 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to restore all or part of the rules in an original security group to the rules of the target security group
How to restore all or part of the rules in an original security group to the rules of the target security group
How to restore all or part of the rules in an original security group to the rules of the target security group
The content of this article is about how to restore all or part of the rules in an original security group to the rules of the target security group. It has certain reference value. Friends in need can refer to it. I hope it will help You helped.
Restore security group rules
Restore security group rules refers to the process of restoring all or part of the rules in an original security group to the rules of the target security group. Among them:
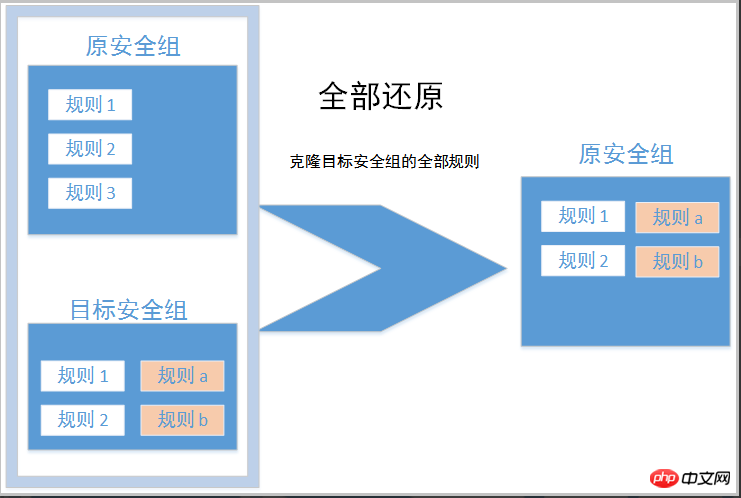
Restore all means that when restoring, the system deletes the rules in the original security group that are not in the target security group, and adds rules in the original security group that are only in the target security group. . After the restore operation, the rules in the original security group are exactly the same as those in the target security group.
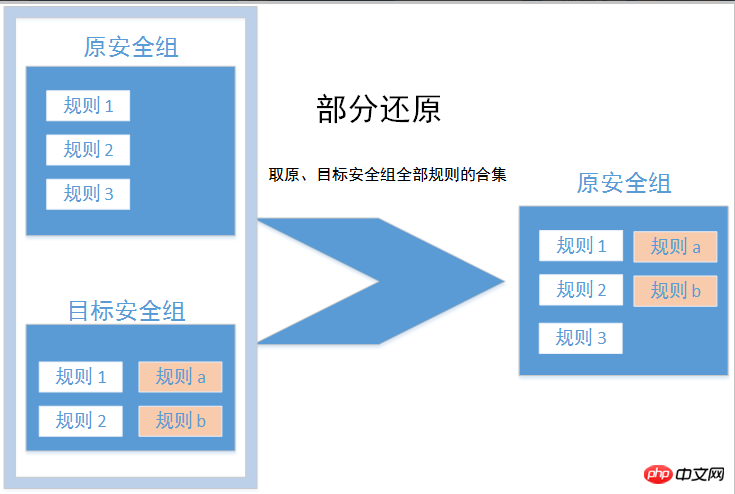
Partial restore means to add only the rules that are in the target security group to the original security group, ignoring the rules that are in the original security group but not in the target security group.
Restrictions
Currently the restore security group rules are as follows Restrictions:
The original security group and the target security group must be in the same region.
The original security group and the target security group must be of the same network type.
If there are system-level security group rules (priority 110) in the target security group, such rules cannot be created during restoration. After restoration, the rules in the original security group may be different from expected. If you need these security group rules, create similar rules manually (the priority can be set to 100).
Usage scenarios
If you need to implement new security group rules for an online business, you can first clone the original security group as a backup , and then modify the rules in the security group. If the new security group rules have an adverse impact on your online business, you can restore the security group rules in whole or in part.
Prerequisite
You should have at least one security group in the same region and the same network type.
Operation steps
Log in to the cloud server ECS management console.
In the left navigation bar, click Security Group.
Select a region.
In the security group list, find the security group whose rules need to be restored as the original security group. In the Operation column, click Restore Rules.
In the Restore Rules dialog box:
Select the target security group: The target security group must have different rules from the original security group.
Select Restore Strategy:
If you need the original security group and the target security group to have completely consistent rules, you should select Restore All.
If you only need to add rules to the original security group that are only available in the target security group, you should choose partial restore.

Preview the restoration results:
Shown in green are rules that only exist in the target security group. Regardless of whether it is a full restore or a partial restore, these rules will be added to the original security group.
Displayed in red are rules that are not in the target security group. If you choose to restore all, the system will delete these rules in the original security group. If you choose partial restore, this part of the rules in the original security group will still be retained.
After confirming that everything is correct, click OK.
After the creation is successful, the restore rules dialog box will automatically close. In the Security Group List, find the original security group that has just completed the restore operation. In the Operation column, click Configure Rules to enter the Security Group Rules page to view the updated security group rules.
The above is the detailed content of How to restore all or part of the rules in an original security group to the rules of the target security group. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1670
1670
 14
14
 1428
1428
 52
52
 1329
1329
 25
25
 1274
1274
 29
29
 1256
1256
 24
24
 Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
Linux Architecture: Unveiling the 5 Basic Components
Apr 20, 2025 am 12:04 AM
The five basic components of the Linux system are: 1. Kernel, 2. System library, 3. System utilities, 4. Graphical user interface, 5. Applications. The kernel manages hardware resources, the system library provides precompiled functions, system utilities are used for system management, the GUI provides visual interaction, and applications use these components to implement functions.
 vscode Previous Next Shortcut Key
Apr 15, 2025 pm 10:51 PM
vscode Previous Next Shortcut Key
Apr 15, 2025 pm 10:51 PM
VS Code One-step/Next step shortcut key usage: One-step (backward): Windows/Linux: Ctrl ←; macOS: Cmd ←Next step (forward): Windows/Linux: Ctrl →; macOS: Cmd →
 How to check the warehouse address of git
Apr 17, 2025 pm 01:54 PM
How to check the warehouse address of git
Apr 17, 2025 pm 01:54 PM
To view the Git repository address, perform the following steps: 1. Open the command line and navigate to the repository directory; 2. Run the "git remote -v" command; 3. View the repository name in the output and its corresponding address.
 How to run java code in notepad
Apr 16, 2025 pm 07:39 PM
How to run java code in notepad
Apr 16, 2025 pm 07:39 PM
Although Notepad cannot run Java code directly, it can be achieved by using other tools: using the command line compiler (javac) to generate a bytecode file (filename.class). Use the Java interpreter (java) to interpret bytecode, execute the code, and output the result.
 How to run sublime after writing the code
Apr 16, 2025 am 08:51 AM
How to run sublime after writing the code
Apr 16, 2025 am 08:51 AM
There are six ways to run code in Sublime: through hotkeys, menus, build systems, command lines, set default build systems, and custom build commands, and run individual files/projects by right-clicking on projects/files. The build system availability depends on the installation of Sublime Text.
 What is the main purpose of Linux?
Apr 16, 2025 am 12:19 AM
What is the main purpose of Linux?
Apr 16, 2025 am 12:19 AM
The main uses of Linux include: 1. Server operating system, 2. Embedded system, 3. Desktop operating system, 4. Development and testing environment. Linux excels in these areas, providing stability, security and efficient development tools.
 laravel installation code
Apr 18, 2025 pm 12:30 PM
laravel installation code
Apr 18, 2025 pm 12:30 PM
To install Laravel, follow these steps in sequence: Install Composer (for macOS/Linux and Windows) Install Laravel Installer Create a new project Start Service Access Application (URL: http://127.0.0.1:8000) Set up the database connection (if required)
 git software installation
Apr 17, 2025 am 11:57 AM
git software installation
Apr 17, 2025 am 11:57 AM
Installing Git software includes the following steps: Download the installation package and run the installation package to verify the installation configuration Git installation Git Bash (Windows only)



