What are the five most commonly used algorithms?
Commonly used algorithms are: 1. Divide and conquer method; 2. Greedy algorithm, a simpler and faster design technology for certain optimal solution problems; 3. Dynamic programming algorithm; 4. Backtracking method, a kind of optimal search method; 5. Branch and bound method.
#The five most commonly used algorithms are: divide and conquer method, greedy algorithm, dynamic programming algorithm, backtracking method, and branch and bound method.
What is an algorithm?
Algorithm refers to an accurate and complete description of a problem-solving solution. It is a series of clear instructions for solving problems. Algorithm represents a systematic method to describe the strategic mechanism for solving problems.
It can be understood that an algorithm is a series of steps used to solve a specific problem; the algorithm must have the following three important characteristics:
1. Finiteness. After executing a finite number of steps, the algorithm must terminate.
2. Accuracy. Each step of the algorithm must be exactly defined.
3. Feasibility. A specific algorithm must be able to solve a specific problem in a specific amount of time.
The five most commonly used algorithms
divide and conquer method
The divide and conquer method is to A complex problem is divided into two or more identical or similar sub-problems, and then the sub-problems are divided into smaller sub-problems... until finally the sub-problems can be solved simply and directly, and the solution to the original problem is the merger of the solutions to the sub-problems. .
Problems that can be solved by the divide-and-conquer method generally have the following characteristics:
1). The problem can be easily solved when the scale of the problem is reduced to a certain extent;
2). This problem can be decomposed into several smaller identical problems, that is, the problem has optimal substructure properties;
3). The solutions to the sub-problems decomposed using this problem can be combined into The solution to this problem;
4), each sub-problem decomposed by this problem is independent of each other, that is, there are no common sub-sub-problems between the sub-problems.
Greedy algorithm
The greedy algorithm is a simpler and faster design technology for certain optimal solution problems.
The greedy method design algorithm is characterized by proceeding step by step. It often makes the optimal choice based on the current situation and based on an optimization measure, without considering various possible overall situations. It eliminates the need to find The optimal solution must exhaust a lot of time to exhaust all possibilities. It uses top-down and iterative methods to make successive greedy choices. Each time a greedy choice is made, the desired problem is simplified into a smaller sub-set. Problem, through greedy selection at each step, an optimal solution to the problem can be obtained. Although it is guaranteed to obtain a local optimal solution at each step, the resulting global solution is sometimes not necessarily optimal, so the greedy algorithm does not Backtrace.
Dynamic programming algorithm
Dynamic programming is a method used in mathematics and computer science to solve optimization problems that contain overlapping subproblems. The basic idea is to decompose the original problem into similar sub-problems, and in the process of solving the problem, the solution to the original problem is obtained through the solutions of the sub-problems. The idea of dynamic programming is the basis of many algorithms and is widely used in the fields of computer science and engineering.
Dynamic programming methods are usually used to solve optimization problems. This type of problem can have many feasible solutions. Each solution has a value. Finding the solution with the optimal value is called an optimal solution to the problem. Instead of the optimal solution, there may be multiple solutions that all reach the optimal value.
Steps to design a dynamic programming algorithm:
1), characterize the structural characteristics of an optimal solution
2), recursively define the value of the optimal solution
3), calculate the value of the optimal solution, usually using the bottom-up method
4), use the calculated information to construct an optimal solution
Dynamic programming and divide and conquer method Similar to the solution of the original problem, the solution of the sub-problem is combined to solve the solution of the original problem. The difference from the divide-and-conquer method is that the sub-problems of the divide-and-conquer method exist independently of each other, while dynamic programming is applied when the sub-problems overlap.
Backtracking method
The backtracking method (exploration and backtracking method) is a optimization search method that searches forward according to the optimization conditions to achieve the goal. But when you reach a certain step in exploration and find that the original choice is not optimal or cannot achieve the goal, you will take a step back and make another choice. This technique of going back and trying again when it doesn't work is the backtracking method, and the point in a certain state that satisfies the backtracking conditions Called the "backtrack point".
The basic idea is that in the solution space tree containing all solutions to the problem, according to the depth-first search strategy, the solution space tree is deeply explored starting from the root node. When a node is explored, it is necessary to first determine whether the node contains the solution to the problem. If it does, continue exploring from this node. If the node does not contain the solution to the problem, proceed layer by layer to its ancestors. Node backtracking.
Branch and Bound Method
The branch and bound method is a very widely used algorithm. The use of this algorithm is very skillful, and different types of problem solutions have different methods. Are not the same.
The basic idea of the branch-and-bound method is to search the space of all feasible solutions (a limited number) to the optimization problem with constraints. When the algorithm is specifically executed, the entire feasible solution space is continuously divided into smaller and smaller subsets (called branches), and a lower or upper bound (called delimitation) is calculated for the value of the solution in each subset. ). After each branch, no further branches will be made to those subsets whose limits exceed the known feasible solution value. In this way, many subsets of the solution (that is, many nodes on the search tree) can be ignored, thus narrowing the search scope. This process continues until a feasible solution is found whose value is no larger than the bounds of any subset. Therefore, this algorithm can generally obtain the optimal solution.
The above is the detailed content of What are the five most commonly used algorithms?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1670
1670
 14
14
 1428
1428
 52
52
 1329
1329
 25
25
 1274
1274
 29
29
 1256
1256
 24
24
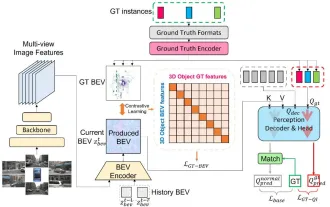 CLIP-BEVFormer: Explicitly supervise the BEVFormer structure to improve long-tail detection performance
Mar 26, 2024 pm 12:41 PM
CLIP-BEVFormer: Explicitly supervise the BEVFormer structure to improve long-tail detection performance
Mar 26, 2024 pm 12:41 PM
Written above & the author’s personal understanding: At present, in the entire autonomous driving system, the perception module plays a vital role. The autonomous vehicle driving on the road can only obtain accurate perception results through the perception module. The downstream regulation and control module in the autonomous driving system makes timely and correct judgments and behavioral decisions. Currently, cars with autonomous driving functions are usually equipped with a variety of data information sensors including surround-view camera sensors, lidar sensors, and millimeter-wave radar sensors to collect information in different modalities to achieve accurate perception tasks. The BEV perception algorithm based on pure vision is favored by the industry because of its low hardware cost and easy deployment, and its output results can be easily applied to various downstream tasks.
 Implementing Machine Learning Algorithms in C++: Common Challenges and Solutions
Jun 03, 2024 pm 01:25 PM
Implementing Machine Learning Algorithms in C++: Common Challenges and Solutions
Jun 03, 2024 pm 01:25 PM
Common challenges faced by machine learning algorithms in C++ include memory management, multi-threading, performance optimization, and maintainability. Solutions include using smart pointers, modern threading libraries, SIMD instructions and third-party libraries, as well as following coding style guidelines and using automation tools. Practical cases show how to use the Eigen library to implement linear regression algorithms, effectively manage memory and use high-performance matrix operations.
 Explore the underlying principles and algorithm selection of the C++sort function
Apr 02, 2024 pm 05:36 PM
Explore the underlying principles and algorithm selection of the C++sort function
Apr 02, 2024 pm 05:36 PM
The bottom layer of the C++sort function uses merge sort, its complexity is O(nlogn), and provides different sorting algorithm choices, including quick sort, heap sort and stable sort.
 Can artificial intelligence predict crime? Explore CrimeGPT's capabilities
Mar 22, 2024 pm 10:10 PM
Can artificial intelligence predict crime? Explore CrimeGPT's capabilities
Mar 22, 2024 pm 10:10 PM
The convergence of artificial intelligence (AI) and law enforcement opens up new possibilities for crime prevention and detection. The predictive capabilities of artificial intelligence are widely used in systems such as CrimeGPT (Crime Prediction Technology) to predict criminal activities. This article explores the potential of artificial intelligence in crime prediction, its current applications, the challenges it faces, and the possible ethical implications of the technology. Artificial Intelligence and Crime Prediction: The Basics CrimeGPT uses machine learning algorithms to analyze large data sets, identifying patterns that can predict where and when crimes are likely to occur. These data sets include historical crime statistics, demographic information, economic indicators, weather patterns, and more. By identifying trends that human analysts might miss, artificial intelligence can empower law enforcement agencies
 Improved detection algorithm: for target detection in high-resolution optical remote sensing images
Jun 06, 2024 pm 12:33 PM
Improved detection algorithm: for target detection in high-resolution optical remote sensing images
Jun 06, 2024 pm 12:33 PM
01 Outlook Summary Currently, it is difficult to achieve an appropriate balance between detection efficiency and detection results. We have developed an enhanced YOLOv5 algorithm for target detection in high-resolution optical remote sensing images, using multi-layer feature pyramids, multi-detection head strategies and hybrid attention modules to improve the effect of the target detection network in optical remote sensing images. According to the SIMD data set, the mAP of the new algorithm is 2.2% better than YOLOv5 and 8.48% better than YOLOX, achieving a better balance between detection results and speed. 02 Background & Motivation With the rapid development of remote sensing technology, high-resolution optical remote sensing images have been used to describe many objects on the earth’s surface, including aircraft, cars, buildings, etc. Object detection in the interpretation of remote sensing images
 Practice and reflections on Jiuzhang Yunji DataCanvas multi-modal large model platform
Oct 20, 2023 am 08:45 AM
Practice and reflections on Jiuzhang Yunji DataCanvas multi-modal large model platform
Oct 20, 2023 am 08:45 AM
1. The historical development of multi-modal large models. The photo above is the first artificial intelligence workshop held at Dartmouth College in the United States in 1956. This conference is also considered to have kicked off the development of artificial intelligence. Participants Mainly the pioneers of symbolic logic (except for the neurobiologist Peter Milner in the middle of the front row). However, this symbolic logic theory could not be realized for a long time, and even ushered in the first AI winter in the 1980s and 1990s. It was not until the recent implementation of large language models that we discovered that neural networks really carry this logical thinking. The work of neurobiologist Peter Milner inspired the subsequent development of artificial neural networks, and it was for this reason that he was invited to participate in this project.
 Application of algorithms in the construction of 58 portrait platform
May 09, 2024 am 09:01 AM
Application of algorithms in the construction of 58 portrait platform
May 09, 2024 am 09:01 AM
1. Background of the Construction of 58 Portraits Platform First of all, I would like to share with you the background of the construction of the 58 Portrait Platform. 1. The traditional thinking of the traditional profiling platform is no longer enough. Building a user profiling platform relies on data warehouse modeling capabilities to integrate data from multiple business lines to build accurate user portraits; it also requires data mining to understand user behavior, interests and needs, and provide algorithms. side capabilities; finally, it also needs to have data platform capabilities to efficiently store, query and share user profile data and provide profile services. The main difference between a self-built business profiling platform and a middle-office profiling platform is that the self-built profiling platform serves a single business line and can be customized on demand; the mid-office platform serves multiple business lines, has complex modeling, and provides more general capabilities. 2.58 User portraits of the background of Zhongtai portrait construction
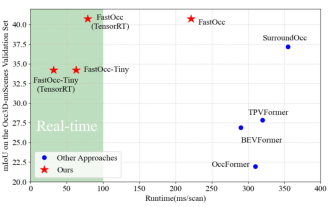 Add SOTA in real time and skyrocket! FastOcc: Faster inference and deployment-friendly Occ algorithm is here!
Mar 14, 2024 pm 11:50 PM
Add SOTA in real time and skyrocket! FastOcc: Faster inference and deployment-friendly Occ algorithm is here!
Mar 14, 2024 pm 11:50 PM
Written above & The author’s personal understanding is that in the autonomous driving system, the perception task is a crucial component of the entire autonomous driving system. The main goal of the perception task is to enable autonomous vehicles to understand and perceive surrounding environmental elements, such as vehicles driving on the road, pedestrians on the roadside, obstacles encountered during driving, traffic signs on the road, etc., thereby helping downstream modules Make correct and reasonable decisions and actions. A vehicle with self-driving capabilities is usually equipped with different types of information collection sensors, such as surround-view camera sensors, lidar sensors, millimeter-wave radar sensors, etc., to ensure that the self-driving vehicle can accurately perceive and understand surrounding environment elements. , enabling autonomous vehicles to make correct decisions during autonomous driving. Head



