enhance the Reusability of Key-Oriented Access Protection in C ?
Can We Enhance the Reusability of Key-Oriented Access Protection in C ?
Can We Enhance the Reusability of Key-Oriented Access Protection in C ?

Can we improve the reusability of the key-oriented access protection pattern?
The provided pattern utilizes friend classes to control access to methods, granting access to only those who possess specific keys. While effective, this approach can become cumbersome due to the repetition of friend declarations and the need to specify passkeys within the method's parameter list.
Solution in C 03:
In C 03, a macro-based approach can enhance usability by reducing the number of friend declarations and allowing the creation of passkeys outside the method's definition. Macros are used to define passkeys that can be easily generated for different friend classes, simplifying the code and making it easier to maintain. This solution, however, comes with limitations such as the requirement to know specific passkey names and the presence of a block of passkey definitions, which can be perceived as ungainly.
Solution in C 0x:
C 0x introduces significant enhancements that enable a cleaner and more expressive implementation of the pattern.
- Variadic templates: Passkeys are templated on their parameter types, allowing for key types to be specified as variadic template parameters. This eliminates the need for macros when defining functions that require passkeys.
- Template parameters as friends: Templates can now be befriended, which enables the direct specification of passkeys as template parameters within the methods they protect. This eliminates the need to declare passkeys separately and simplifies the process of creating and using them.
The implementation in C 0x involves defining a passkey template that represents unique passkeys for each class and a allow template that checks if a passkey is allowed for a particular function, based on the template parameters of that function. This approach offers significant benefits:
- Passkeys are specific to each class: Each class possesses its unique passkey, which can be used to grant or restrict access.
- Simplified function access: Functions are befriended using the allow template, which ensures that only those who possess the required passkeys can invoke the function.
- Generic and reusable: This solution is generic and can be applied to any combination of classes and functions without requiring special definitions, making it highly reusable and easy to incorporate into existing codebases.
The above is the detailed content of Can We Enhance the Reusability of Key-Oriented Access Protection in C ?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 C language data structure: data representation and operation of trees and graphs
Apr 04, 2025 am 11:18 AM
C language data structure: data representation and operation of trees and graphs
Apr 04, 2025 am 11:18 AM
C language data structure: The data representation of the tree and graph is a hierarchical data structure consisting of nodes. Each node contains a data element and a pointer to its child nodes. The binary tree is a special type of tree. Each node has at most two child nodes. The data represents structTreeNode{intdata;structTreeNode*left;structTreeNode*right;}; Operation creates a tree traversal tree (predecision, in-order, and later order) search tree insertion node deletes node graph is a collection of data structures, where elements are vertices, and they can be connected together through edges with right or unrighted data representing neighbors.
 The truth behind the C language file operation problem
Apr 04, 2025 am 11:24 AM
The truth behind the C language file operation problem
Apr 04, 2025 am 11:24 AM
The truth about file operation problems: file opening failed: insufficient permissions, wrong paths, and file occupied. Data writing failed: the buffer is full, the file is not writable, and the disk space is insufficient. Other FAQs: slow file traversal, incorrect text file encoding, and binary file reading errors.
 What are the basic requirements for c language functions
Apr 03, 2025 pm 10:06 PM
What are the basic requirements for c language functions
Apr 03, 2025 pm 10:06 PM
C language functions are the basis for code modularization and program building. They consist of declarations (function headers) and definitions (function bodies). C language uses values to pass parameters by default, but external variables can also be modified using address pass. Functions can have or have no return value, and the return value type must be consistent with the declaration. Function naming should be clear and easy to understand, using camel or underscore nomenclature. Follow the single responsibility principle and keep the function simplicity to improve maintainability and readability.
 Function name definition in c language
Apr 03, 2025 pm 10:03 PM
Function name definition in c language
Apr 03, 2025 pm 10:03 PM
The C language function name definition includes: return value type, function name, parameter list and function body. Function names should be clear, concise and unified in style to avoid conflicts with keywords. Function names have scopes and can be used after declaration. Function pointers allow functions to be passed or assigned as arguments. Common errors include naming conflicts, mismatch of parameter types, and undeclared functions. Performance optimization focuses on function design and implementation, while clear and easy-to-read code is crucial.
 Concept of c language function
Apr 03, 2025 pm 10:09 PM
Concept of c language function
Apr 03, 2025 pm 10:09 PM
C language functions are reusable code blocks. They receive input, perform operations, and return results, which modularly improves reusability and reduces complexity. The internal mechanism of the function includes parameter passing, function execution, and return values. The entire process involves optimization such as function inline. A good function is written following the principle of single responsibility, small number of parameters, naming specifications, and error handling. Pointers combined with functions can achieve more powerful functions, such as modifying external variable values. Function pointers pass functions as parameters or store addresses, and are used to implement dynamic calls to functions. Understanding function features and techniques is the key to writing efficient, maintainable, and easy to understand C programs.
 How to calculate c-subscript 3 subscript 5 c-subscript 3 subscript 5 algorithm tutorial
Apr 03, 2025 pm 10:33 PM
How to calculate c-subscript 3 subscript 5 c-subscript 3 subscript 5 algorithm tutorial
Apr 03, 2025 pm 10:33 PM
The calculation of C35 is essentially combinatorial mathematics, representing the number of combinations selected from 3 of 5 elements. The calculation formula is C53 = 5! / (3! * 2!), which can be directly calculated by loops to improve efficiency and avoid overflow. In addition, understanding the nature of combinations and mastering efficient calculation methods is crucial to solving many problems in the fields of probability statistics, cryptography, algorithm design, etc.
 CS-Week 3
Apr 04, 2025 am 06:06 AM
CS-Week 3
Apr 04, 2025 am 06:06 AM
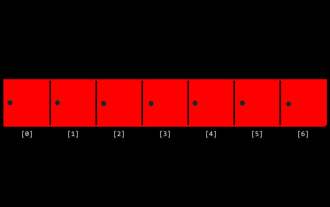
Algorithms are the set of instructions to solve problems, and their execution speed and memory usage vary. In programming, many algorithms are based on data search and sorting. This article will introduce several data retrieval and sorting algorithms. Linear search assumes that there is an array [20,500,10,5,100,1,50] and needs to find the number 50. The linear search algorithm checks each element in the array one by one until the target value is found or the complete array is traversed. The algorithm flowchart is as follows: The pseudo-code for linear search is as follows: Check each element: If the target value is found: Return true Return false C language implementation: #include#includeintmain(void){i
 C# vs. C : History, Evolution, and Future Prospects
Apr 19, 2025 am 12:07 AM
C# vs. C : History, Evolution, and Future Prospects
Apr 19, 2025 am 12:07 AM
The history and evolution of C# and C are unique, and the future prospects are also different. 1.C was invented by BjarneStroustrup in 1983 to introduce object-oriented programming into the C language. Its evolution process includes multiple standardizations, such as C 11 introducing auto keywords and lambda expressions, C 20 introducing concepts and coroutines, and will focus on performance and system-level programming in the future. 2.C# was released by Microsoft in 2000. Combining the advantages of C and Java, its evolution focuses on simplicity and productivity. For example, C#2.0 introduced generics and C#5.0 introduced asynchronous programming, which will focus on developers' productivity and cloud computing in the future.





